Claude Anthropic Compliance API App (Platform)
May 19, 2026
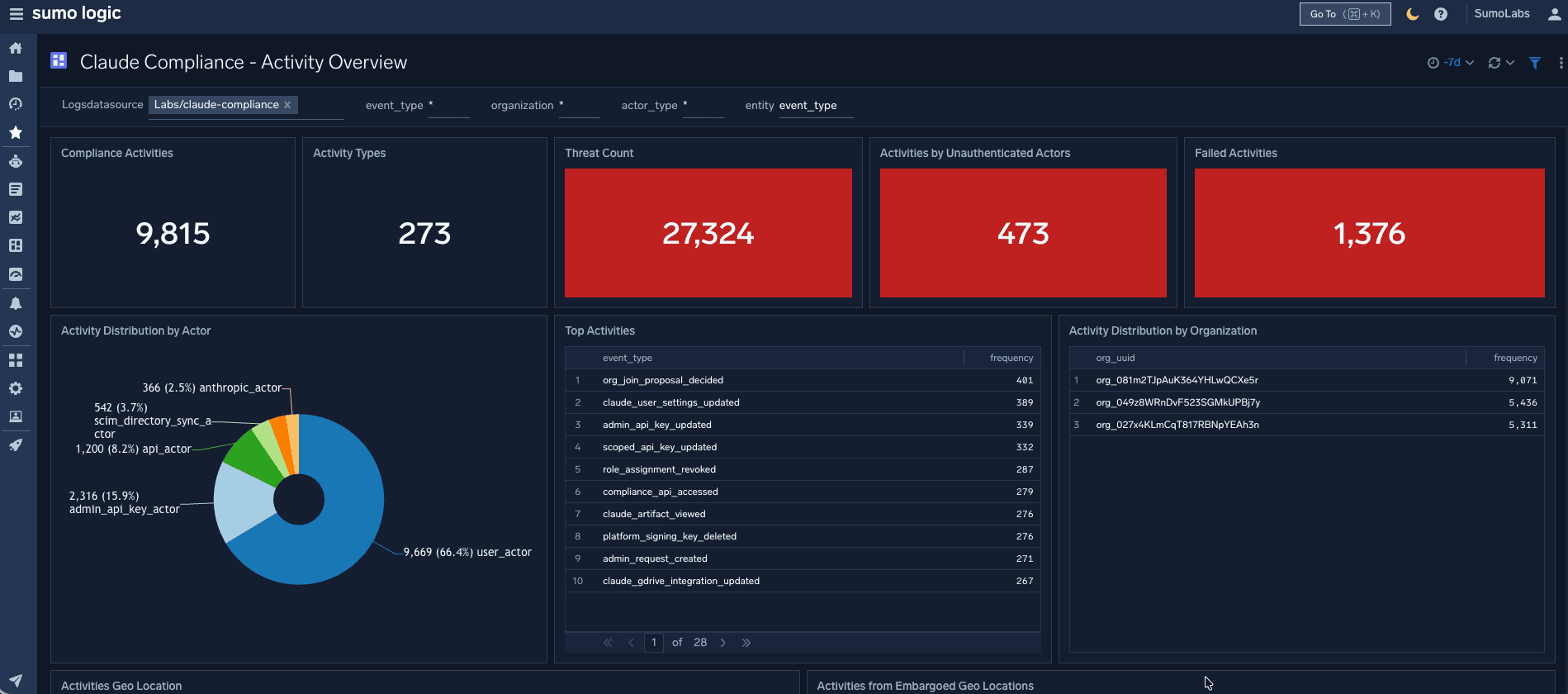
Extend your security and compliance posture to your AI workflows with our new Claude Compliance API integration. This turnkey solution pulls Claude Enterprise activity logs and Claude Platform activity logs directly into Sumo Logic. This integration delivers 11 use cases covering: eDiscovery, data loss prevention (DLP), audit and compliance, API key governance, and developer resource auditing. Monitor AI activity alongside your existing SaaS stack with no custom pipeline development.
Data Deletion Control (Platform)
March 16, 2026
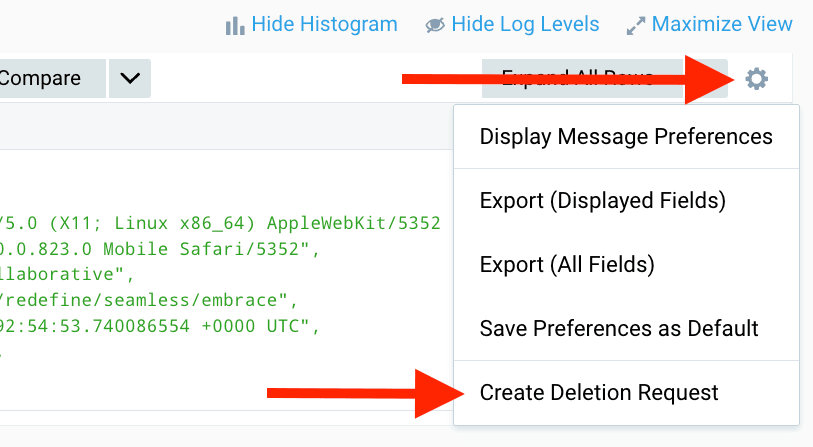
Delete ingested data on demand—no Support ticket required. Authorized users can submit and approve deletion requests directly in the platform or automate them via API, giving teams faster control over data management and compliance workflows.
Insight Bulk Management (Cloud SIEM)
February 18, 2026
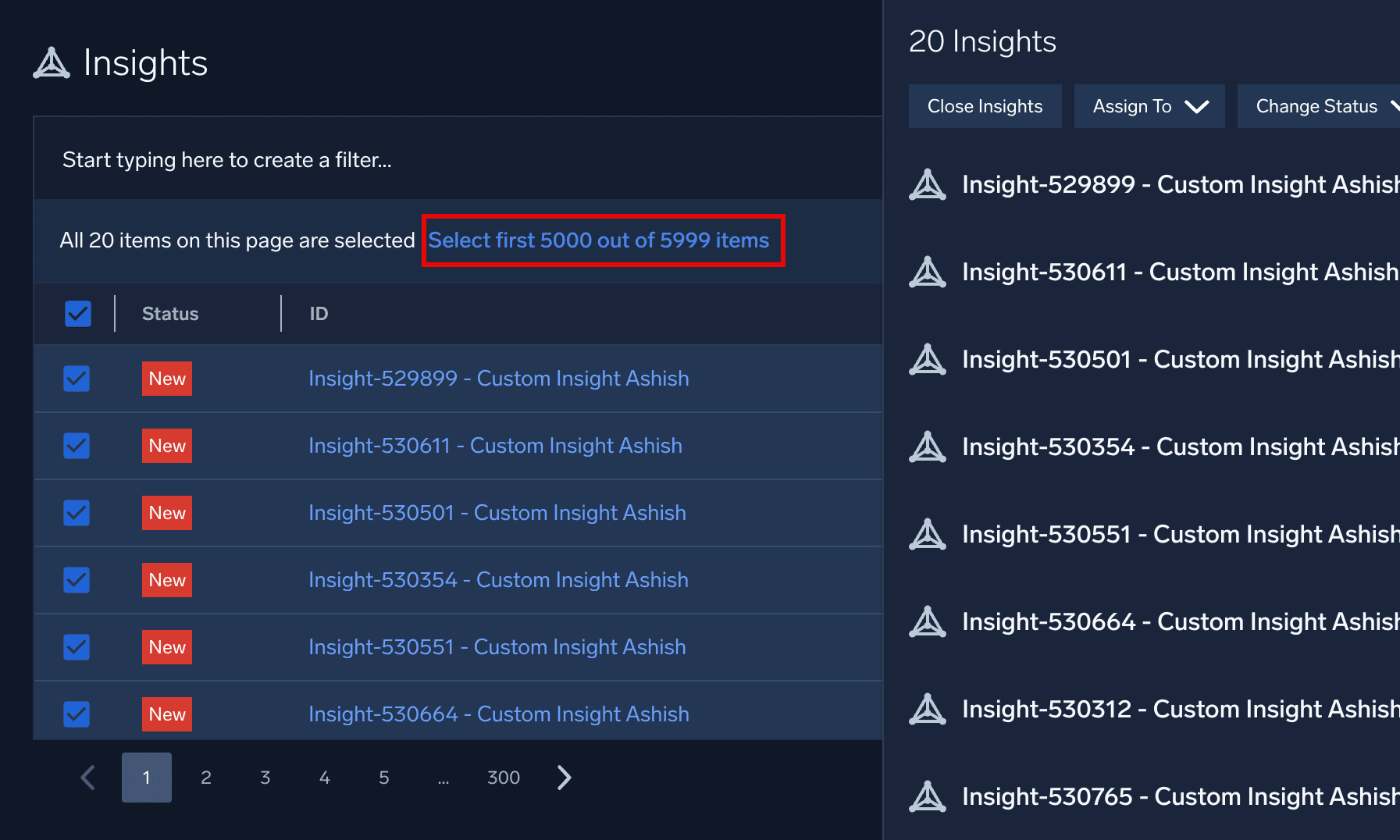
Act on thousands of insights at once to accelerate investigations and response. Update up to 5,000 insights via UI or API, with real-time progress tracking and parallel operations.
