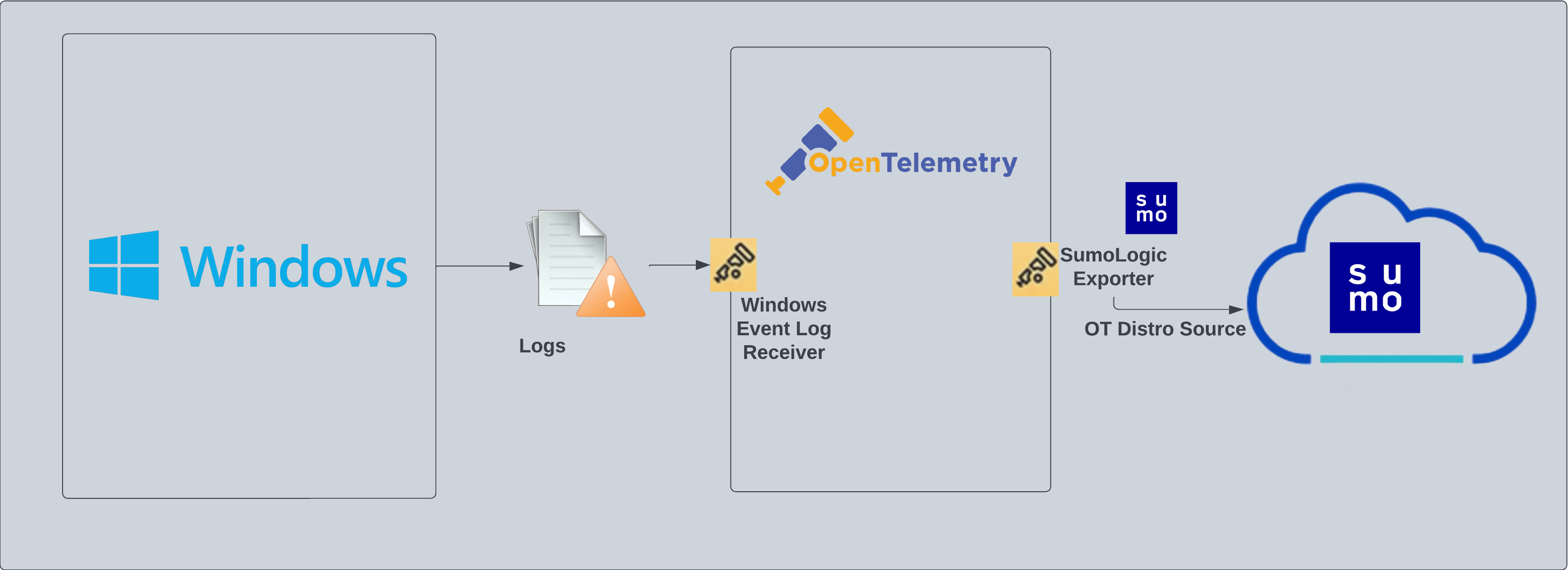
Windows - Cloud Security Monitoring and Analytics - OpenTelemetry

Windows - Cloud Security Monitoring and Analytics - OpenTelemetry is a unified log app that ingests distribution of Windows data to Sumo Logic via OpenTelemetry filelog receiver. The app's preconfigured dashboards provide insight into user accounts, login activity, and Windows updates.
Fields created in Sumo Logic for Windows
The following tag will be created as part of Windows app installation, if not already present.
sumo.datasource. Has a fixed value of windows.host.group. User configured tag which signifies a group of hosts for the operating system.deployment.environment. User configured tag which identifies the environment where the windows system resides. For example: dev, prod or qa.
Log types
The Windows app assumes events are coming from the Windows Event Log receiver in JSON format. It does not work with third party logs.
Standard Windows event channels include:
- Security
- System
Collection configuration and app installation
- You can skip this section if you have already set up the logs collection through Windows PCI or Windows or Active Directory app installation. Additional collection is not required as the logs used by this app are already ingested into Sumo Logic.
Follow these steps to set up and deploy the source template to collect data in Sumo Logic from a remotely managed OpenTelemetry collector.
Step 1: Set up remotely managed OpenTelemetry collector
If you want to configure your source locally, you can do so by downloading the YAML file. For details, see Configure OpenTelemetry collectors locally.
In this step, we'll install remotely managed OpenTelemetry collector and add a uniquely identifiable tag to these collectors.
- Classic UI. In the main Sumo Logic menu, Select App Catalog.
New UI. In the Sumo Logic main menu select App Catalog. - In the 🔎 Search Apps field, run a search for your desired OpenTelemetry app, then select it. For example, Apache - OpenTelemetry.
- Click the Manage dropdown and then select Add Collection.
- On the Set Up Collector page, select Add a New Collector and then click Next.
If you want to use an existing OpenTelemetry Collector, you can skip this step by selecting the Use an existing Collector option.
- Select the platform where you want to install the Sumo Logic OpenTelemetry Collector. For example, Linux.
This will generate a command that you can execute in the machine environment you need to monitor. Once executed, it will install the Sumo Logic OpenTelemetry Collector.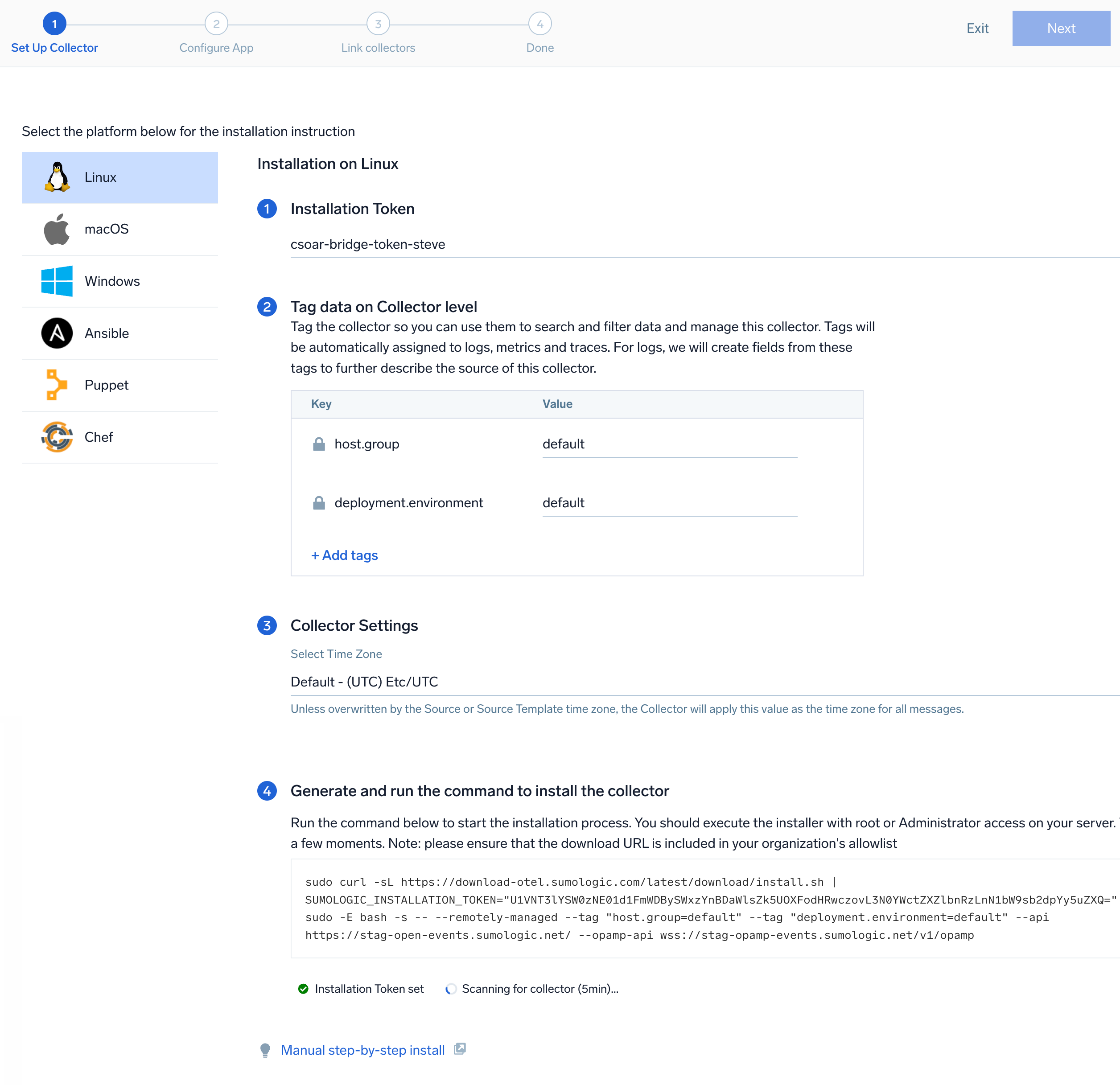 The installation commands now include a
The installation commands now include a --remotely-managedflag. When this flag is used, a remotely managed collector is installed automatically instead of a locally managed one. If you prefer to use a locally managed collector, simply remove the flag from the installation command.
