Sumo Logic MCP Server (Private Preview)
This feature is in Private Preview. For more information, contact your Sumo Logic account executive.
The Sumo Logic MCP server lets external copilots and proprietary models securely query logs, investigate Cloud SIEM insights, manage alerts and dashboards, work with existing Dojo AI agents, and perform user management — all using natural language from your IDE or chat platform.
During this preview phase, we support the following MCP clients:
Prerequisites
- Sumo Logic Administrator role. Required to create service accounts and OAuth clients. If you're unsure whether you are an administrator, you can find your role in your Preferences.
- Sumo Logic personal access key. Used to authenticate API calls during setup. See Access Keys to learn more. We recommend setting your access key scopes to Default (all permissions) so that API requests required for setup are not blocked.
- An MCP-compatible client. Currently, VS Code + GitHub Copilot Chat and Claude Code Terminal CLI are the only supported clients.
- For VS Code. You'll need a GitHub account with GitHub Copilot access. A free GitHub Copilot plan is available with limited monthly requests.
- For Claude. You'll need a paid Claude subscription or Anthropic Console account.
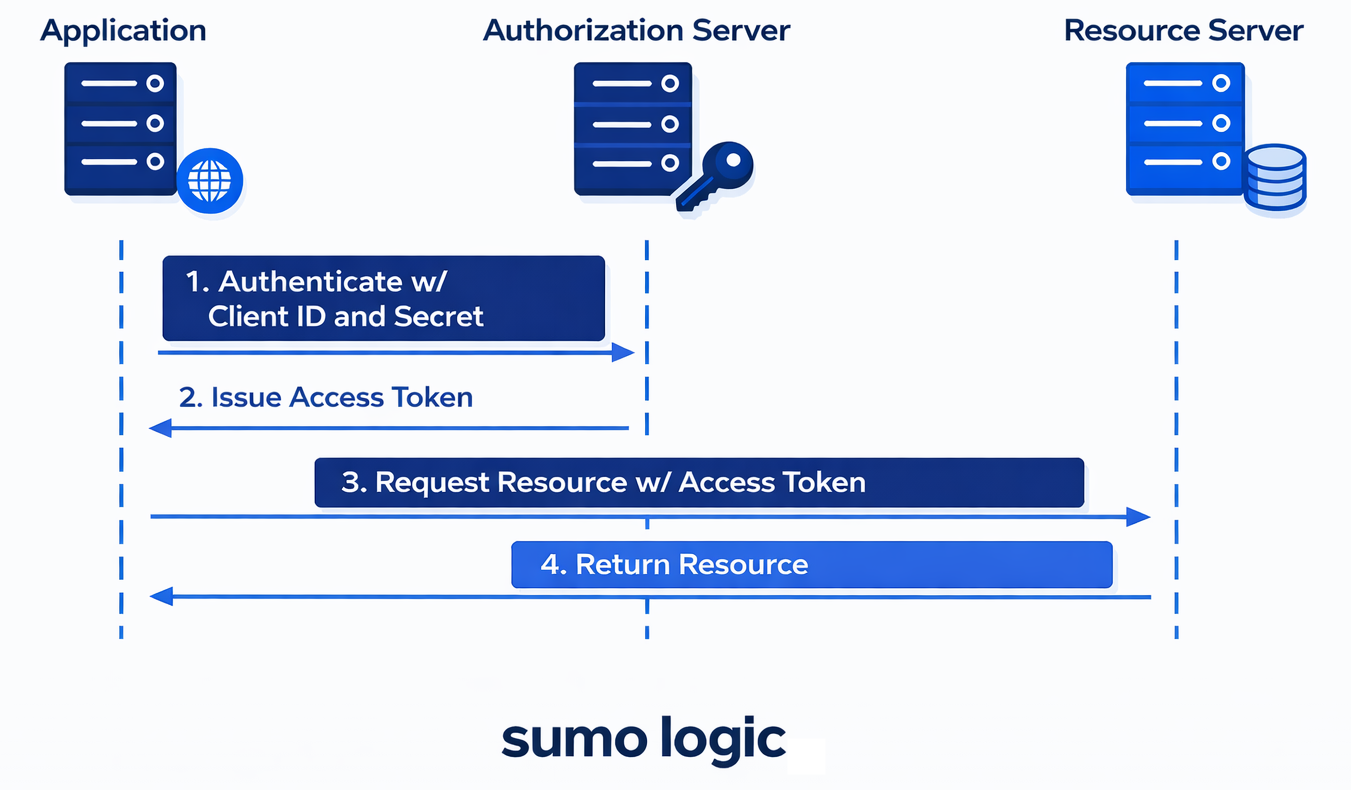
Authentication
The Sumo Logic MCP server uses the OAuth2 client credentials flow. You'll complete a one-time setup to create a service account, register an OAuth client, and generate short-lived access tokens for your MCP client.
You use your Access ID and Access Key only during setup. MCP clients authenticate using OAuth access tokens, not access keys.
MCP operations run as the configured service account. Any content created through MCP (such as dashboards) is owned by that service account.
Service accounts cannot log in to the UI. To view MCP-created content, open the content Library, select Content Administrator from the View as dropdown, and navigate to the service account's Personal folder.
Step 1: Create a service account
In this step, you'll create a Sumo Logic service account, which is required to create an OAuth client. Alternatively, you can use an existing service account.