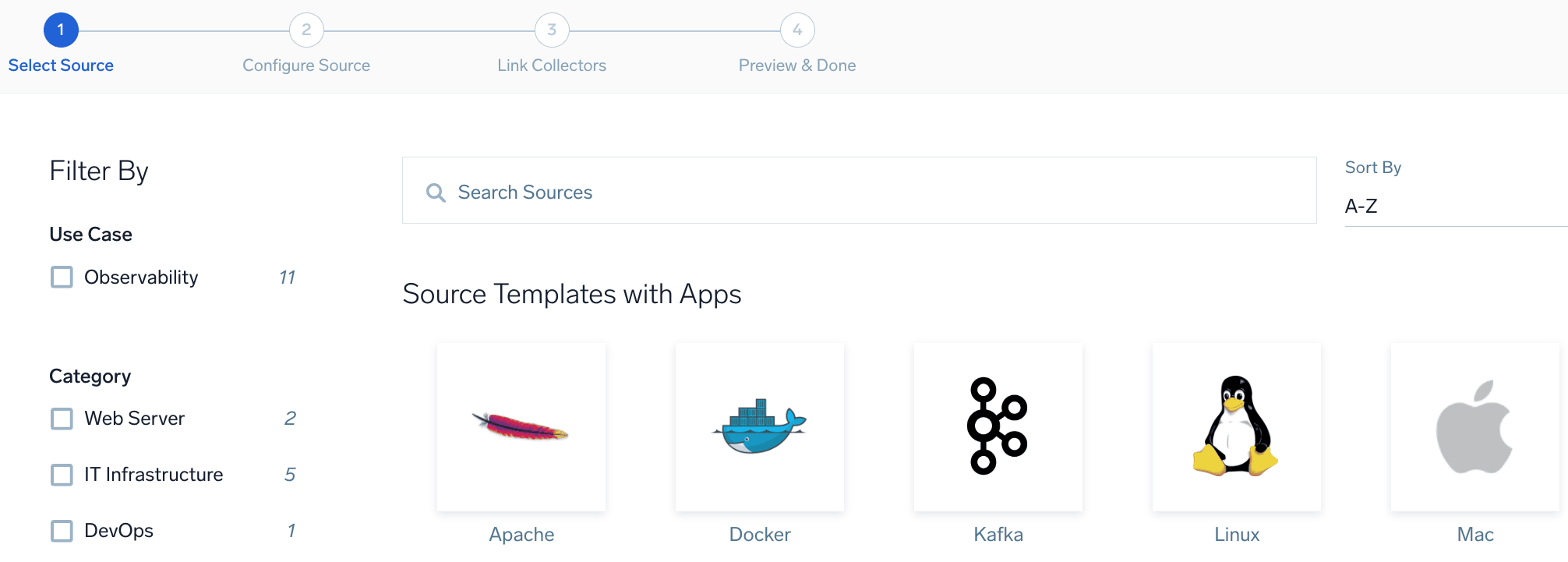
OTEL Source Template-Based Remotely Managed Collectors for Apps (Platform)
February 9, 2026
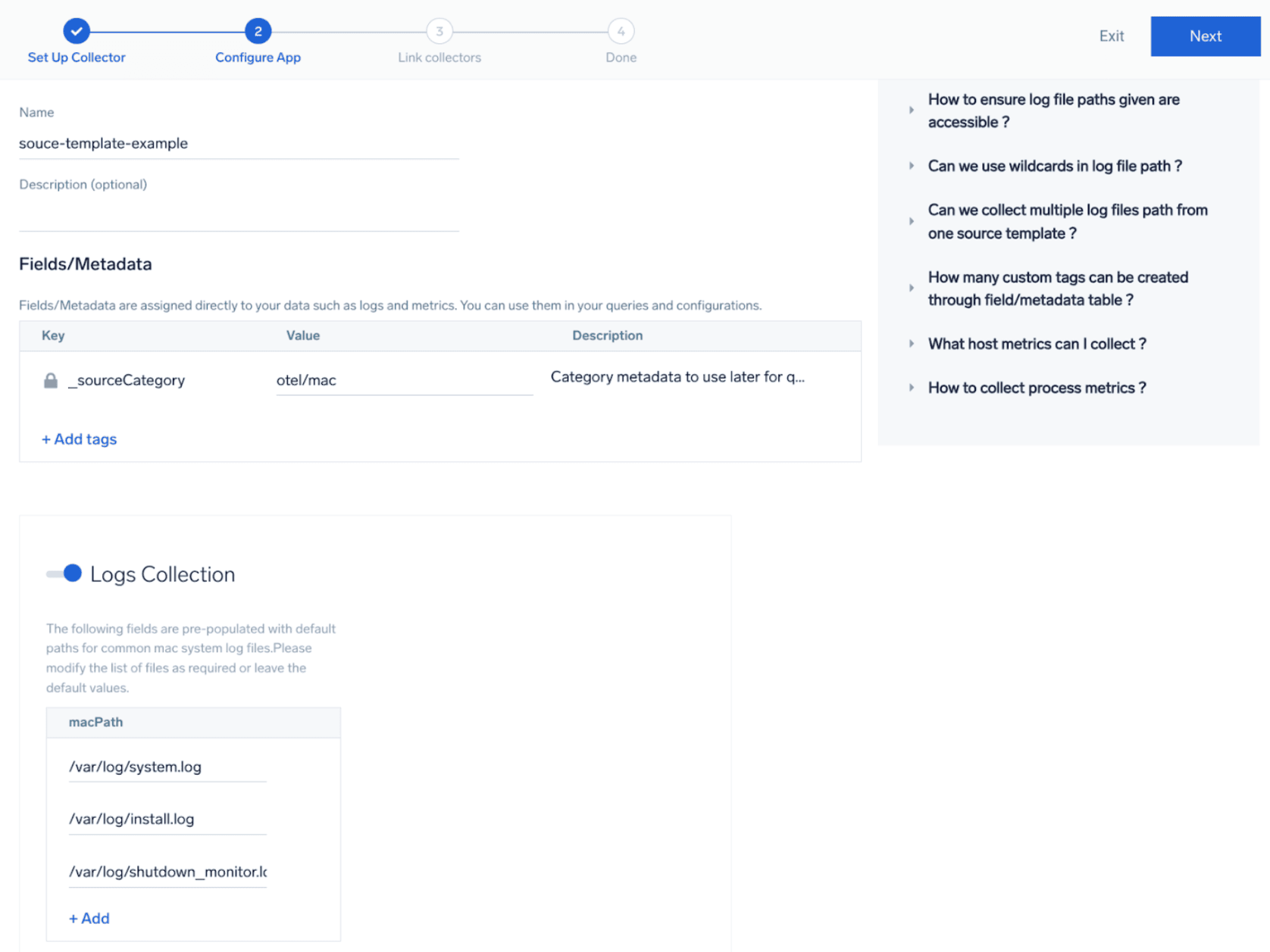
You can now install selected apps from the App Catalog using remotely managed collectors via Source Templates. A new Remotely Managed Apps section guides you through setup, eliminating manual configuration with locally managed collectors and enabling more scalable, streamlined data collection.