Step 2: Configure the source template
In this step, you will configure the YAML required for Windows collection. Below are the inputs required for configuration:
- Name. Name of the source template.
- Description. Description for the source template.
Logs collection
- Fields/Metadata. You can provide any customer fields to be tagged with the data collected. By default, Sumo Logic tags
_sourceCategorywith the valueotel/windows. - Windows Event. In this section you can select choose among the most widely used Windows event channel for which Windows event log collection will be enabled. You can also provide Custom Event Channels providing any customer event channel for which event logs are to be collected.
- Forward to SIEM. Check the checkbox to forward your data to Cloud SIEM.
Metrics collection
- Metrics. Select the metric scrappers you want to enable. By default, metric collection for CPU, memory, disk, load, file system, network and paging are enabled, and process metric collection is disabled.
Enable process metric collection (optional)
By default, the collector will not send process metrics to Sumo Logic. This is because the number of processes running on a host can be very large, which would result in a significant increase in Data Points per Minute (DPM).
Click the Enable process metric collection checkbox to collect process-level metrics.
- Name of process. Add the list of process names.
- Include/Exclude the above pattern. Signifies if you want to exclude or include the metrics for the processes listed previously.
- Match type for process name. Select if the process name given should be considered for a strict match with the host machine processes or if it should be considered as regex when matching.
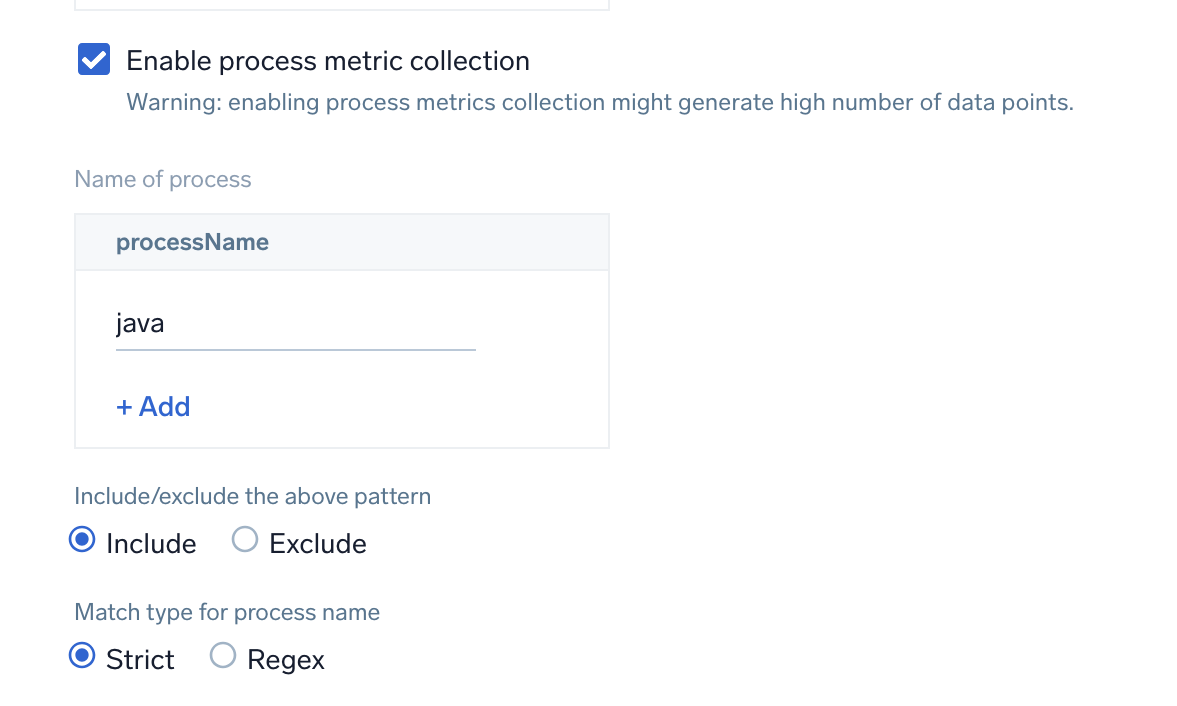
If you need to edit the process list in the future, you can do this manually in the OTEL config yaml by adding or removing in the names list under process scrapper.
process:
include:
names: [ <process name1>, <process name2> ... ]
match_type: <strict|regexp>
- Scan Interval. The frequency at which the source is scanned.
- Processing Rules. You can add processing rules for logs/metrics collected. To learn more, refer to Processing Rules. For masking windows event logs, refer to Mask Rules for Windows Source Template.
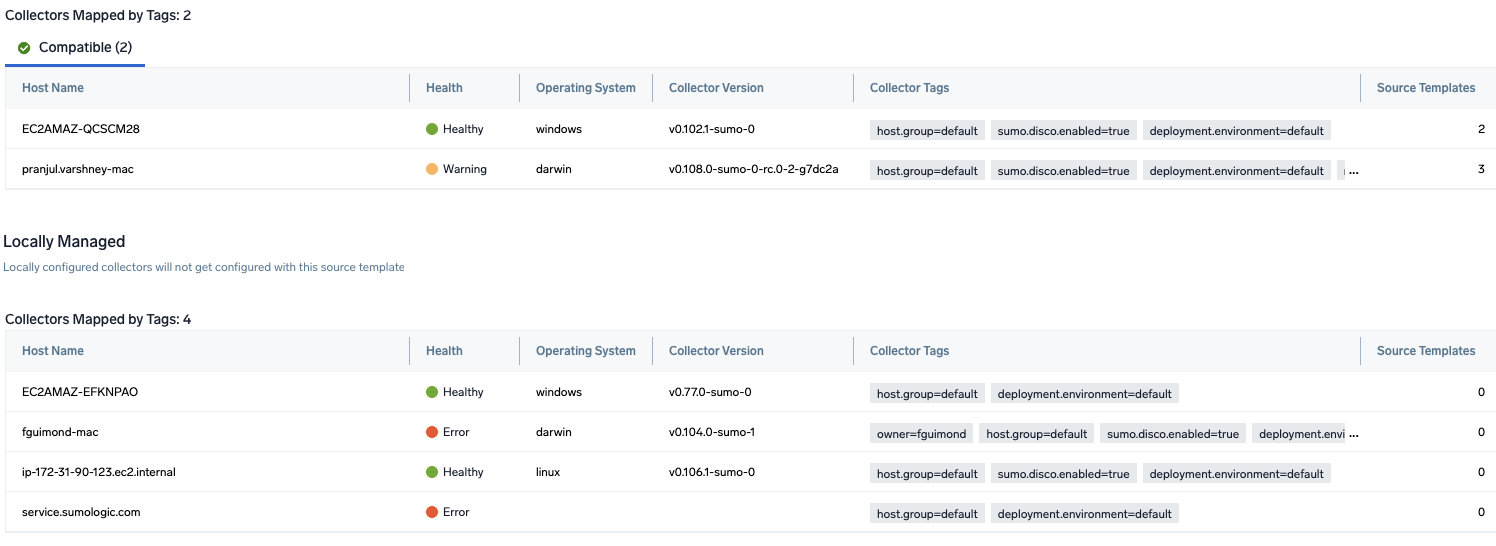
Step 3: Push the source template to the desired remotely managed collectors
A new source template will always be created with the latest version of the source template.
Follow the below steps to create a data collection configuration to gather the required logs and link them to all the collectors with the help of collector tags.
- Complete the source template form with the name and file path for your logs (for example, error logs or access logs), then click Next.