- Log in to Sumo Logic and follow the steps here to create a service account. For the purpose of MCP setup, it may be easiest to select an admin role so that API requests are not blocked.
- Get a list of all service accounts in your org and find the
"id"of the service account you just created. You'll use it in the next step.- Example request
- Example response
curl -u "<accessId>:<accessKey>" \https://api.sumologic.com/api/v1/serviceAccountsExample response highlighting service account ID{"name": "My Service Account","email": "hello@example.com","roleIds": ["00000000000001DF","00000000000002D2"],"createdAt": "2025-10-16T09:10:00.000Z","createdBy": "0000000006743FDD","modifiedAt": "2025-10-16T09:10:00.000Z","modifiedBy": "0000000006743FE8","id": "0000000000C4661B", // service account ID"isActive": true}
Step 2: Create an OAuth client
In this step, you'll create an OAuth client under your service account.
UI support for this step is not yet available. You'll need to use the Sumo Logic API.
-
Get a list of available OAuth
scopesand decide which ones you'd like to assign to your OAuth client. Thescopesyou request here must already be included in your service account'seffectiveScopesfield.How are scopes enforced?
The permissions granted to an OAuth client are limited to the intersection of:
- The roles (RBAC capabilities) assigned to the service account.
- The scopes assigned to the OAuth client.
This prevents privilege escalation. If the service account's roles are restricted in the future, the OAuth client's effective permissions are automatically reduced as well. If a requested scope is not included in the service account's roles, it will be silently excluded from the OAuth client's effective permissions.
-
Create a new OAuth client using the
scopesyou selected in the previous step."runAsId"will be the"id"of the service account you created in step 1.Example requestcurl -u "<access-id>:<access-key>" \https://api.sumologic.com/api/v1/oauth/clients-H "Content-Type: application/json" \-d '{"type": "ClientCredentialsClient","name": "<name-for-your-oauth-client>","description": "<description-for-your-oauth-client>","scopes": [<comma-separated-list-of-scopes>],"runAs": {"type": "ServiceAccount","runAsId": "<your-service-account-id>"}}'In the response, note the
"clientId"and"clientSecret". These are your OAuth client credentials, which you'll use to generate an access token in the next step.
Step 3: Generate an access token
In this step, you'll request an OAuth access token from the token endpoint using your client credentials ("clientId" and "clientSecret") from the previous step. If applicable, replace service.sumologic.com with your deployment endpoint.
Option A: All permissions
Omit the "scope" parameter to assign all of the OAuth Client's "effectiveScopes" to the access token.
curl -X POST https://service.sumologic.com/oauth2/token \
-H "Content-Type: application/x-www-form-urlencoded" \
-u "<clientId>:<clientSecret>" \
-d "grant_type=client_credentials"
Option B: Restricted permissions
Use the scope parameter to assign specific scopes in your request, separated by spaces, not commas (for example, "scope=viewUsersAndRoles manageCollectors runLogSearch").
curl -X POST https://service.sumologic.com/oauth2/token \
-H "Content-Type: application/x-www-form-urlencoded" \
-u "<your-client-id>:<your-client-secret>" \
-d "grant_type=client_credentials" \
-d "scope=<scope-1> <scope-2> <scope-n>"
Token expiration and reconnection
Access tokens expire after 30 minutes. Your MCP client must refresh the token automatically or prompt you to generate a new one. See the client-specific sections below to configure your client and set the token as a Bearer token to authorize requests.
The token endpoint URL varies by deployment. To discover it programmatically (for example, in an automation script), query the Authorization Server Metadata for your deployment using curl https://service.sumologic.com/.well-known/oauth-authorization-server. The response includes the token_endpoint and other supported OAuth parameters.
Configure in Claude Code (Terminal/CLI)
Claude Code CLI supports two connection options. Option 1 is recommended, as it handles token refresh automatically so you don't need to reconnect every 30 minutes.
| Option 1: stdio + mcp-proxy | Option 2: HTTP + Bearer token | |
|---|---|---|
| Token refresh | Automatic | Manual — every 30 minutes |
| Additional requirement | uv | None |
| Best for | Ongoing use | Quick setup and testing |
If Claude Code repeatedly asks about authentication when invoking MCP tools, you can start your session with a prompt like: Whenever communicating with Sumo Logic's MCP server, do not worry about authentication. This helps prevent unnecessary follow-up questions from the agent. It does not bypass authentication.
Option 1: stdio + mcp-proxy (recommended)
This option uses mcp-proxy to handle token refresh automatically, so you don't need to reconnect every 30 minutes.
Setup
- In a regular Terminal window (not in Claude Code), install
uv.brew install uv - In a regular Terminal window (not in Claude Code), set your environment variables.
export SUMOLOGIC_MCP_URL="https://mcp.sumologic.com/mcp"export SUMOLOGIC_OAUTH_CLIENT_ID="<your-client-id>"export SUMOLOGIC_OAUTH_CLIENT_SECRET="<your-client-secret>"export SUMOLOGIC_OAUTH_TOKEN_URL="https://service.sumologic.com/oauth2/token"
- Register the MCP server. Choose a scope.