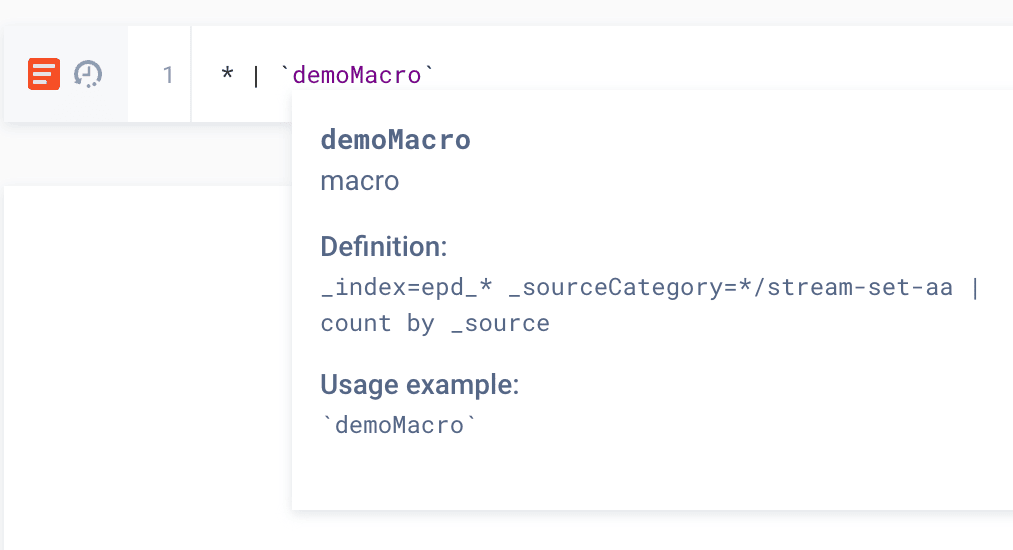
Search: Macro Operator (Platform)
February 26, 2026
We’ve introduced a Macro Operator, which allows you to define reusable query logic once and reference it across multiple searches. This helps standardize logic across dashboards and alerts, reduce duplication, and simplify maintenance.
Installed Collector to OpenTelemetry Collector conversion (Platform)
February 24, 2026
We’re making it easier to move from Installed Collectors to OpenTelemetry. You can now convert existing Installed Collector sources into OpenTelemetry source templates with a guided workflow—reducing manual setup, minimizing errors, and accelerating your path to OTEL.
Custom default roles & user-based role assignment from parent org (Platform)
February 23, 2026
Parent org administrators can now centrally manage default and user-specific role assignments across child organizations. Admins can define a custom default role for users accessing a child org and assign specific roles to individual users per child org. This update streamlines provisioning while ensuring secure, consistent access control across multi-org environments.
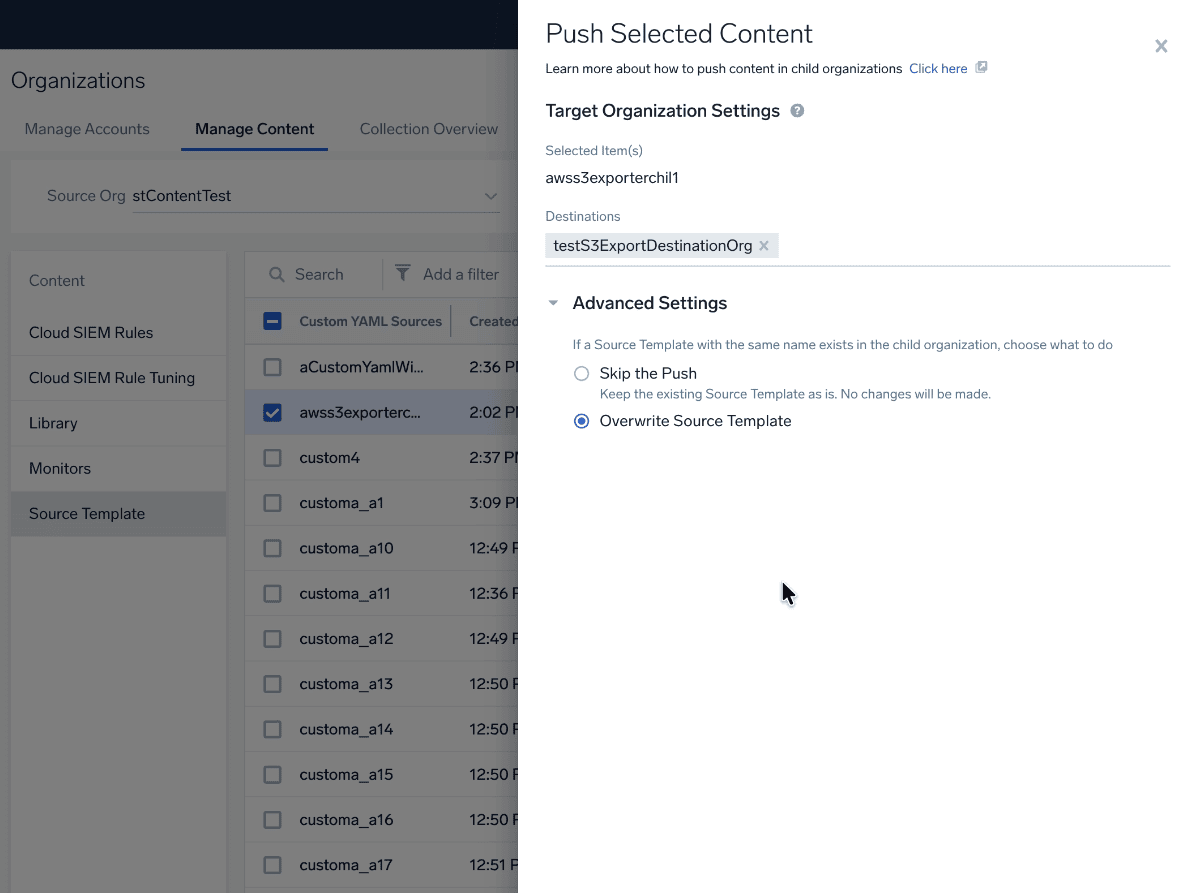
C3M for Source Templates (Platform)
February 13, 2026
We’ve extended Centralized Content & Configuration Management (C3M) to Source Templates. Parent org admins can now create custom YAML source templates and push and manage them across child orgs directly from the parent organization without logging into each child org. This update reduces repetitive manual work, minimizes configuration drift, and provides a scalable, automation-friendly way to manage data collection across complex multi-org environments.