- Under Link Collectors, you will have the option to link the collectors using the collector name or by adding tags to find the group of collectors (for example,
application = Apache).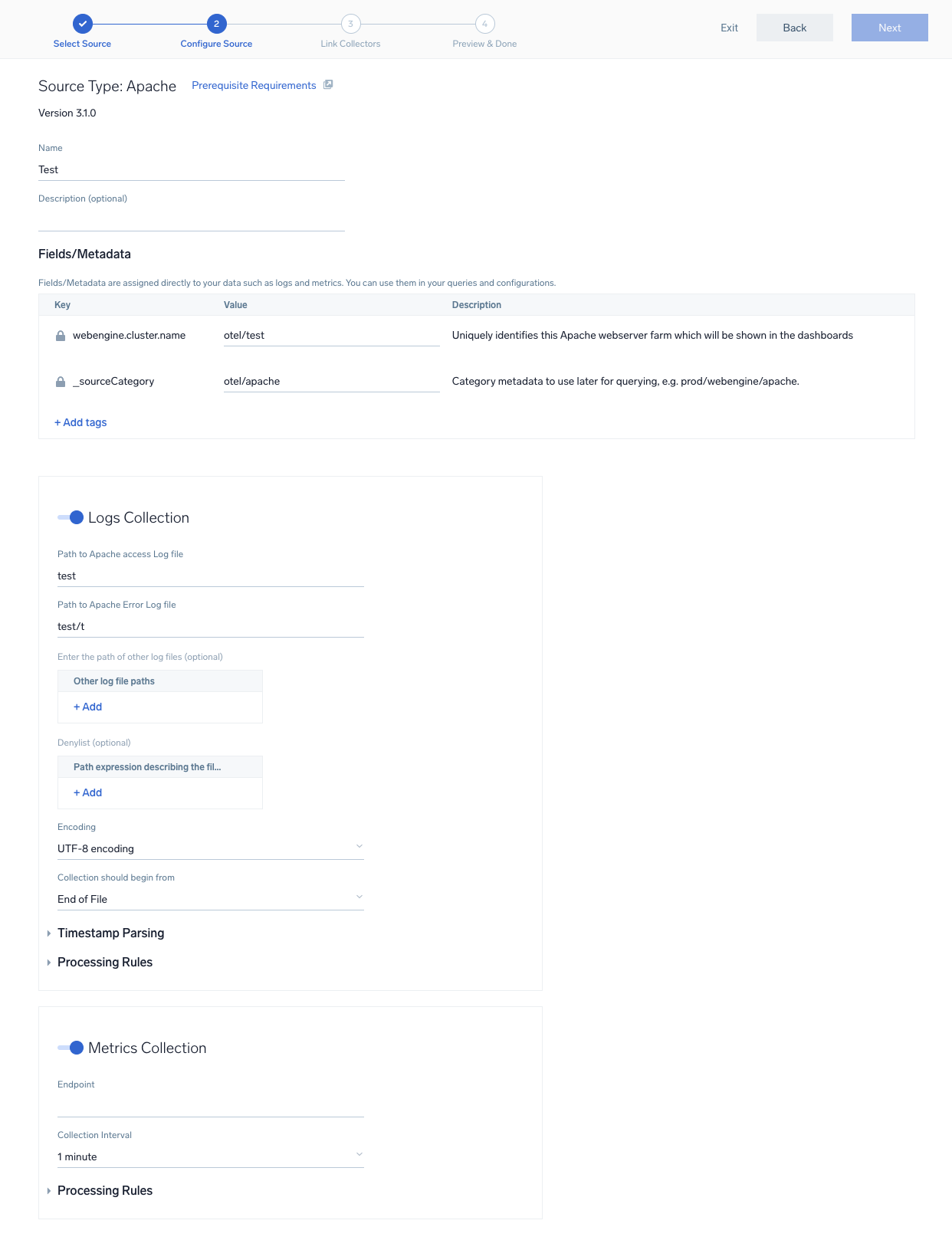
- Preview and confirm the collectors that will be linked (fetched automatically) to the newly created source template.
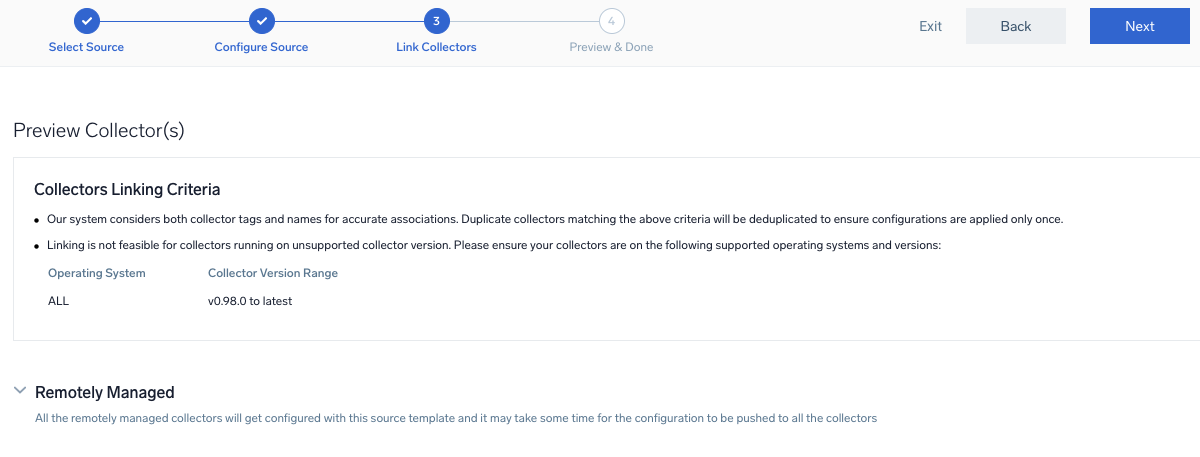
- Click Next to complete the source template creation. In the background, the system will apply the configuration to all the linked collectors and will start collecting the respective telemetry data from the remote host (in the example, it would start collecting Apache error logs).
- Click the Log Search or Metrics Search icons to search for and analyze your data collected for this source template.
Sample log messages
{
"record_id":161812,
"channel":"Security",
"event_data":{
"WorkstationName":"-",
"TargetDomainName":"",
"SubjectUserSid":"S-1-0-0",
"LogonProcessName":"NtLmSsp ",
"TargetUserName":"ADMINISTRATOR",
"TargetUserSid":"S-1-0-0",
"IpAddress":"3.137.149.192",
"ProcessId":"0x0",
"KeyLength":"0",
"ProcessName":"-",
"SubjectUserName":"-",
"LogonType":"3",
"TransmittedServices":"-",
"FailureReason":"%%2313",
"SubjectLogonId":"0x0",
"IpPort":"0",
"AuthenticationPackageName":"NTLM",
"Status":"0xc000006d",
"LmPackageName":"-",
"SubStatus":"0xc000006a",
"SubjectDomainName":"-"
},
"task":"Logon",
"provider":{
"name":"Microsoft-Windows-Security-Auditing",
"guid":"{54849625-5478-4994-a5ba-3e3b0328c30d}",
"event_source":""
},
"system_time":"2023-07-11T14:14:51.1731050Z",
"computer":"EC2AMAZ-V57A85N",
"opcode":"Info",
"keywords":[
"Audit Failure"
],
"details":{
"Account For Which Logon Failed":{
"Security ID":"S-1-0-0",
"Account Name":"ADMINISTRATOR",
"Account Domain":"-"
},
"Network Information":{
"Workstation Name":"-",
"Source Network Address":"3.137.149.192",
"Source Port":"0"
},
"Failure Information":{
"Failure Reason":"Unknown user name or bad password.",
"Status":"0xC000006D",
"Sub Status":"0xC000006A"
},
"Detailed Authentication Information":{
"Transited Services":"-",
"Key Length":"0",
"Logon Process":"NtLmSsp",
"Authentication Package":"NTLM",
"Package Name (NTLM only)":"-"
},
"Subject":{
"Security ID":"S-1-0-0",
"Account Name":"-",
"Account Domain":"-",
"Logon ID":"0x0"
},
"Process Information":{
"Caller Process ID":"0x0",
"Caller Process Name":"-"
},
"Logon Type":"3",
"Additional Context":[
"This event is generated when a logon request fails. It is generated on the computer where access was attempted.",
"The Subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.",
"The Logon Type field indicates the kind of logon that was requested. The most common types are 2 (interactive) and 3 (network).",
"The Process Information fields indicate which account and process on the system requested the logon.",
"The Network Information fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.",
"The authentication information fields provide detailed information about this specific logon request.",
"- Transited services indicate which intermediate services have participated in this logon request.",
"- Package name indicates which sub-protocol was used among the NTLM protocols.",
"- Key length indicates the length of the generated session key. This will be 0 if no session key was requested."
