What is threat hunting?
Threat hunting, cyber threat hunting or proactive threat hunting, is the seeking out unknown cybersecurity threats to a network. Threat hunting involves actively searching through endpoints, networks, systems, applications, sources and datasets to hunt or identify malicious activity or suspicious activity.
Key takeaways
- Cyber threat hunters usually leverage log data, permission, and comparative approaches to help them identify abnormalities.
- While threat detection or automated triggers help find potentially harmful material in your networks, these are still somewhat passive approaches that should work alongside a cyber threat-hunting strategy.
- Alert reduction, event correlation, anomaly detection, and deep analytic features are all optimized through Sumo Logic’s advanced, intelligent features.
How does threat hunting work?
A cyber threat hunter digs deep into the backends of websites to find anomalies and issues that may lead to an attack on the network. It’s a manual process that involves IT security analysts thoroughly scrutinizing the security data in their networks. Rather than rely on a single threat hunting tool, threat hunters utilize several tools, including automation, machine learning and behavioral analytics solutions, to identify a potential threat.
Cyber threat hunters usually leverage log data, permission and comparative approaches to help them identify abnormalities. Baselining, for example, helps threat hunters understand how their networks would look under normal conditions. From there, they can begin to identify abnormalities in the network and single out malicious behavior.
What is managed threat hunting?
Managed threat hunting allows organizations to benefit from the expertise and resources of specialized security professionals without the need to maintain an in-house security operations center (SOC). In this model, specialized security analysts continuously monitor the organization’s network and systems for security threats, emerging threats, attackers, malicious activity, an insider threat, hidden threat or an advanced threat using practical threat hunting, managed detection, threat modeling, the MITRE ATTCK framework, cyber threat intelligence, penetration testing, automated tools, advanced analytics and human expertise.
Threat hunting steps
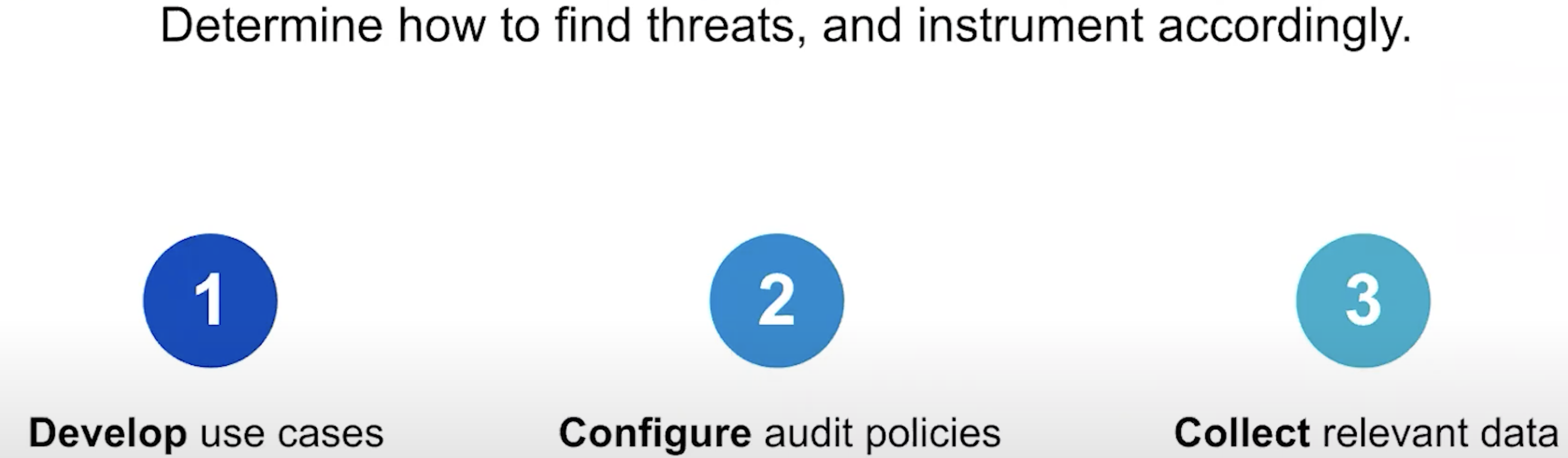
While threat detection or automated triggers help find potentially harmful material in your networks, these passive approaches should work alongside a cyber threat hunting techniques and strategy. Threat hunting follows a series of steps that ensure a thorough and effective hunt. These steps include:
- Starting with a hypothesis: All threat hunters begin by hypothesizing where or what threats might compromise the system. AI applications, baselining, and other security-related solutions lead threat hunters to their starting points.
- Data collection: With the help of SIEM solutions, threat hunters can utilize data already at the organization’s disposal to verify their assumptions.
- Investigation: Once threat hunters have developed a hypothesis and examined their data, they can begin investigating based on Indicators of Compromise (IoC) or Indicators of Attack, signs or evidence of an attack. These include malware infection, suspicious outbound traffic and large outbound data transfers.
- Resolution: With the help of automation, advanced analytics, and machine learning, threat hunters can submit data into their intelligent solutions that will subsequently identify, resolve, and mitigate or remediate threats.
When to engage in threat hunting?
Ideally, threat hunting is happening all the time. The idea behind threat hunting is proactive security that promotes cyber resilience against threat actors..
In practice, this may mean monthly, bi-weekly, and weekly checks and scans through log data and other relevant network features. Only by examining large pools of crowdsourced data and log data regularly can threat hunters gain insight into attack tactics and respond accordingly with the steps listed above.
Types of threat hunting tools
In an ever-evolving threat landscape, information security teams use several tools for threat hunting. Some of these tools provide IT teams with the space to reallocate time to threat hunting, while others provide tool automation that assists threat hunters in getting through their steps more efficiently and quickly.
- Xori Automated Disassembly: Xori automates the tedious process of disassembling malware, including the swaths of sample variants from the same family of malware.
- Dejavu Deception Framework: Dejavu is a clever solution to a tricky problem. Dejavu creates a number of fake workstations and servers that lure in rogue bots or unwanted bugs and identify where they came from to prevent future breaches.
- Dradis Framework: Dradis is like Github for reporting threats. It’s a collaborative solution that basically makes it easier to customize, format, and create reports on threats.
Threat hunting with Sumo Logic
Sumo Logic’s Cloud SIEM helps optimize your threat-hunting strategy and incident response. Improved cyber security analyst productivity and automated security operations center (SOC) analyst workflows help IT teams perform all the routine tasks that go into threat hunting. Additionally, focused and guided workflows remove resources from managing SIEM systems and put that energy on proactive measures, like cyber threat hunting.
Alert reduction, event correlation, anomaly detection and deep analytic features are all optimized through Sumo Logic’s advanced, intelligent features that make threat hunting more effective, efficient and seamless for IT teams.
Learn more about modern SIEM technology in our ultimate guide.