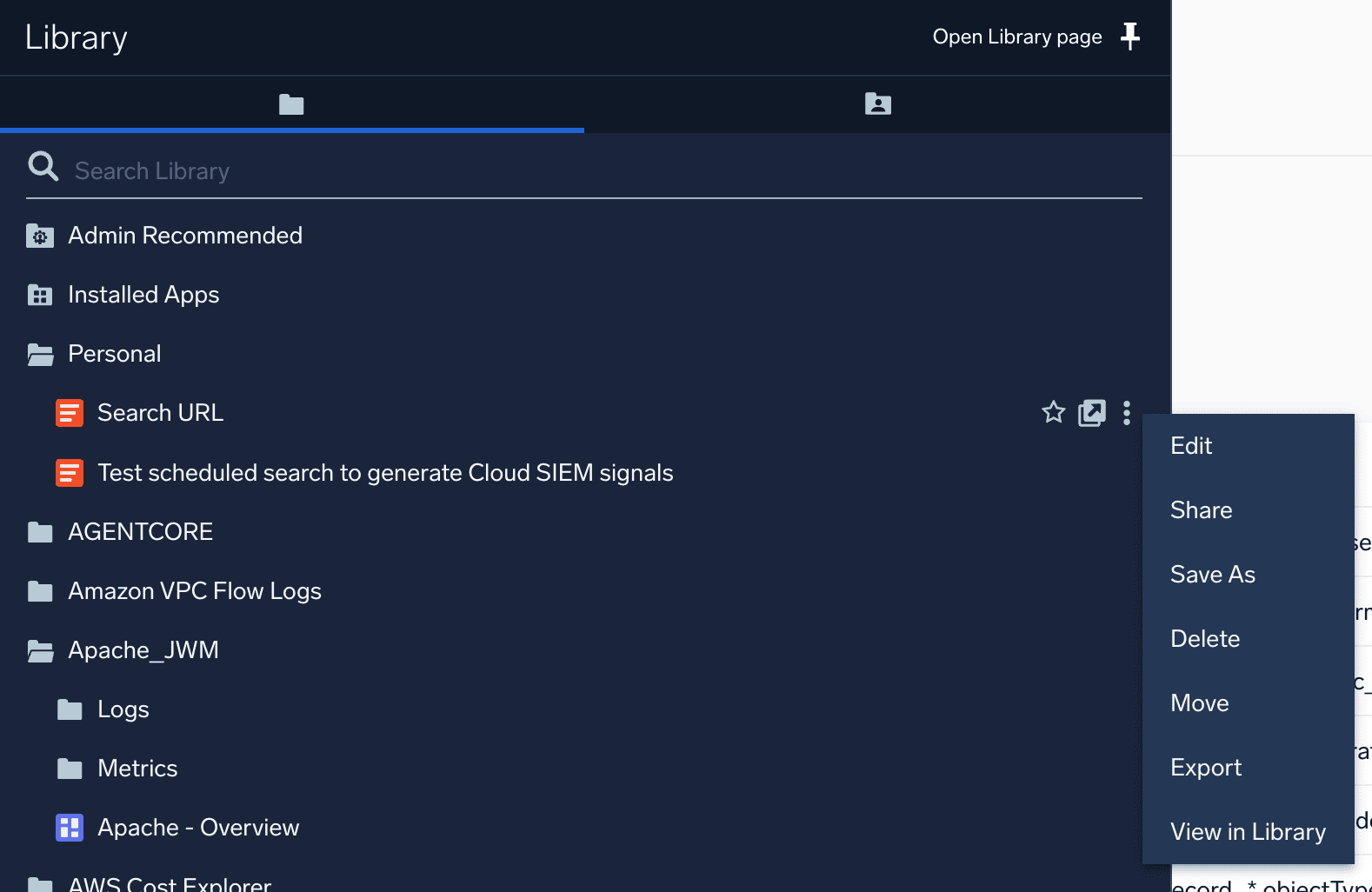
Content item actions in navigation for new UI (Platform)
February 12, 2026
You can now perform quick actions—edit, delete, share, and move—on content directly from navigation menus in the new UI, without first opening the Content Library. This reduces clicks and streamlines everyday content management, helping you work more efficiently across the platform.
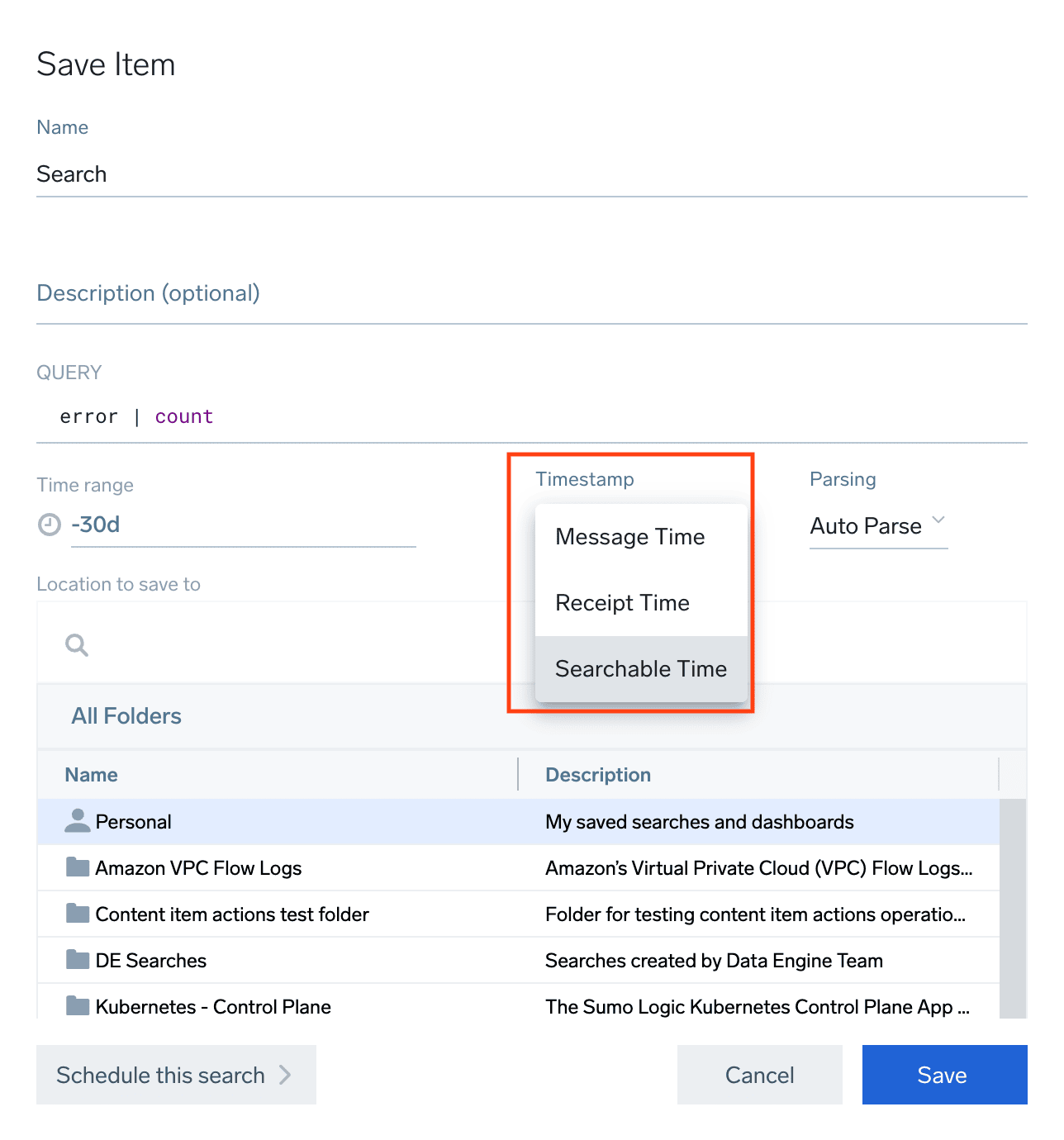
Searchable Time (Platform)
February 6, 2026
You can now query logs using the moment when data is fully processed and guaranteed to be available for search. This helps prevent gaps or duplicate results caused by ingestion latency, making scheduled searches, dashboards, and recurring queries more reliable.