]
},
"message":"An account failed to log on.",
"event_id":{
"qualifiers":0,
"id":4625
},
"level":"Information"
}
Sample queries
This sample log query is from the Windows - Security Analytics - User Account Changes dashboard > Failed Logins Summary panel.
sumo.datasource=windows "Microsoft-Windows-Security-Auditing" ("4770" OR "4771" OR "4772" OR "4776" OR "4777" OR "4768" OR "4769" OR "4820" OR "4625" OR "4624" OR "4647" OR "4778" OR "4779" OR "4800" OR "4801" OR "4802" OR "4803") "Audit Failure" * * * * *
| json "channel", "provider", "event_id", "computer","task","keywords","event_data","message" as Channel, Provider, EventID, Computer, Task, Keywords, Event_Data, Message nodrop
| json field=EventID "qualifiers","id" as qualifiers, EventID
| json field=Provider "guid","event_source","name" as Guid, EventSource,Provider
| where Channel = "Security"
| where provider = "Microsoft-Windows-Security-Auditing"
| where EventID in ("4770", "4771", "4772", "4776", "4776", "4768", "4769", "4820", "4625", "4624", "4647", "4778", "4779", "4800", "4801", "4802","4803")
| where EventID matches "{{EventID}}"
| where Keywords matches "*Audit Failure*"
| where Computer matches "{{Computer}}"
| json field=Event_Data "TargetDomainName","TargetUserName", "SubjectDomainName", "SubjectUserName", "IpAddress", "LogonType" as TargetDomainName, TargetUserName, SubjectDomainName, SubjectUserName, IpAddress, LogonType nodrop
| where !(TargetUserName matches "*$")
| replace(IpAddress, "::ffff:", "") as IpAddress
| formatDate(_messageTime, "yyyy-MM-dd hh:mm:ss") as date
| format("%s/%s", SubjectDomainName, SubjectUserName) as subject
| format("%s/%s", TargetDomainName, TargetUserName) as target
| parse field=Message "*\n" as message nodrop
| where subject matches "{{{Subject}}}"
| where target matches "{{{Target}}}"
| where IpAddress matches "{{{IpAddress}}}"
| timeslice 1h
| count as Total _timeslice
| order by _timeslice
Viewing Windows - Cloud Security Monitoring and Analytics dashboards
All dashboards have a set of filters that you can apply to the entire dashboard. Use these filters to drill down and examine the data to a granular level.
- You can change the time range for a dashboard or panel by selecting a predefined interval from a drop-down list, choosing a recently used time range, or specifying custom dates and times. Learn more.
- If required, configure the refresh interval rate for a dashboard or panel by clicking the drop-down arrow next to the refresh icon.
- Click the funnel icon in the dashboard top menu bar to filter the dashboard with template variables.

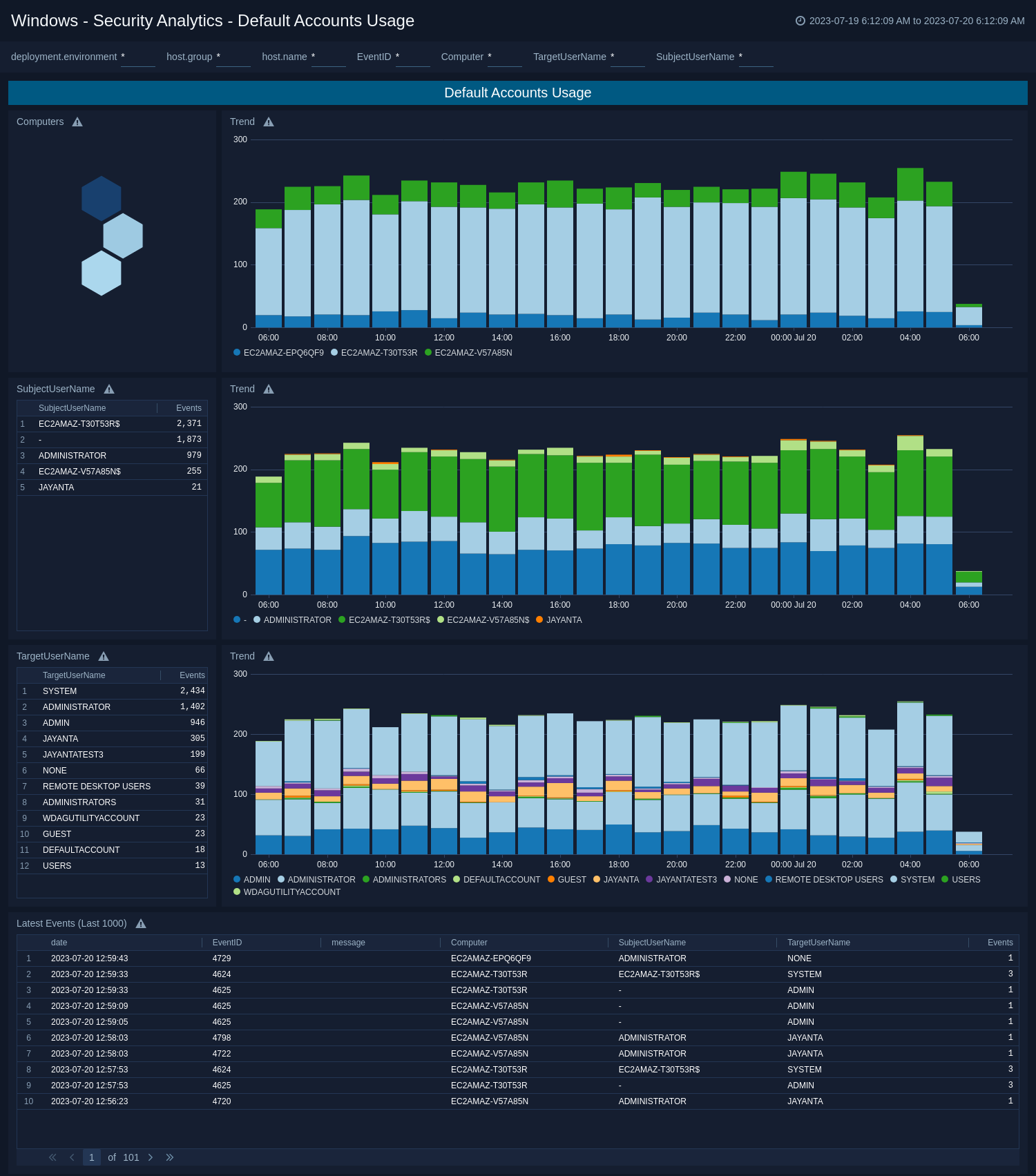
Default Accounts Usage
The Windows - Security Analytics - Default Accounts Usage dashboard displays analytics of default account usage including Administrator, Guest, System, and Root accounts.
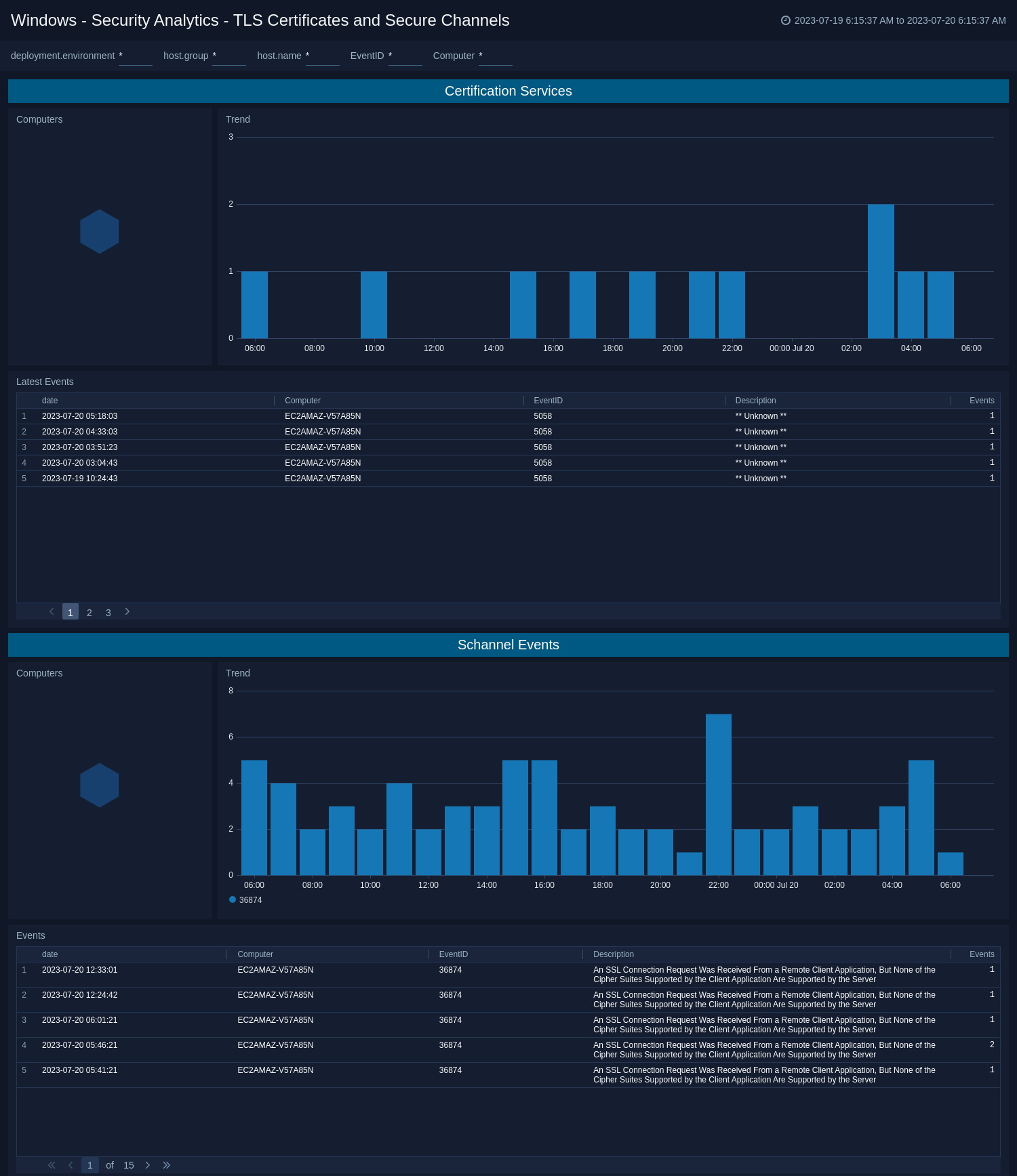
TLS Certificates and Secure Channels
The Windows - Security Analytics - TLS Certificates and Secure Channels dashboard provides security analytics on TLS and Schannel events.