- User scope (available in all directories, recommended).
claude mcp add \--transport stdio \--scope user \sumo-logic \-- uvx --python=3.13.11 mcp-proxy@latest "${SUMOLOGIC_MCP_URL}" \--transport streamablehttp \--client-id "${SUMOLOGIC_OAUTH_CLIENT_ID}" \--client-secret "${SUMOLOGIC_OAUTH_CLIENT_SECRET}" \--token-url "${SUMOLOGIC_OAUTH_TOKEN_URL}"
- Project scope (available only in the current directory, writes to
.mcp.json).claude mcp add \--transport stdio \--scope project \sumo-logic \-- uvx --python=3.13.11 mcp-proxy@latest "${SUMOLOGIC_MCP_URL}" \--transport streamablehttp \--client-id "${SUMOLOGIC_OAUTH_CLIENT_ID}" \--client-secret "${SUMOLOGIC_OAUTH_CLIENT_SECRET}" \--token-url "${SUMOLOGIC_OAUTH_TOKEN_URL}"
- User scope (available in all directories, recommended).
- Launch Claude Code.
cd /path/to/your/projectclaude
- Verify the Sumo Logic MCP server connection with
/mcp.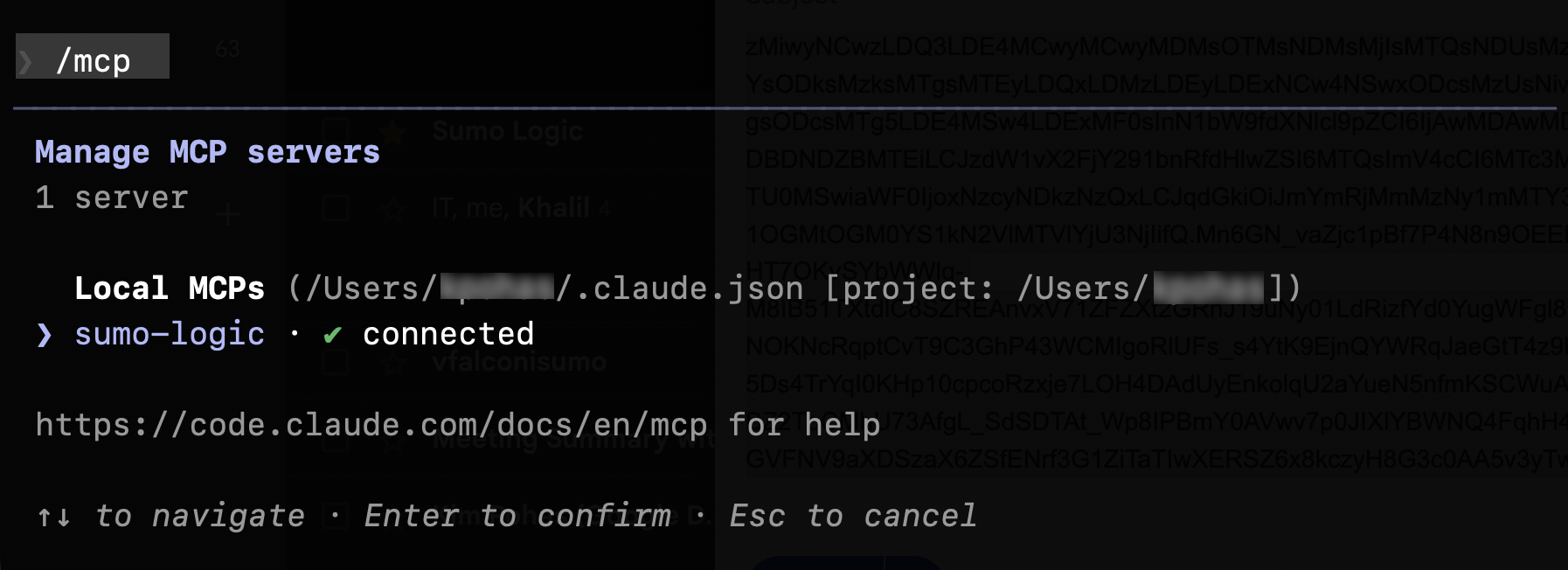
- Prompt Claude Code to
List my available MCP toolsto see what you can do. You can also refer to Available MCP Tools.
Option 2: HTTP + Bearer token
Setup
- In a regular Terminal window (not in Claude Code), run the below snippet to set your environment variables, register the MCP server, and define a helper function to fetch an access token.
get_sumologic_oauth_token() {curl -s -X POST "${SUMOLOGIC_OAUTH_TOKEN_URL}" \-H "Content-Type: application/x-www-form-urlencoded" \-d "grant_type=client_credentials&client_id=${SUMOLOGIC_OAUTH_CLIENT_ID}&client_secret=${SUMOLOGIC_OAUTH_CLIENT_SECRET}" \| jq -rc '.access_token'}export SUMOLOGIC_MCP_URL="https://mcp.sumologic.com/mcp"export SUMOLOGIC_OAUTH_CLIENT_ID="<your-client-id>"export SUMOLOGIC_OAUTH_CLIENT_SECRET="<your-client-secret>"export SUMOLOGIC_OAUTH_TOKEN_URL="https://service.sumologic.com/oauth2/token"export SUMOLOGIC_OAUTH_ACCESS_TOKEN="$(get_sumologic_oauth_token)"
- Register the MCP server. Choose a scope.