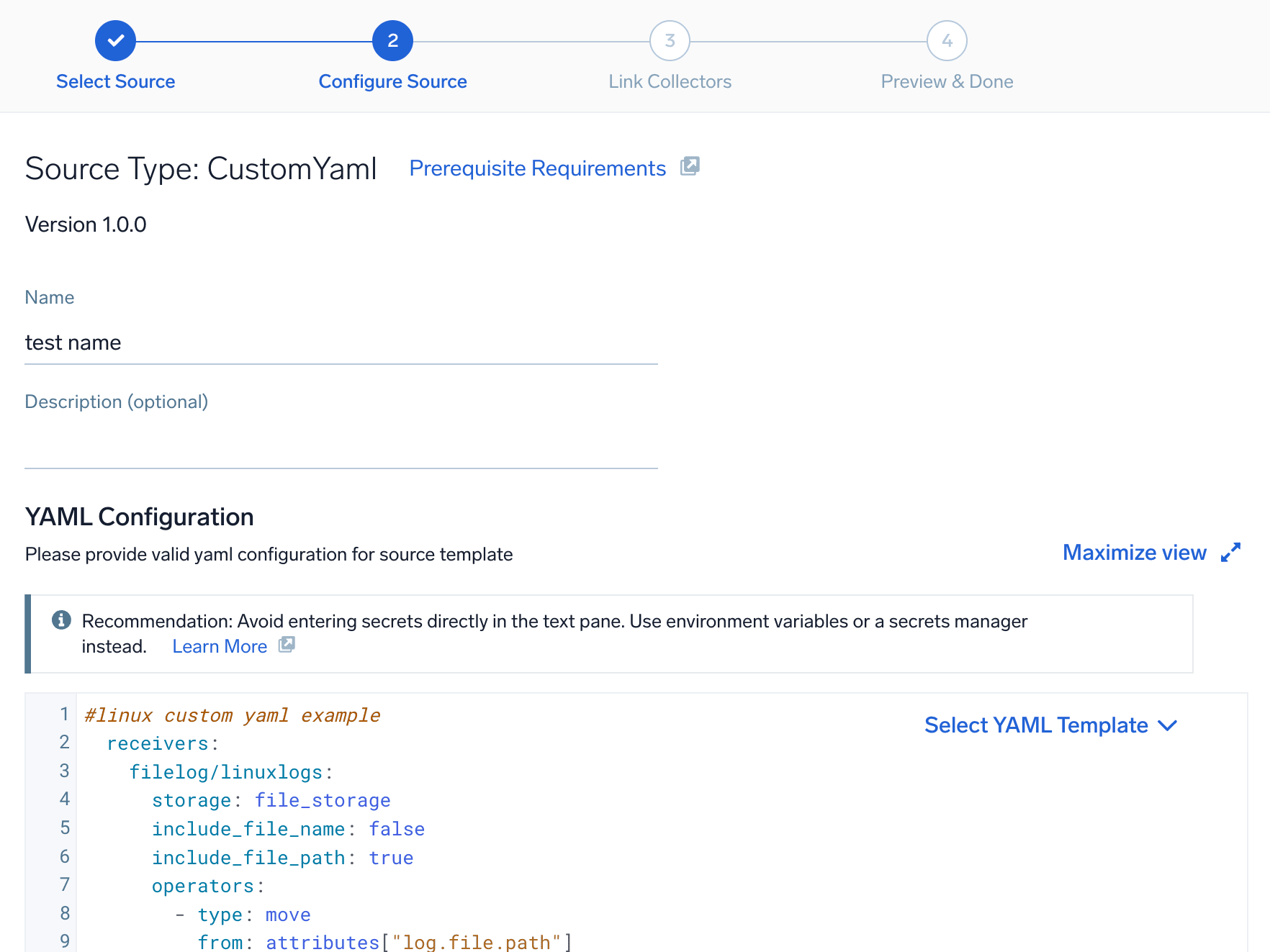
Data Collection: YAML Editor for Source Templates (Platform)
January 30, 2026
A new YAML editor is now available for creating and managing source templates, giving you greater flexibility and control over source configuration.
Playbook Executions (Automation Services / Cloud SOAR)
January 30, 2026
You can now view active and historical playbook runs in one centralized place. Playbook Execution History provides step-level execution details and the ability to cancel running workflows, making it easier to monitor automation health and troubleshoot issues.

Automation Service: Public APIs (Platform / Cloud SOAR)
January 12, 2026
New public APIs allow you to attach, list, and execute playbooks directly from external systems, enabling seamless automation and tighter integration with your existing workflows.
Google SSO (Platform)
January 12, 2026
You can now sign up and sign in to Sumo Logic using Google Single Sign-On (SSO), eliminating the need to create separate credentials.

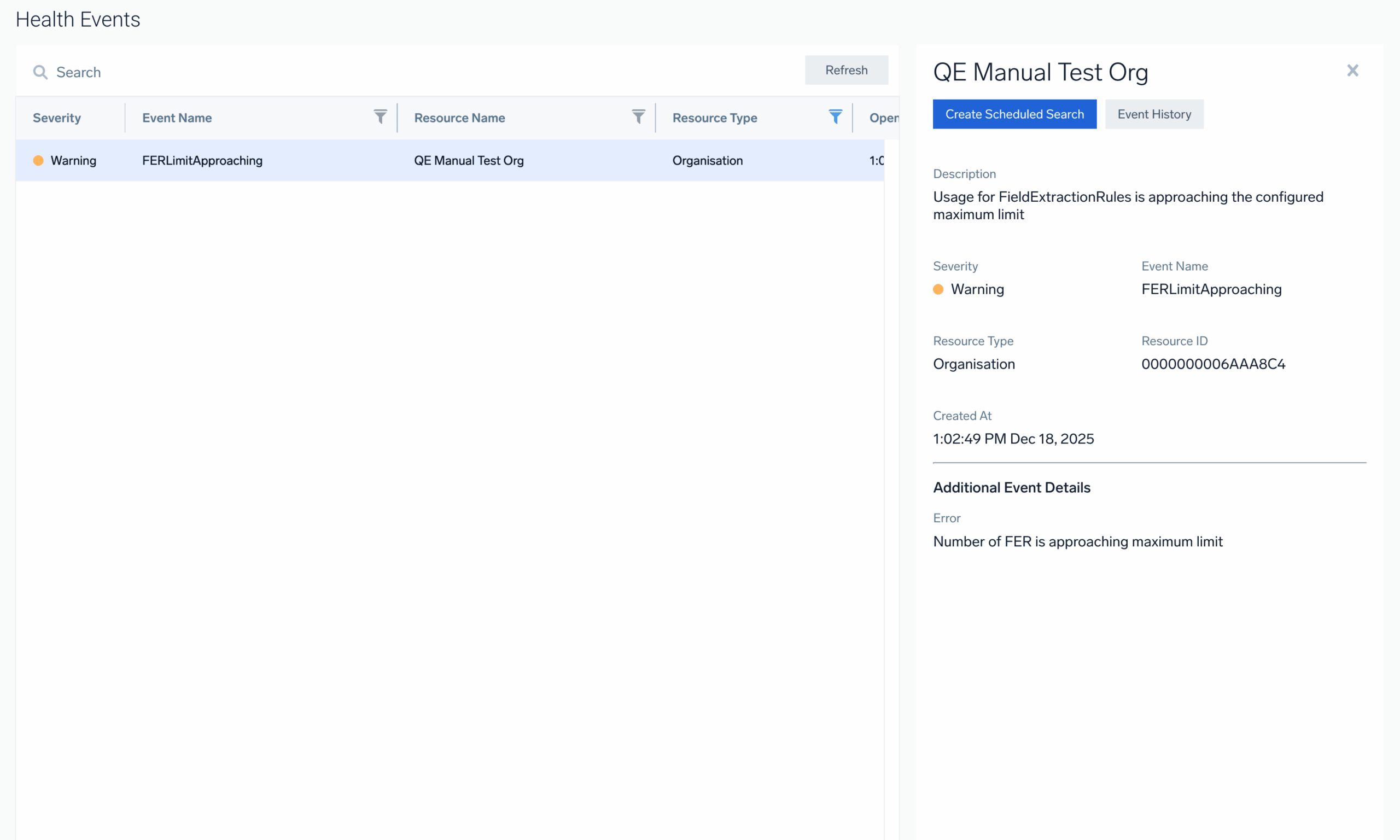
System Limits Visibility (Platform)
December 17, 2025
We’re introducing enhanced visibility and alerting for key system limits: Lookup Tables, Partitions, Fields, and Field Extraction Rules (FERs). Admins now receive health events when usage reaches 90% of these limits. Health events can trigger email alerts, with configurable email alerts and optional scheduled search templates for earlier monitoring.