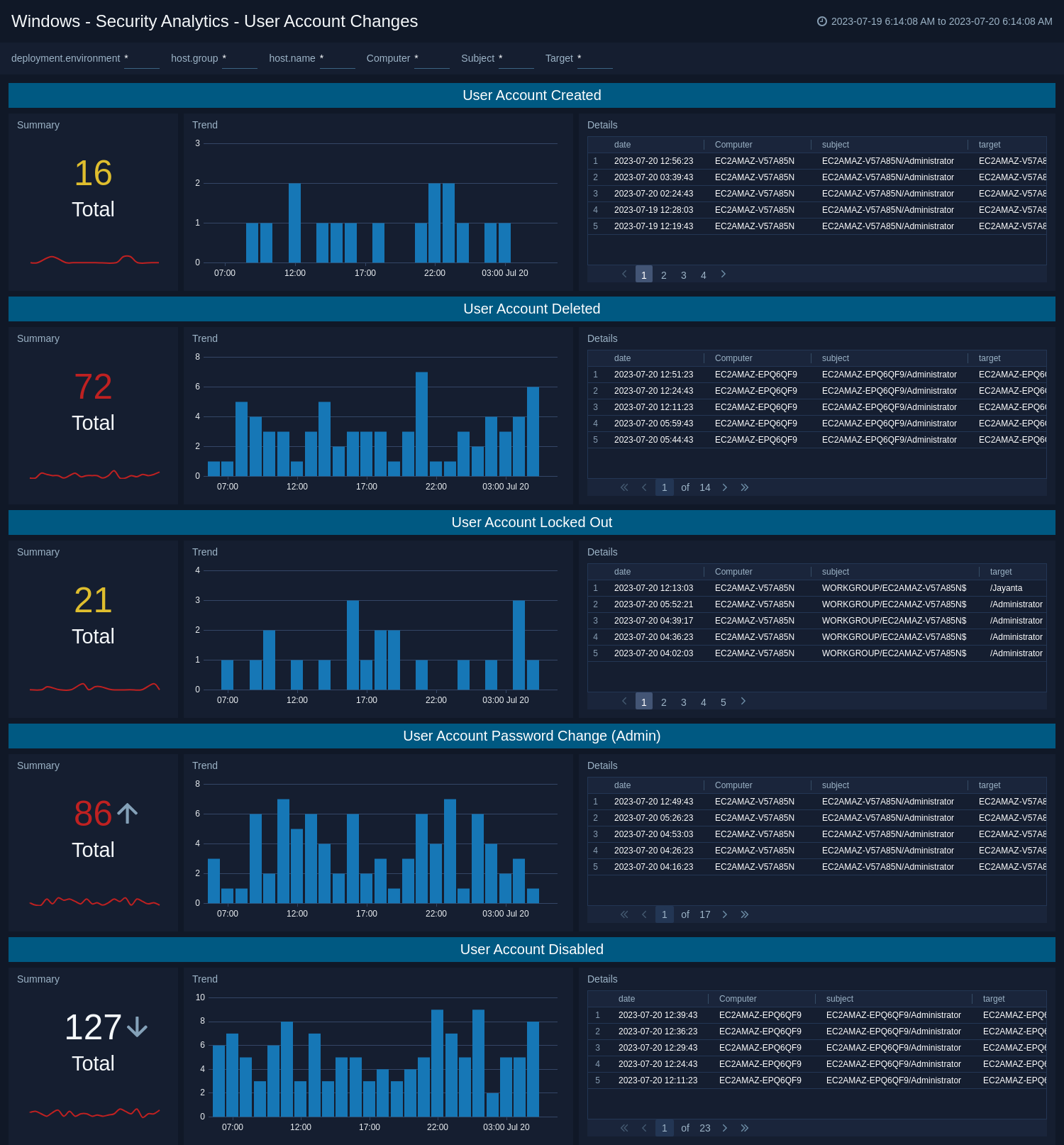
User Account Changes
The Windows - Security Analytics - User Account Changes dashboard provides analytics on user account changes and events.
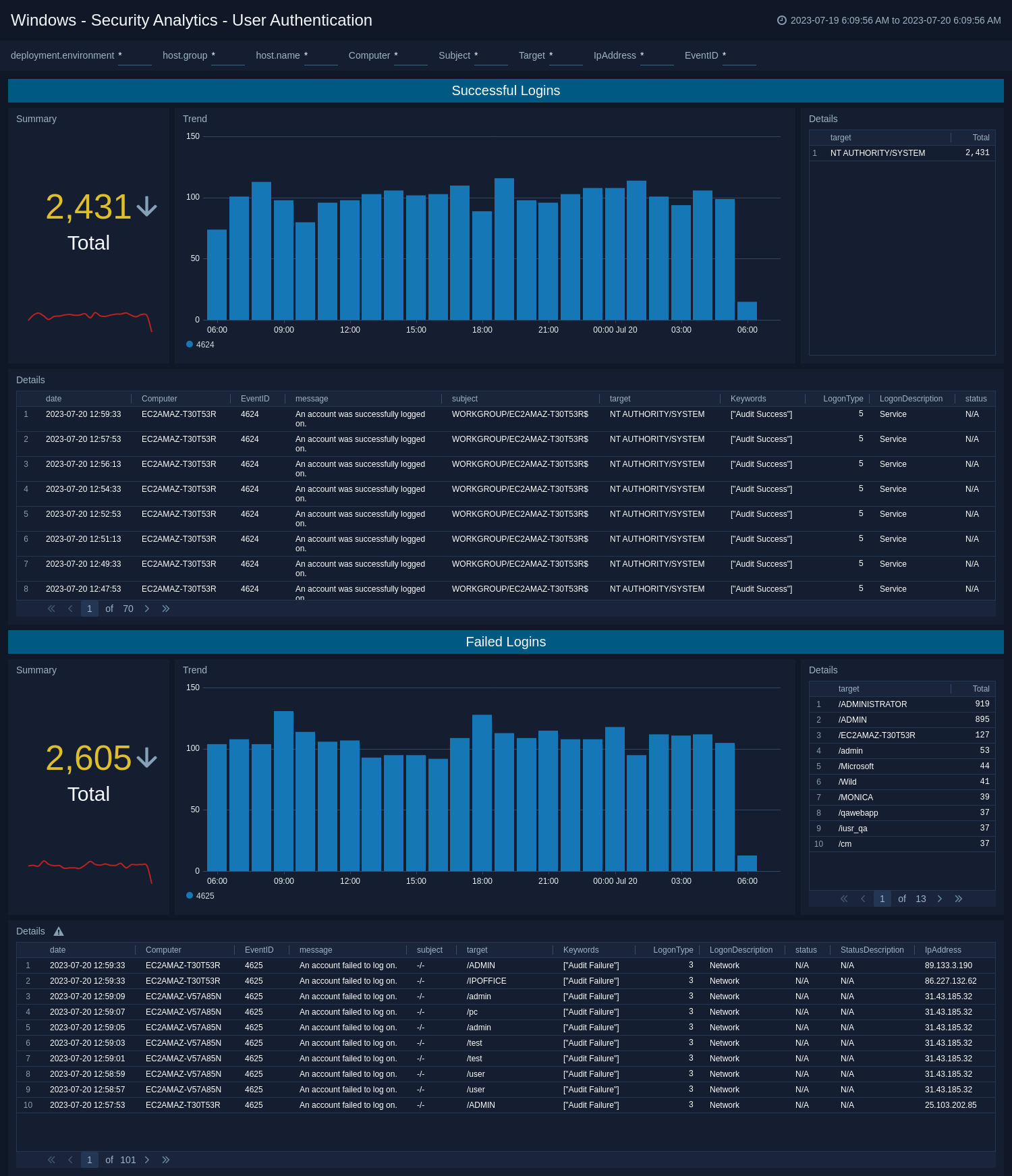
User Authentication
The Windows - Security Analytics - User Authentication dashboard provides security analytics on successful and failed account logins.