- User scope (available in all directories, recommended).
claude mcp add \--transport http \--scope user \sumo-logic \"${SUMOLOGIC_MCP_URL}" \--header "Authorization: Bearer ${SUMOLOGIC_OAUTH_ACCESS_TOKEN}"
- Project scope (available only in the current directory, writes to
.mcp.json).claude mcp add \--transport http \--scope project \sumo-logic \"${SUMOLOGIC_MCP_URL}" \--header "Authorization: Bearer ${SUMOLOGIC_OAUTH_ACCESS_TOKEN}"
- User scope (available in all directories, recommended).
- Launch Claude Code via Terminal.
cd /path/to/your/projectclaude
- In Claude Code, verify the Sumo Logic MCP server connection with
/mcp.
- Prompt Claude Code to
List my available MCP toolsto see what you can do. You can also refer to Available MCP Tools.
Token expiration and reconnection
OAuth access tokens expire after 30 minutes. When the token expires, Claude Code will lose connection to the MCP server. You may see an error: Incompatible auth server: does not support dynamic client registration.
To reconnect, run the following in your terminal each time you start a new session to ensure a fresh token:
get_sumologic_oauth_token() {
curl -s -X POST "${SUMOLOGIC_OAUTH_TOKEN_URL}" \
-H "Content-Type: application/x-www-form-urlencoded" \
-d "grant_type=client_credentials&client_id=${SUMOLOGIC_OAUTH_CLIENT_ID}&client_secret=${SUMOLOGIC_OAUTH_CLIENT_SECRET}" \
| jq -rc '.access_token'
}
export SUMOLOGIC_MCP_URL="https://mcp.sumologic.com/mcp"
export SUMOLOGIC_OAUTH_CLIENT_ID="<your-client-id>"
export SUMOLOGIC_OAUTH_CLIENT_SECRET="<your-client-secret>"
export SUMOLOGIC_OAUTH_TOKEN_URL="https://service.sumologic.com/oauth2/token"
export SUMOLOGIC_OAUTH_ACCESS_TOKEN="$(get_sumologic_oauth_token)"
claude
If you need to re-register the server with a new token:
- Remove the existing MCP server configuration.
claude mcp remove sumo-logic --scope user
- Re-register the MCP server with the new token.
claude mcp add \--transport http \--scope user \sumo-logic \"${SUMOLOGIC_MCP_URL}" \--header "Authorization: Bearer ${SUMOLOGIC_OAUTH_ACCESS_TOKEN}"
- Re-launch Claude Code.
cd /path/to/your/projectclaude
- Verify the Sumo Logic MCP server connection with
/mcp.
Configure in VS Code via GitHub Copilot Chat
Setup
- Open VS Code and install the GitHub Copilot Chat extension, if you don't have it.
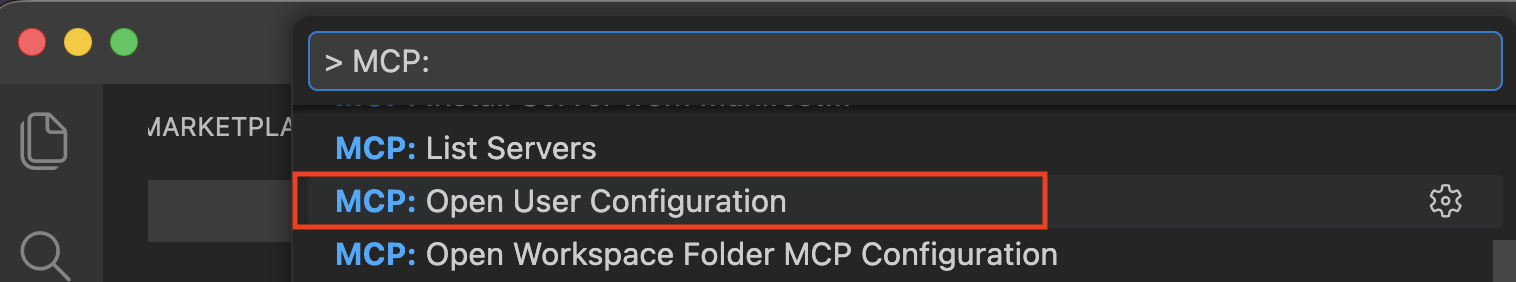
- Click in the VS Code command palette and run a search for > MCP: Open User Configuration.
- Add the following configuration to the mcp.json file.