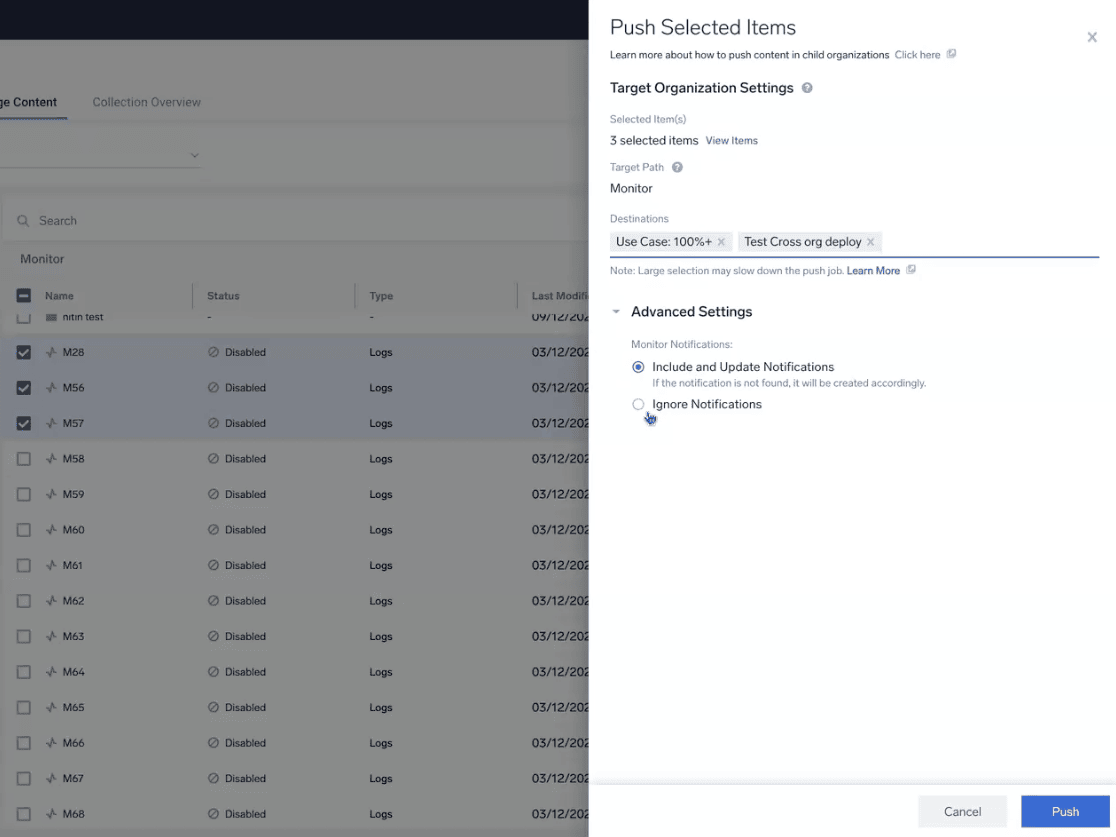
Centralized Monitor management (Platform)
December 15, 2025
Parent org admins can now replicate log, metric, and trace monitors from a parent organization into any managed child org without switching accounts. Core monitor configurations, including trigger logic, notification settings, and connection details, are automatically preserved during replication.
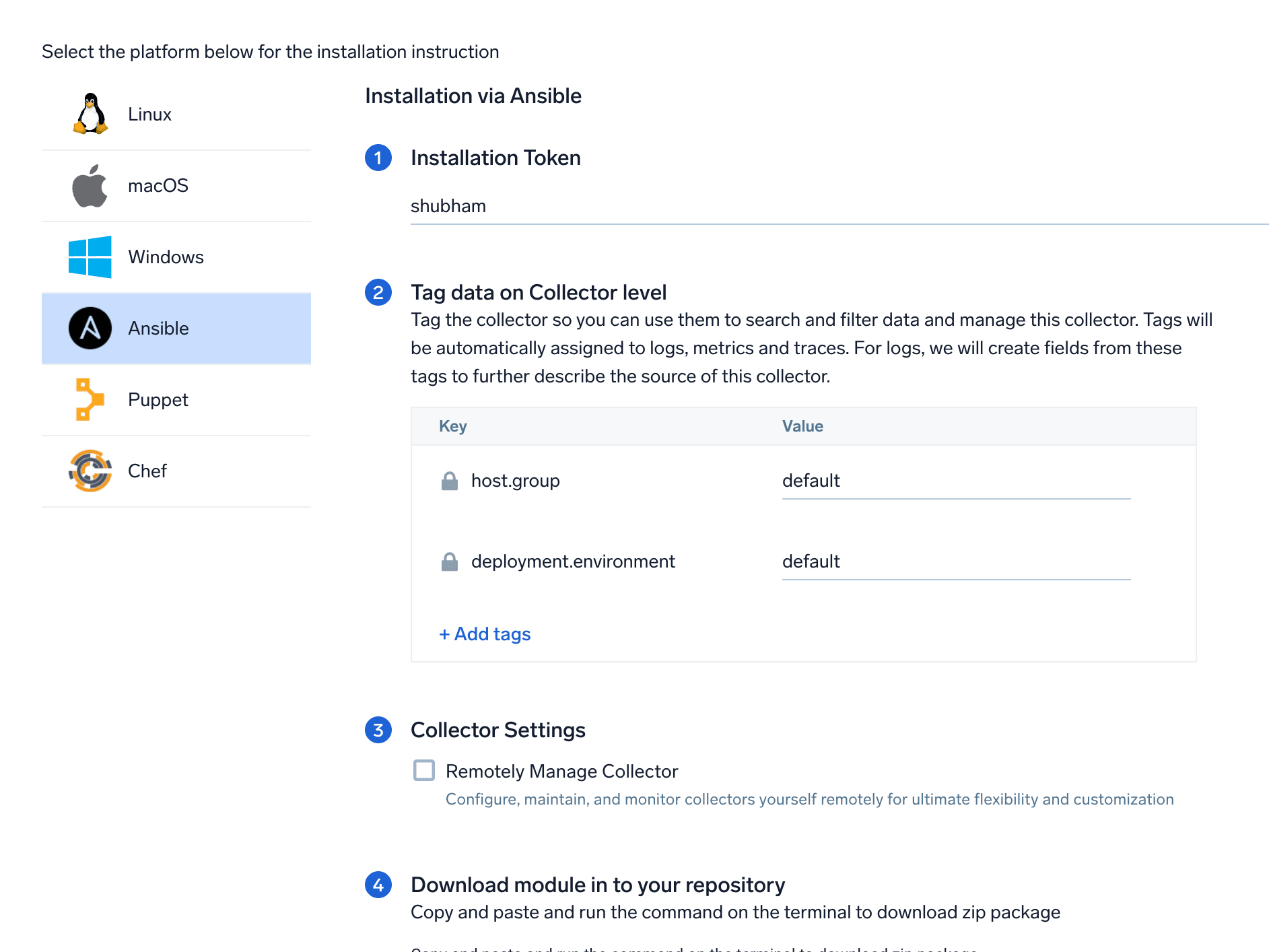
Remote OTEL Collector Management (Platform)
December 11, 2025
We’ve expanded our playbook-based solution for remotely managing OTEL Collectors with two major enhancements:
- Windows OS support: Playbooks now support managing OTEL Collectors running on Windows
- Remote-management install parameter: Install OTEL Collectors in remote-management mode using tools like Ansible, Chef, and Puppet
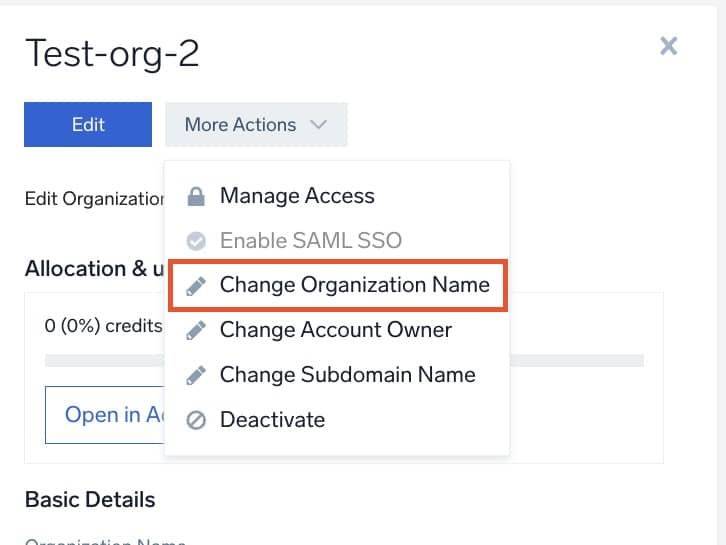
Centralized child org management (Platform)
December 3, 2025
Parent org administrators can now update the Org Name, Subdomain, and Account Owner directly from the Organizations page. This enhancement simplifies administration for multi-org environments, reduces manual effort, and improves overall platform usability.