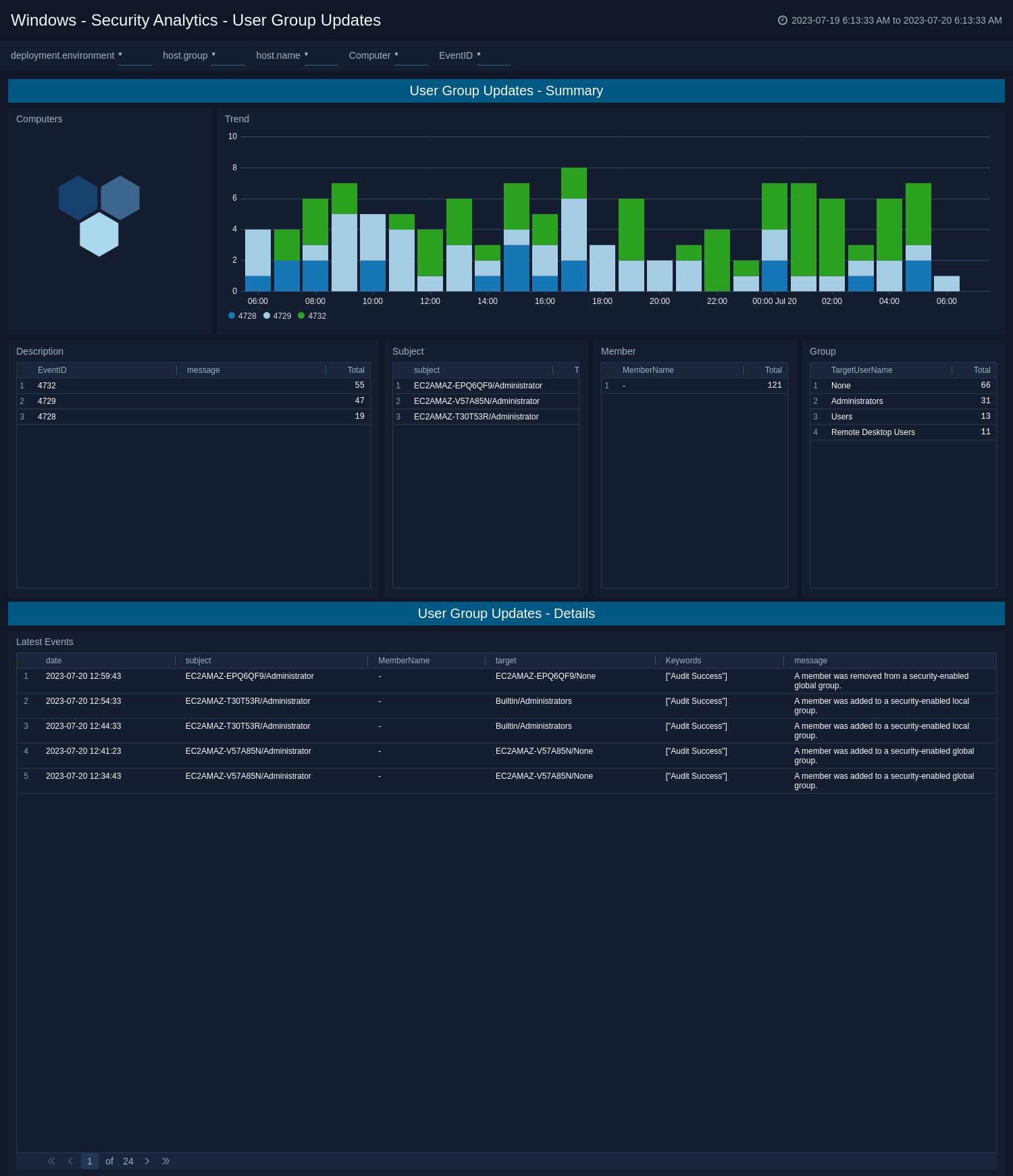
User Group Updates
The Windows - Security Analytics - User Group Updates dashboard provides security analytics on user group updates.
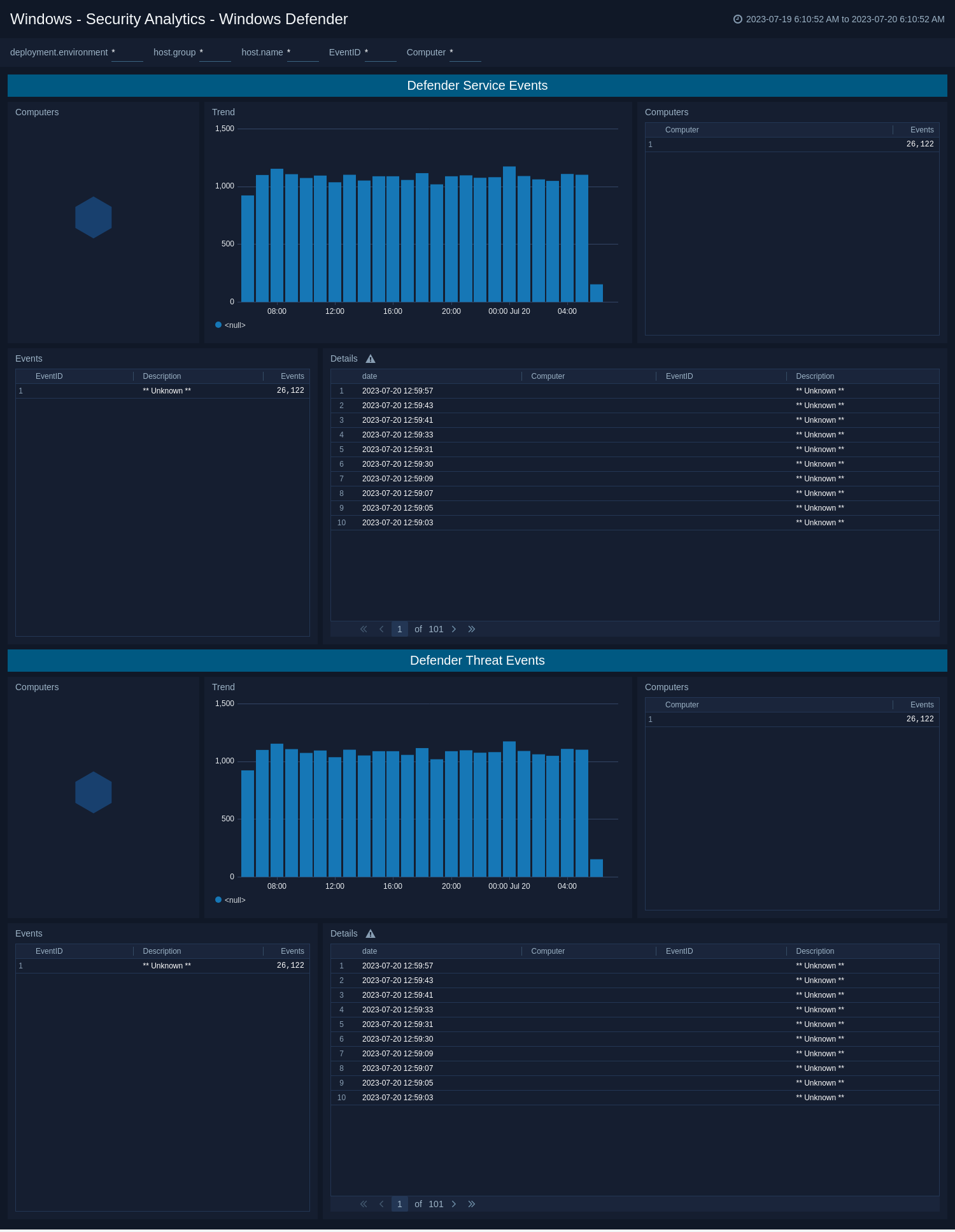
Windows Defender
The Windows - Security Analytics - User Authentication dashboard provides security analytics on Windows Defender events.