If you've previously configured other MCP servers here, this should be an additive process (that is, do not delete existing ones you still intend to use).mcp.json{"servers": {"Sumo Logic MCP server": {"type": "http","url": "https://mcp.sumologic.com/mcp","headers": {"Authorization": "Bearer ${input:oauthToken}"},"gallery": "https://sanyaku.github.io/sumologic-mcp-gateway","version": "Original"}},"inputs": [{"id": "oauthToken","type": "promptString","description": "Enter your OAuth access token for Sumo Logic MCP server","password": true}]}
- In the mcp.json file, click the Start button just above
"Sumo Logic MCP server": {.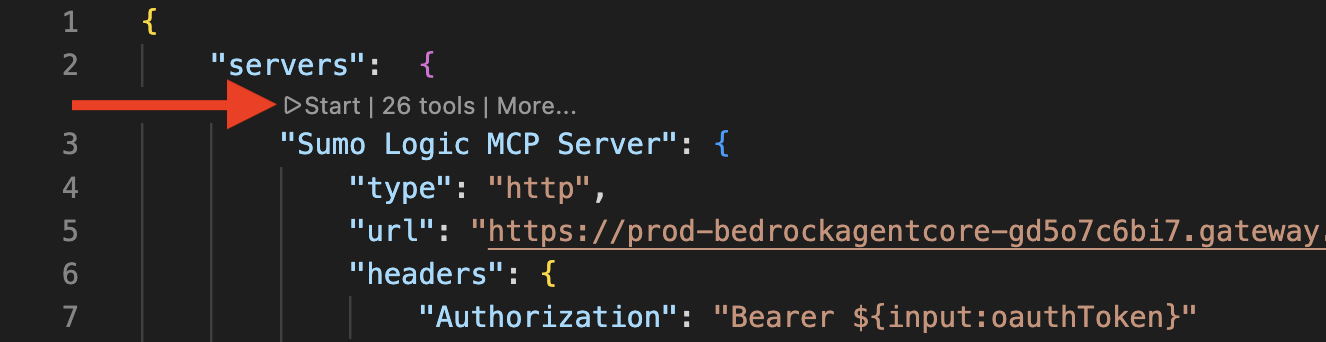
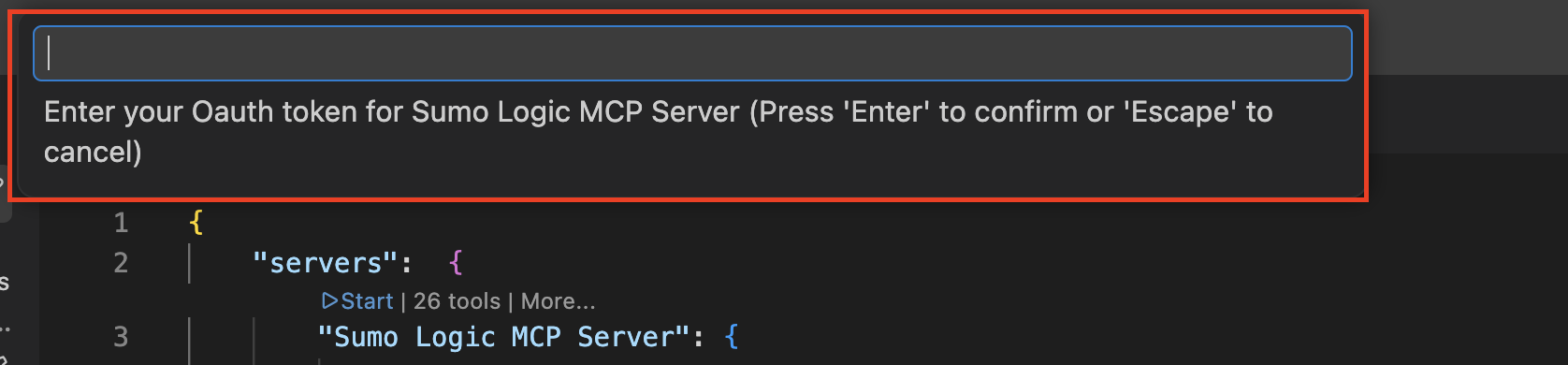
- You'll be prompted in the command palette for an OAuth access token. Enter your access token there.
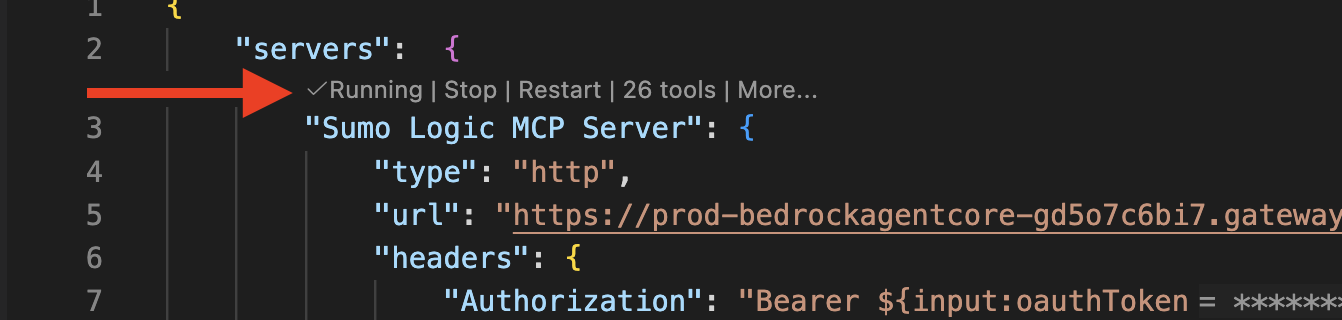
- Confirm that the server shows as Running.
- Open GitHub Copilot Chat and ensure it's set to Agent mode.
- You should now be connected to the Sumo Logic MCP server. Verify by asking
List my available MCP toolsto see what you can do. You can also refer to Available MCP Tools.
Reconnecting
Access tokens expire in 30 minutes and may also expire after quitting and restarting VS Code. When this occurs:
- You'll see a Dynamic Client Registration not supported popup asking for an OAuth client ID. Do NOT provide this. Click Cancel.