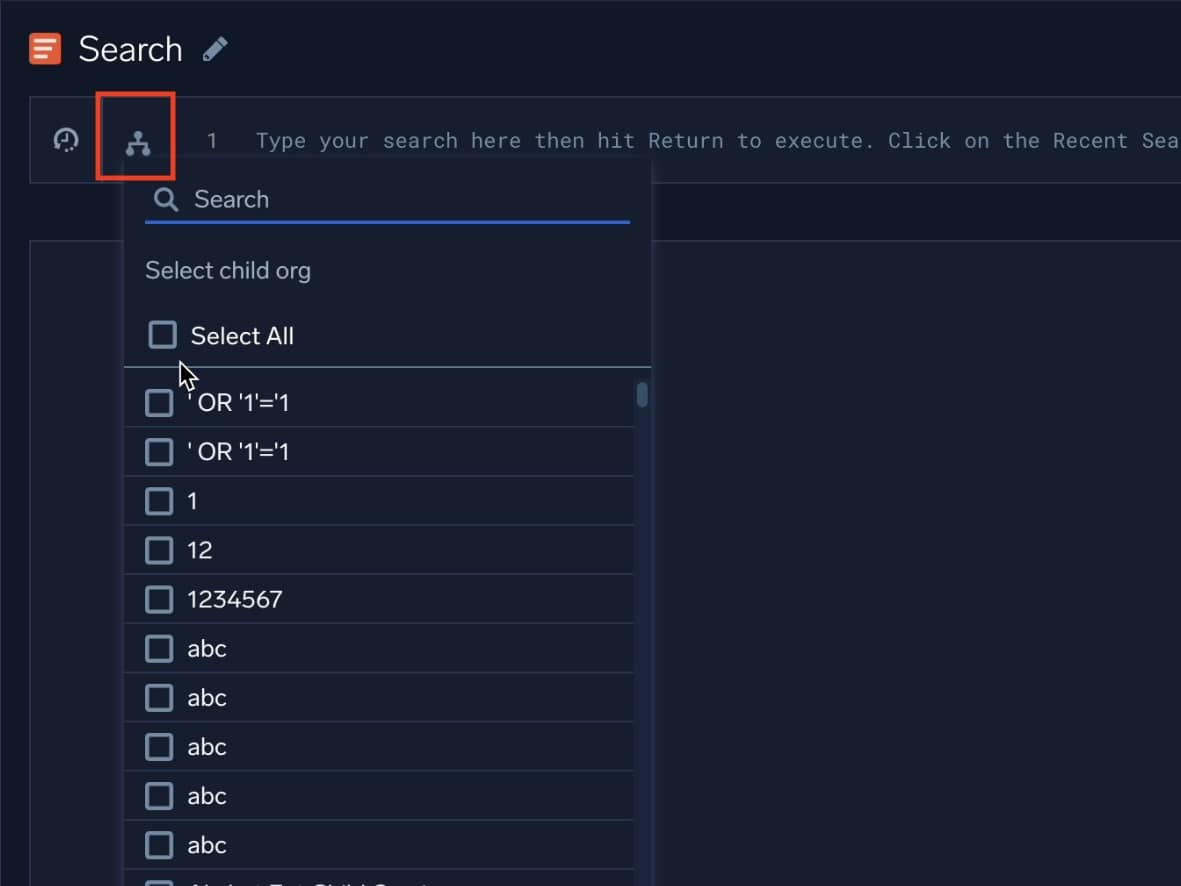
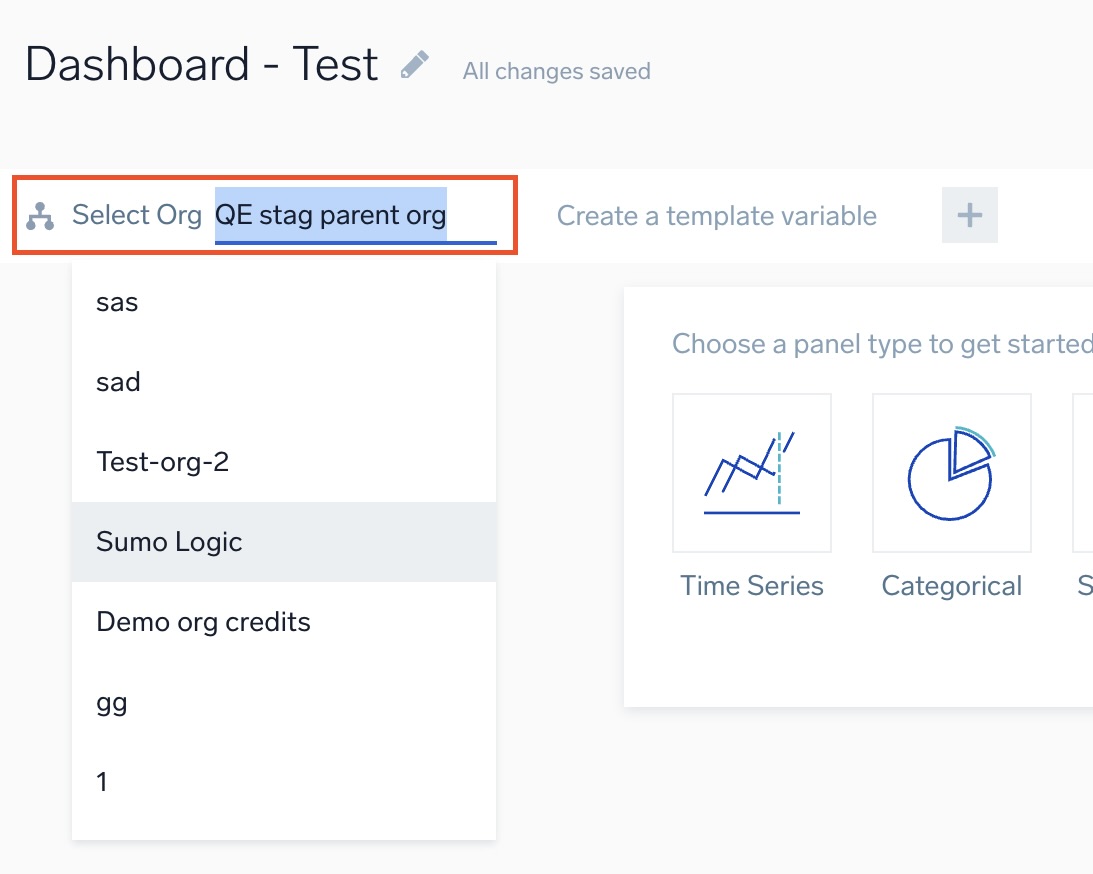
Search and dashboard across multiple child orgs (Platform)
December 2, 2025
You can now run log and dashboard queries across multiple child orgs directly from the parent organization. Previously limited to querying a single child org at a time, this update makes it easier to explore multi-org insights and compare across environments.