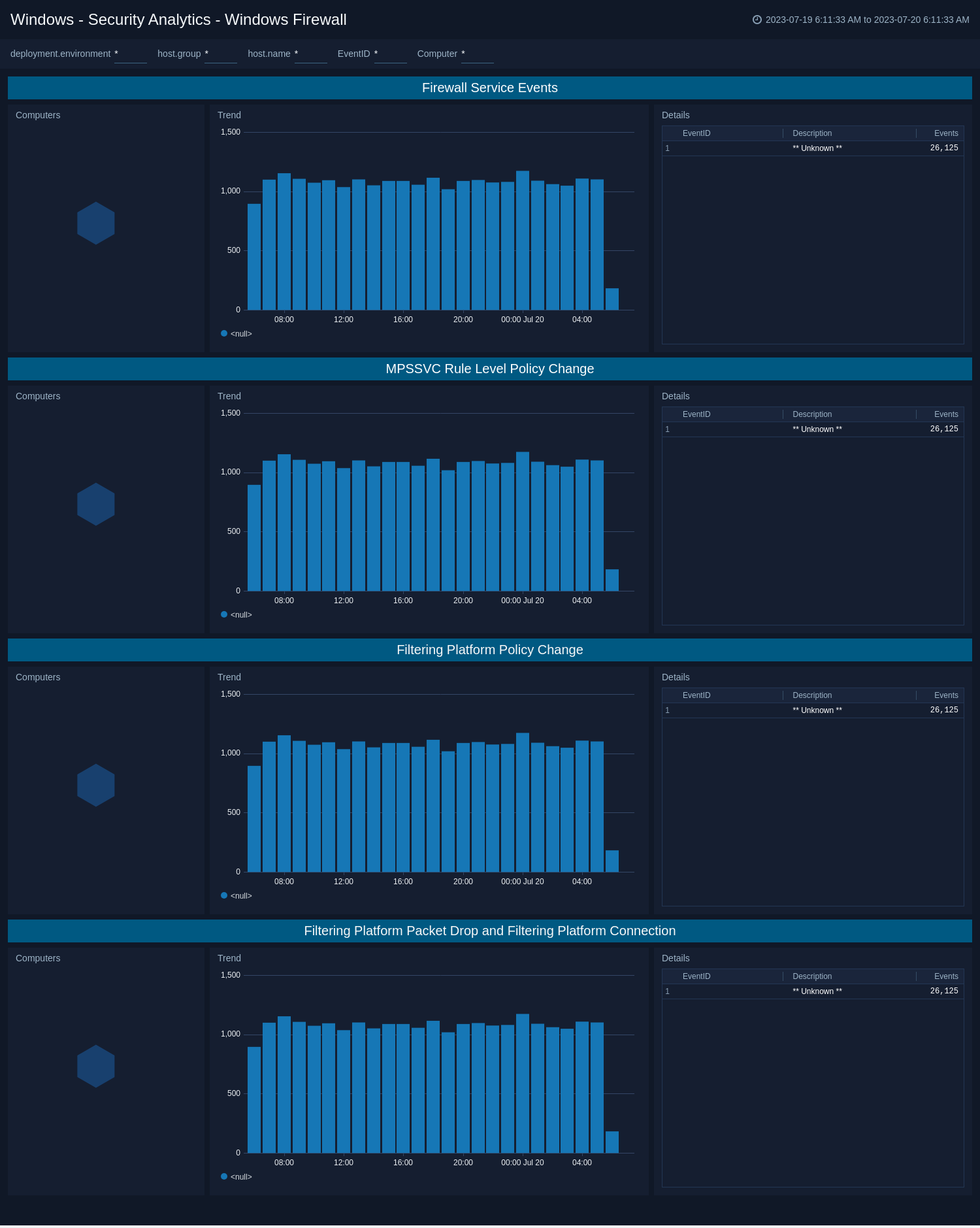
Windows Firewall
The Windows - Security Analytics - Windows Firewall dashboard provides security analytics on Windows Firewall events.
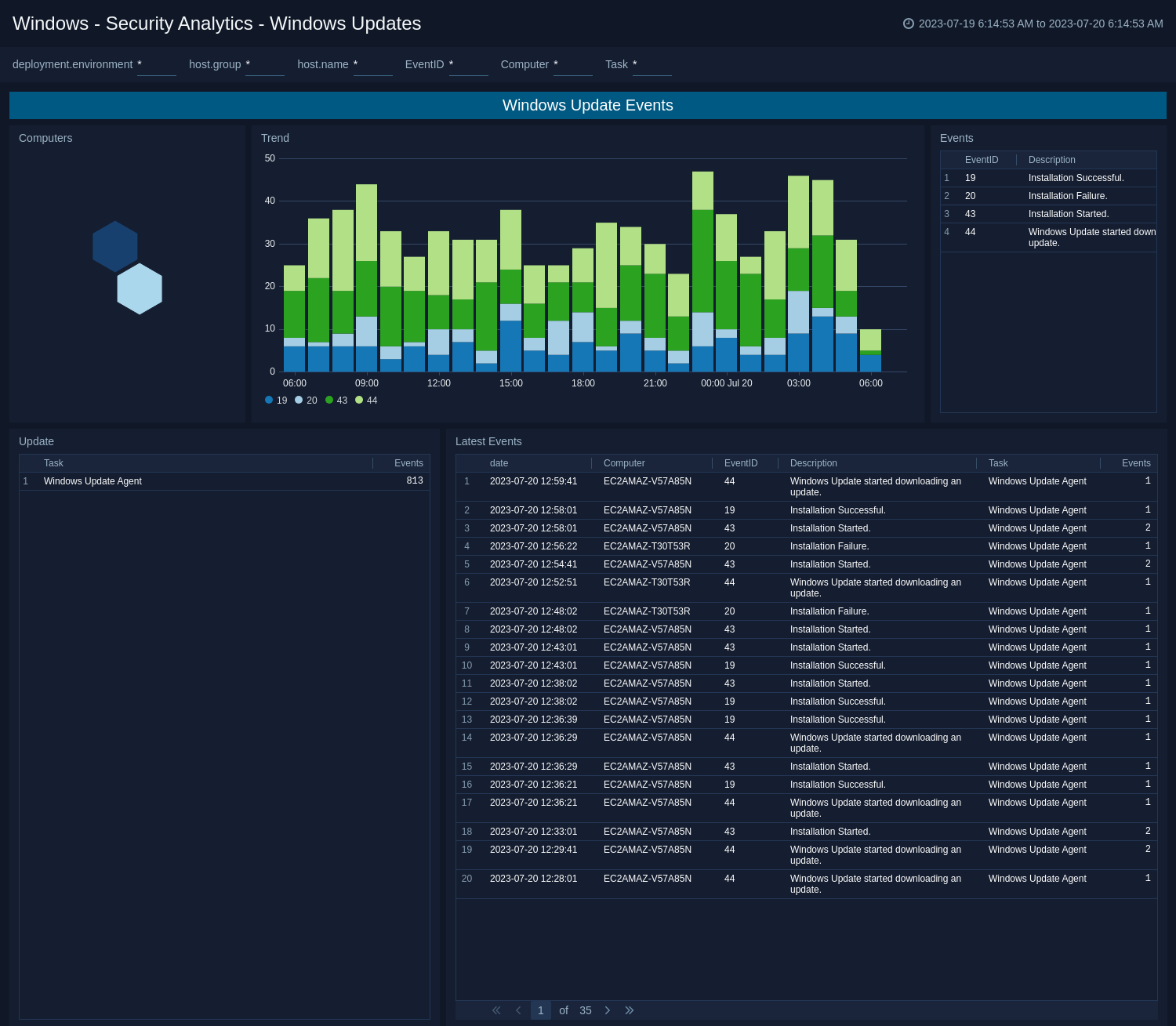
Windows Updates
The Windows - Security Analytics - Windows Updates dashboard provides security Windows Updates events.