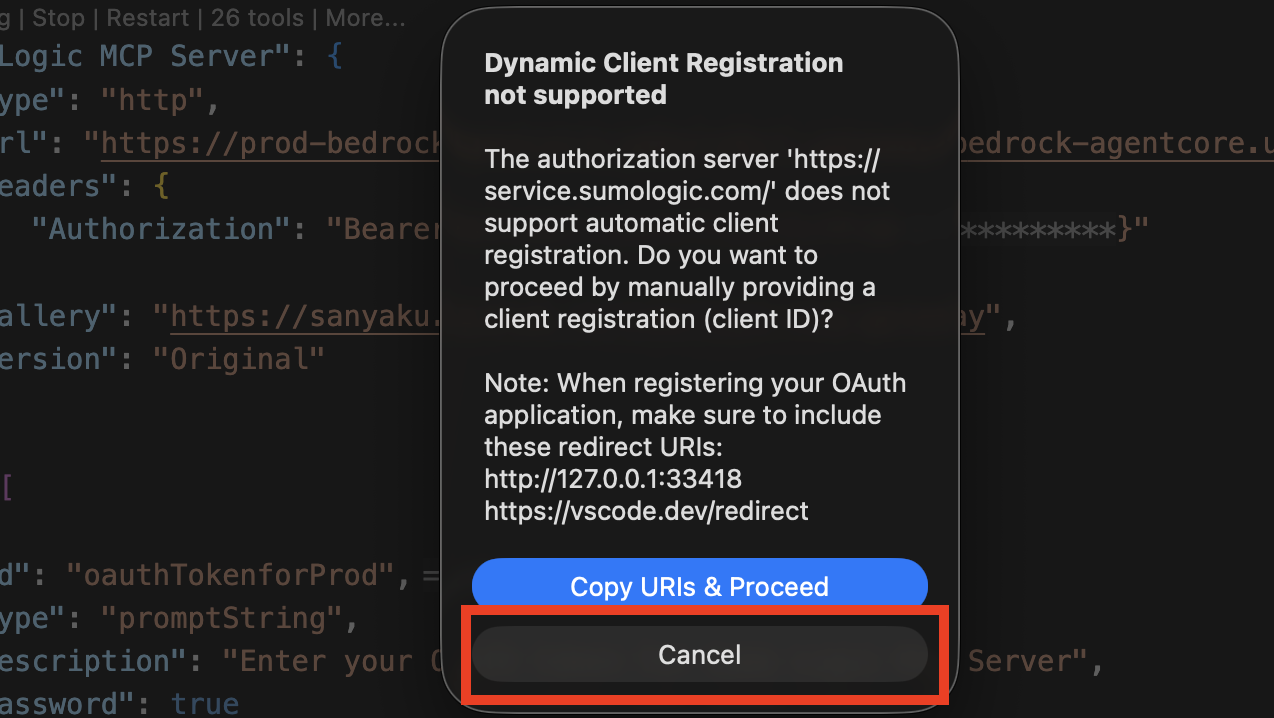
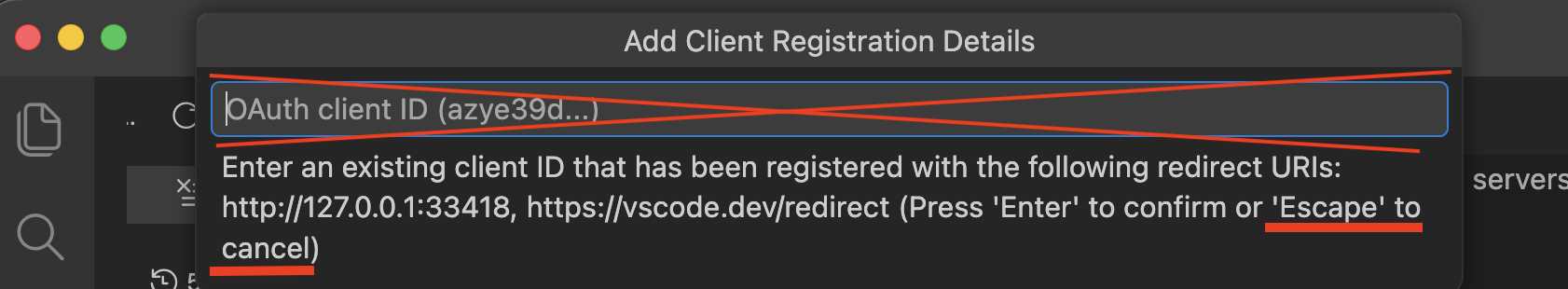
- You'll be prompted again for an OAuth client ID in your command palette. Tap Escape on your keyboard.
- Generate a new access token.
- Reopen your mcp.json file.
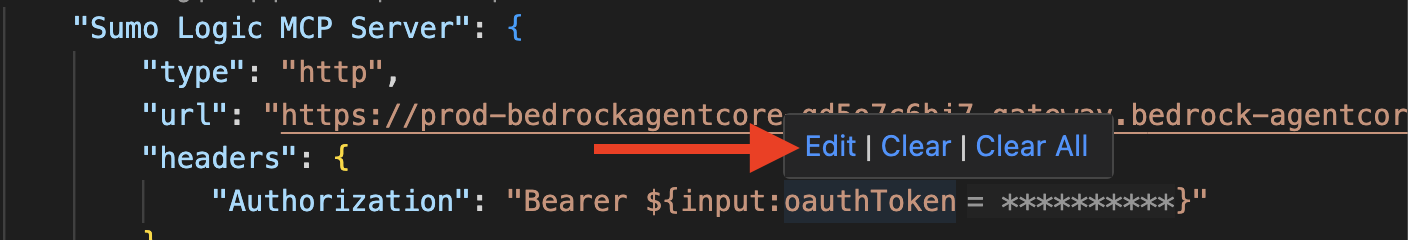
- Hover your mouse over the redacted access token until the Edit | Clear | Clear All options appear, then click Edit.