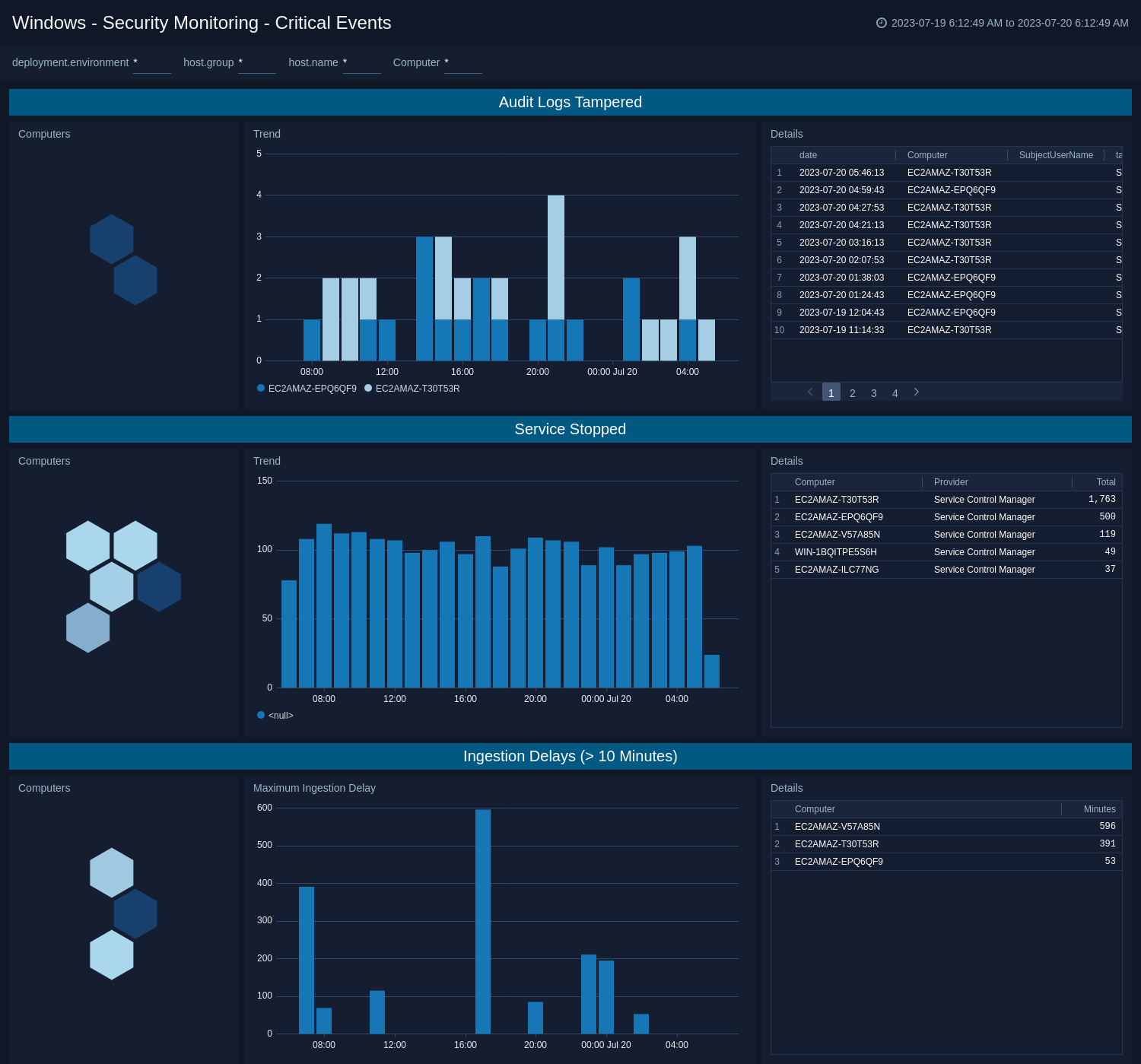
Critical Events
The WWindows - Security Monitoring - Critical Events dashboard provides analysis of critical security events related to services stopped, audit logs tampered, and logging ingestion delays.
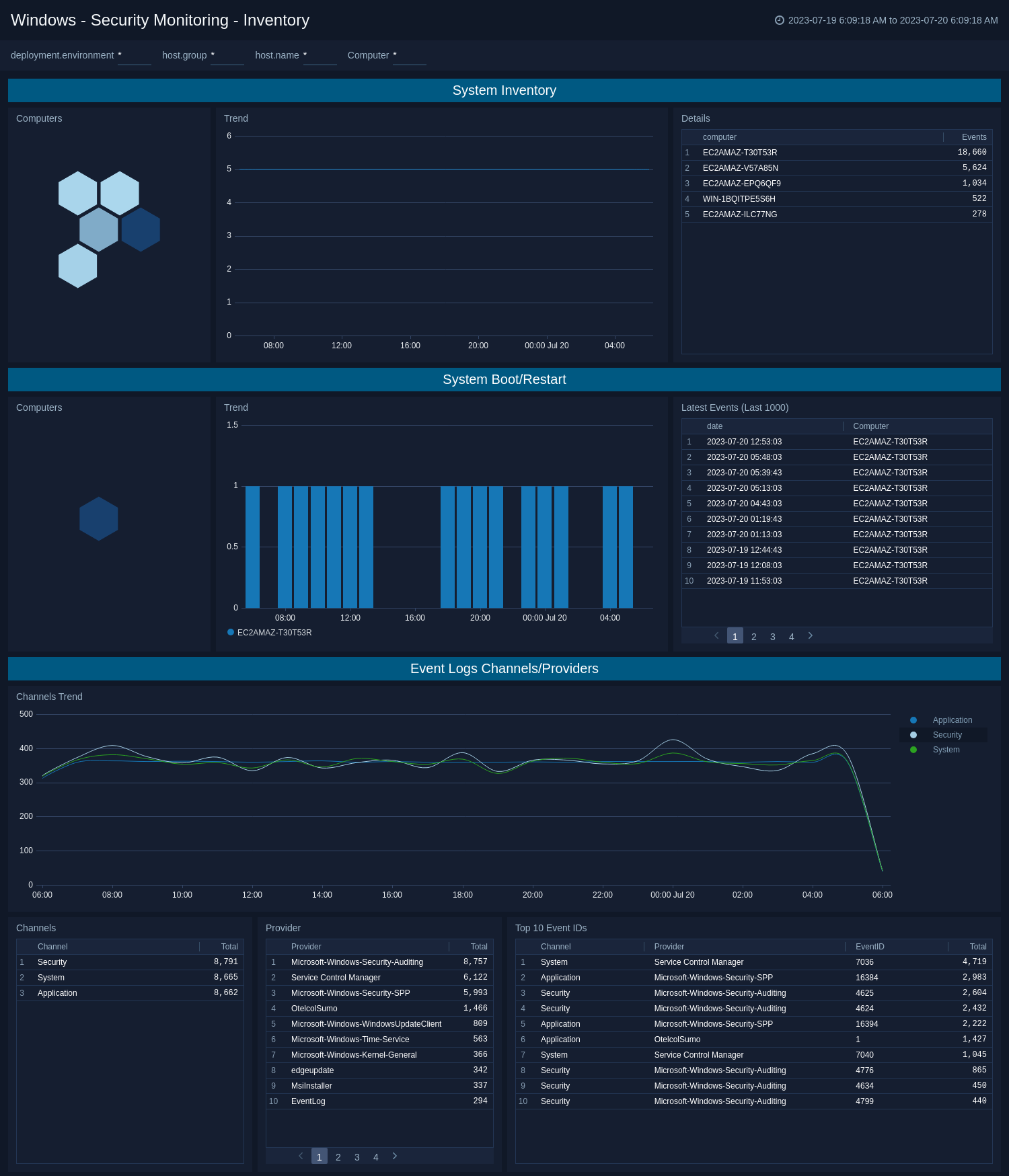
Inventory
The Windows - Security Monitoring - Inventory dashboard helps you to monitor windows events provided by computer, channel, and provider. This dashboard also provides additional information on computer reboots.
Create monitors for Windows - Cloud Security Monitoring and Analytics app
From your App Catalog:
- From the Sumo Logic navigation, select App Catalog.
- In the Search Apps field, search for and then select your app.
- Make sure the app is installed.
- Navigate to What's Included tab and scroll down to the Monitors section.
- Click Create next to the pre-configured monitors. In the create monitors window, adjust the trigger conditions and notifications settings based on your requirements.
- Scroll down to Monitor Details.
- Under Location click on New Folder.
note
By default, monitor will be saved in the root folder. So to make the maintenance easier, create a new folder in the location of your choice.
- Enter Folder Name. Folder Description is optional.
tip
Using app version in the folder name will be helpful to determine the versioning for future updates.
- Click Create. Once the folder is created, click on Save.
Windows - Cloud Security Monitoring and Analytics alerts
| Name | Description | Alert Condition | Recover Condition |
|---|---|---|---|
Windows CSMA - Audit Log Tampering Detection | This alert is triggered when attempt is detected to clear or tamper with Windows audit logs, indicating potential attempts to cover malicious activities. | Count > = 1 | Count < 1 |
Windows CSMA - Failed Authentication Spike | This alert is triggered when unusual spikes in failed authentication attempts are detected, indicating potential brute force attacks. | Count > = 10 | Count < 10 |
Windows CSMA - Windows Update Failures | This alert is triggered when repeated Windows Update failures are detected, indicating potential vulnerabilities to known exploits. | Count > = 3 | Count < 3 |