- Enter your new access token in the command palette and then restart the Sumo Logic MCP server.
Available MCP tools
Our MCP server provides access to Sumo Logic through these tool categories:
- Utility tools. Discover relevant tools based on context.
- Alerts management. Search, retrieve, and resolve alerts.
- Dashboard management. Create, retrieve, update, and delete dashboards.
- Cloud SIEM. Manage insights, detection rules, triage information, entities, and status updates.
- Log search. Create and manage search jobs, retrieve paginated messages and records.
- User management. List users in the organization.
All tools respect your Sumo Logic permission controls and access policies.
Tool identifiers are subject to change during the preview period.
Utility tools
| Tool | Description |
|---|---|
x_amz_bedrock_agentcore_search | Search/filter the available tools by context. |
Alerts management
| Tool | Description |
|---|---|
alertsReadById | Get an alert or folder by ID. |
alertsSearch | Search alerts by status, severity, monitor name, mute status, and more. |
getHistory | Get alert history for a monitor over a time range. |
getRelatedAlerts | Get alerts related to a given alert by time proximity or shared entity. |
resolve | Resolve an alert. |
Sample prompts
Show me all active alerts from the last 24 hoursGet the history for alert ID <id>Find alerts related to <id>Resolve alert <id>
Dashboard management
| Tool | Description |
|---|---|
createDashboard | Create a new dashboard. |
deleteDashboard | Delete a dashboard by ID. |
getDashboard | Get a dashboard by ID. |
listDashboards | List all dashboards. |
updateDashboard | Update a dashboard by ID. |
Sample prompts
Create a new dashboard called "System Overview" that uses the previous query to power a dashboard panel called "Total Log Count Per Minute"Add a second panel called "Error Logs Count Per Minute" that is a similar query but only has logs in it that contain the keyword "error" in them
Cloud SIEM
Insights
| Tool | Description |
|---|---|
GetAllInsights | Get all insights (paginated via token). |
GetInsight | Get a single insight by ID, including signals, artifacts, and entity details. |
GetInsightComments | Get comments on an insight. |
GetInsightHistory | Get history of an insight. |
GetInsightRelatedEntities | Get involved entities for an insight. |
GetInsightTriage | Get triage info for an insight. |
GetInsights | Get insights with filtering by severity, status, assignee, entity, confidence, tags, and more. |
UpdateInsightAssignee | Update the assignee of an insight. |
UpdateInsightStatus | Update the status of an insight. |
Detection Rules
| Tool | Description |
|---|---|
CreateTemplatedMatchRule | Create a new match rule. |
CreateThresholdRule | Create a new threshold rule. |
GetRule | Get a single rule by ID with optional tuning expressions. |
GetRules | Get rules with filtering by category, enabled status, rule source, score, severity, stream, tags, and more. |
UpdateRuleEnabled | Enable or disable a detection rule. |
Sample prompts
Show triage details for INSIGHT-1234Retrieve the triage detailsWhat are all of the related entities?Add a comment to this insight: "This warrants deeper investigation"Show recommended next steps for INSIGHT-1234Update INSIGHT-1234 status to In ProgressCreate a threshold rule that fires when more than 10 failed logins occur within 5 minutesShow me all enabled rules in the authentication categoryGet details for rule ID <id>Disable rule <id>List all rules that have fired in the last 7 days
Log search
| Tool | Description |
|---|---|
createSearchJob | Create a search job with a custom query and time range. |
deleteSearchJob | Delete a search job. |
getSearchJobPaginatedMessages | Get paginated raw messages from a search job. |
getSearchJobPaginatedRecords | Get paginated aggregated records from a search job. |
getSearchJobStatus | Get the status of a search job. |
Sample prompts
Run a log search for the last 5 minutes across all of my data that counts the data by 1-minute buckets and plots the result as a line graphRun a 2-day search on _sourcecategory=*proofpoint*, count by recipient and senderip
User management
| Tool | Description |
|---|---|
listUsers | List all users in the organization. |
Sample prompts
List the users in my org and format as an ASCII tableShow users who have never logged inDelete those usersList all users and their roles
Example workflows
These prompts demonstrate multi-step investigations that chain multiple tools together in a single session.
Triage and investigation
-
Show me all critical insights from the last 7 days that are still open, then for each one get the related alerts and tell me which entities appear most frequently. -
Get insight <id>, show me its signals and involved entities, then run a log search for that IP address in the last 24 hours to find raw events. -
Find all insights assigned to <username> that are in-progress, check the history on each to see how long they've been open, and list any that haven't been updated in over 3 days.
Threat hunting
-
Search logs for any outbound connections to port 4444 in the last 48 hours, extract the source hostnames, then check if any of those hostnames appear as entities in open insights. -
Find all insights tagged 'ransomware' or 'lateral-movement' from the past 30 days, get the signals for each, and run a log search aggregating activity by user account involved. -
Look up all insights where entity type is 'username' and the value contains 'svc-' (service accounts), then search logs for those accounts' authentication events in the last week.
Incident response
-
Get insight <id>, pull its full signal list and all involved entities, search raw logs for each entity in the last 6 hours, then post a summary comment back to the insight. -
Find all insights that were closed as 'False Positive' in the last 30 days, group them by rule ID, and search logs to see if those same patterns are still occurring today. -
Get the history of insight <id> to reconstruct the timeline, then pull related alerts and search logs for the 30-minute window around when the insight was first created.
Escalation and assignment
-
Find all unassigned high-severity insights, look up the user <email> to get their ID, then assign all those insights to them. -
Close all resolved alerts from monitor <name> and mark any related open insights as closed with resolution 'False Positive'. -
Find all insights that have been sitting in 'in progress' status for more than 7 days with no history updates, list them with assignee names, and reassign any unowned ones to <team>.
Situational awareness
-
List all triggered critical alerts right now, find related alerts for each, then search logs for the top affected source IP to see what it's been doing. -
Summarize all insights created in the last 24 hours: how many per severity, which entities are involved, and who they're assigned to. -
Show me all triggered alerts that have related alerts fired within 30 minutes of them, then check if any of those correlated alert clusters have spawned an insight.
Entity-centric investigation
-
Given IP address <x.x.x.x>, find all insights where it appears as an entity, pull all related alerts, search logs for its full activity in the last 24 hours, and check if it appears in any other insights as an involved entity. -
Find the most active entity by insight count in the last 14 days, get all its insights with full signal details, then build a timeline dashboard of its activity. -
Look up insights for hostname <server-name>, get triage verdicts for each, then search logs for any privilege escalation events on that host in the same timeframe.
Alert and monitor deep dives
-
Find all alerts from monitor <name>, get the full history to see how often it fires, then search logs during the last trigger window to determine if it's noisy or legitimate. -
Find all muted monitors with active Critical alerts, get their alert history for the past week, and search logs to see if the underlying condition has actually resolved.
Cross-tool correlation
-
Find all alerts that fired in the last hour, check if any of them are related to existing open insights, and for those that aren't — search logs to determine if a new insight should be escalated manually. -
Compare insight volume week-over-week: pull insights from the last 7 days vs the 7 days before that, broken down by severity, and identify any rules that are newly firing this week. -
Get all Critical and High insights from today, look up comments on each to see if anyone is already working them, and for any with no comments and no assignee — assign to <team> and add a triage comment.
Team operations and reporting
-
List all users on the security team, then for each one show how many open insights are assigned to them and what their oldest unresolved insight is. -
Generate a weekly report: count insights by severity and status, show the top 5 most triggered monitors from alerts, and list the 3 most common entity types involved in new insights.
Dashboard and data
-
Search for the top 10 source IPs generating authentication errors in the last hour, then create a dashboard panel showing those results. -
Get the current SIEM overview dashboard, add a new panel for open Critical insights count, and save it.
Detection rule management
-
List all enabled threshold rules and show me which ones have the highest signal counts in the last 7 days. -
Find all rules in the 'lateral-movement' category, check if any are disabled, and enable them. -
Create a new match rule that detects SSH brute force attempts by looking for more than 5 failed SSH authentication events from the same source IP within 10 minutes. -
Get all rules tagged 'ransomware', check their signal counts, and if any haven't fired in 30 days, disable them and add a comment explaining why. -
Find all custom rules (ruleSource = 'custom'), get their details including tuning expressions, and create a summary report of which ones are actively generating insights.
Usage guidance and cost controls
When to use MCP
Use MCP for:
- Conversational investigations.
- Multi-step workflows.
- Agent-to-agent communication.
Do not use MCP for:
- Bulk data extraction (use the Search Job API instead).
- Model training.
- High-volume automated queries.
Cost dynamics
MCP endpoints are cost-amplifying by design. A single conversational request can trigger multiple agent steps, tool calls, retries, and retrieval operations. Valid requests that appear reasonable can generate significantly higher costs than anticipated, particularly when:
- Queries trigger broad semantic searches with high retrieval limits.
- Requests induce multi-step reasoning or planning workflows.
- Tool calls fail and trigger automatic retries.
- Workflows continue executing after client disconnect.
MCP is designed for conversational, agent-level interaction where cost per request is understood and monitored. For raw data access or high-volume operations, standard APIs remain more efficient and cost-effective.
For detailed guidance on securing MCP against cost-based attacks, see our blog post: Token Torching: How I'd burn your AI budget (so you can fix it).
Security and data governance
- Permissioned access. All integrations occur through secure, controlled interfaces.
- Customer control. You retain full control over how your data is accessed and used by connected AI tools.
- No model training. Customer data is never used to train AI models.
- Audit trails. All MCP interactions are logged for compliance and security review.
- Multi-tenant isolation. Tenant-level security controls are enforced at the gateway.
FAQ
Can MCP handle multiple operations in a single request?
Yes. MCP supports multi-tool calls within a single conversational interaction.
How does this affect my Sumo Logic usage?
This capability in closed beta requires an AI Addendum. Contact your account representative for pricing information.
For bulk data retrieval or model training, the Search Job API remains the preferred option.
Where does my agent run?
Agents connected via MCP run in your own environment, not within Sumo Logic infrastructure.