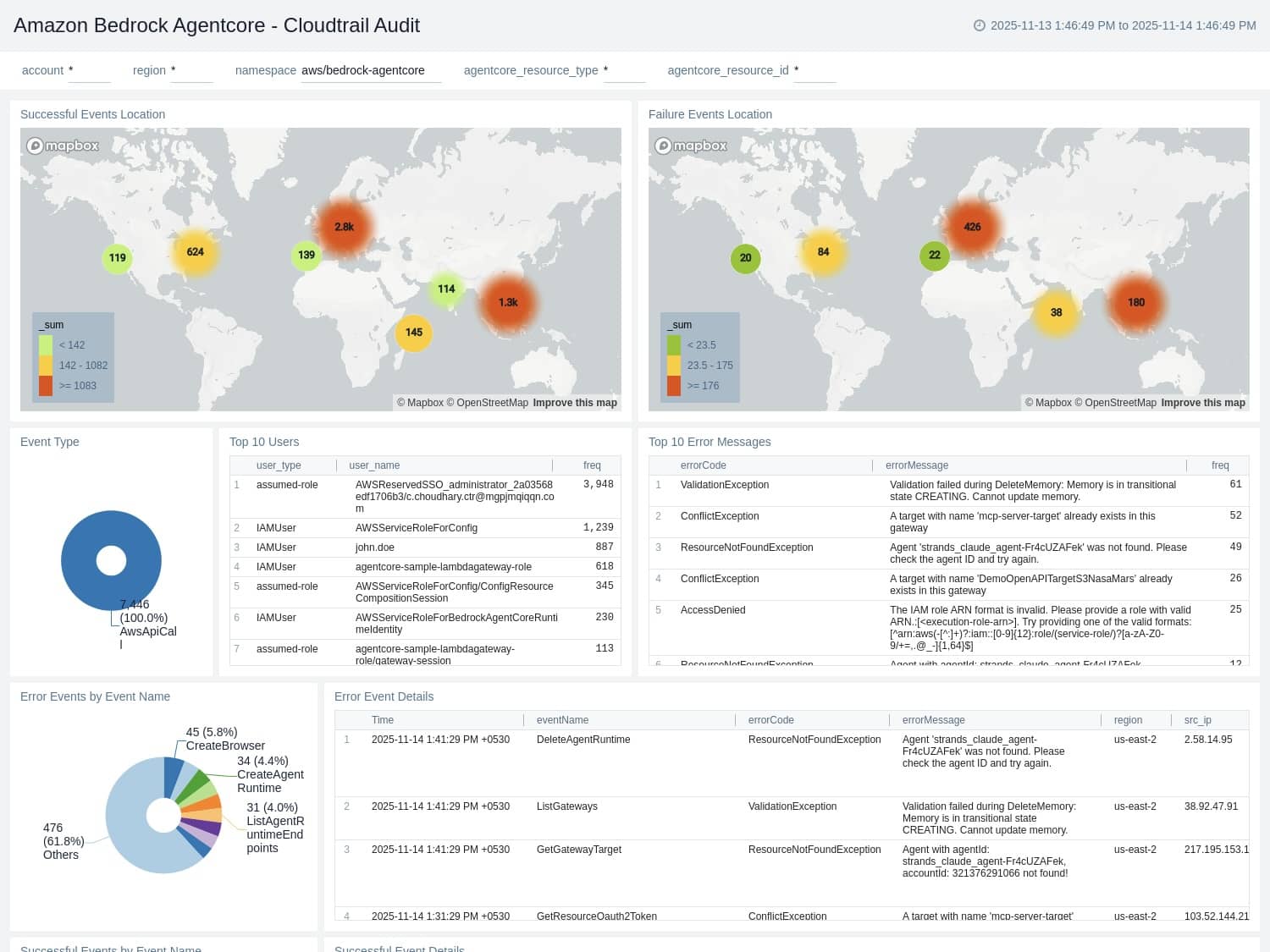
Apps: Amazon Bedrock AgentCore (Platform)
December 1, 2025
The new Amazon Bedrock AgentCore app provides real-time visibility into the performance and behavior of your AI agents built on Amazon Bedrock. The app ingests CloudWatch Logs and performance metrics to give you comprehensive insights into agent runtimes, memory usage, gateways, built-in tools, and identity services. With preconfigured dashboards, you can quickly monitor execution activity, resource utilization, errors, and operational health, making it easier to optimize agent performance, troubleshoot issues, and ensure reliable AI deployments.
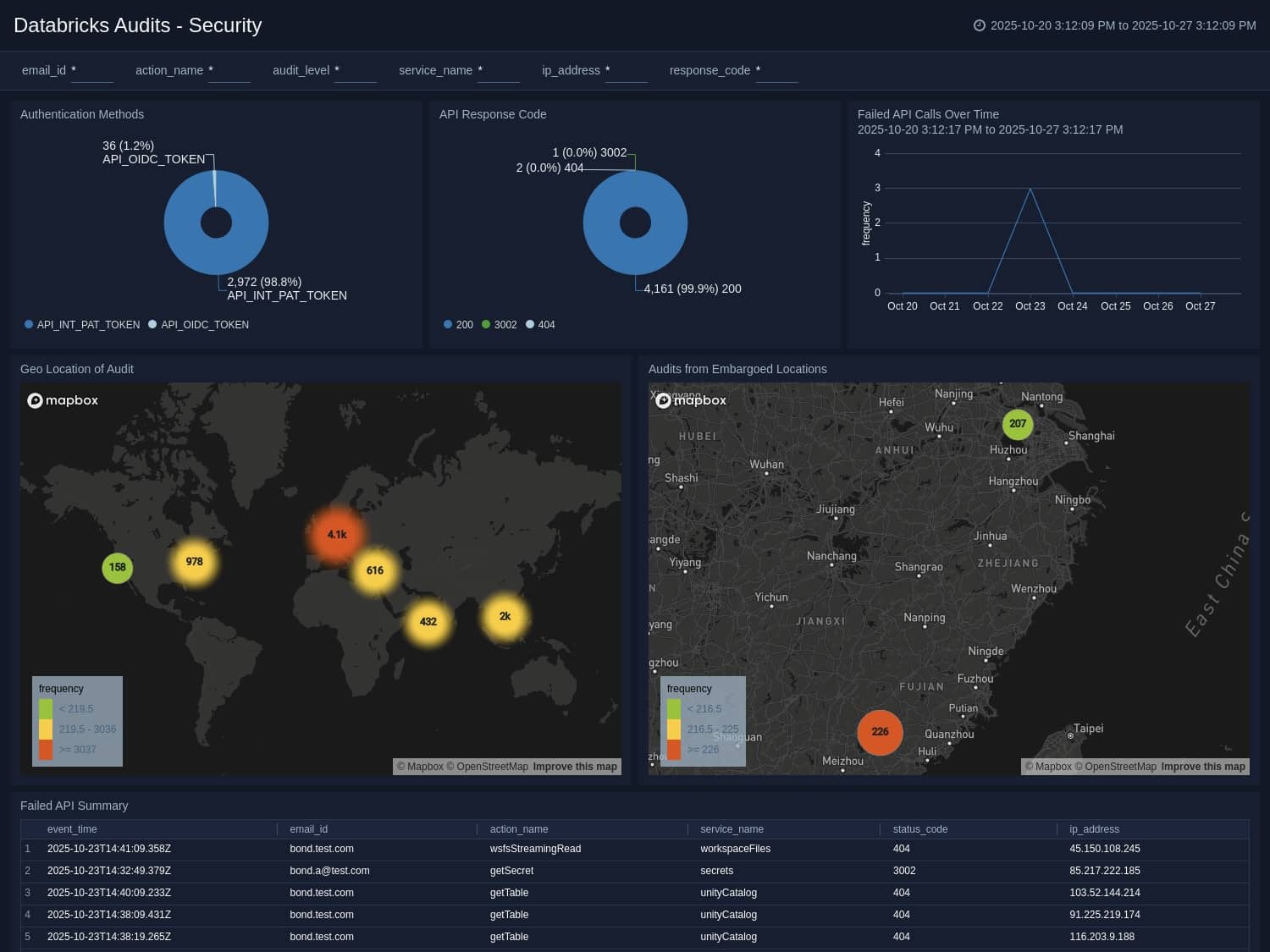
Recent app highlights (Platform)
November 30, 2025
- Varonis: Gain a unified view of Varonis alerts to strengthen threat investigations and accelerate analysis
- GitHub Copilot: Monitor adoption, engagement, and productivity with insights that help optimize AI-assisted development
- Databricks Audit: Analyze audit logs to identify threats, track key trends, and enhance your Databricks security posture
- Zero Networks Segment: Visualize segmentation policies, enforcement actions, and network activity to detect anomalies and validate zero-trust controls
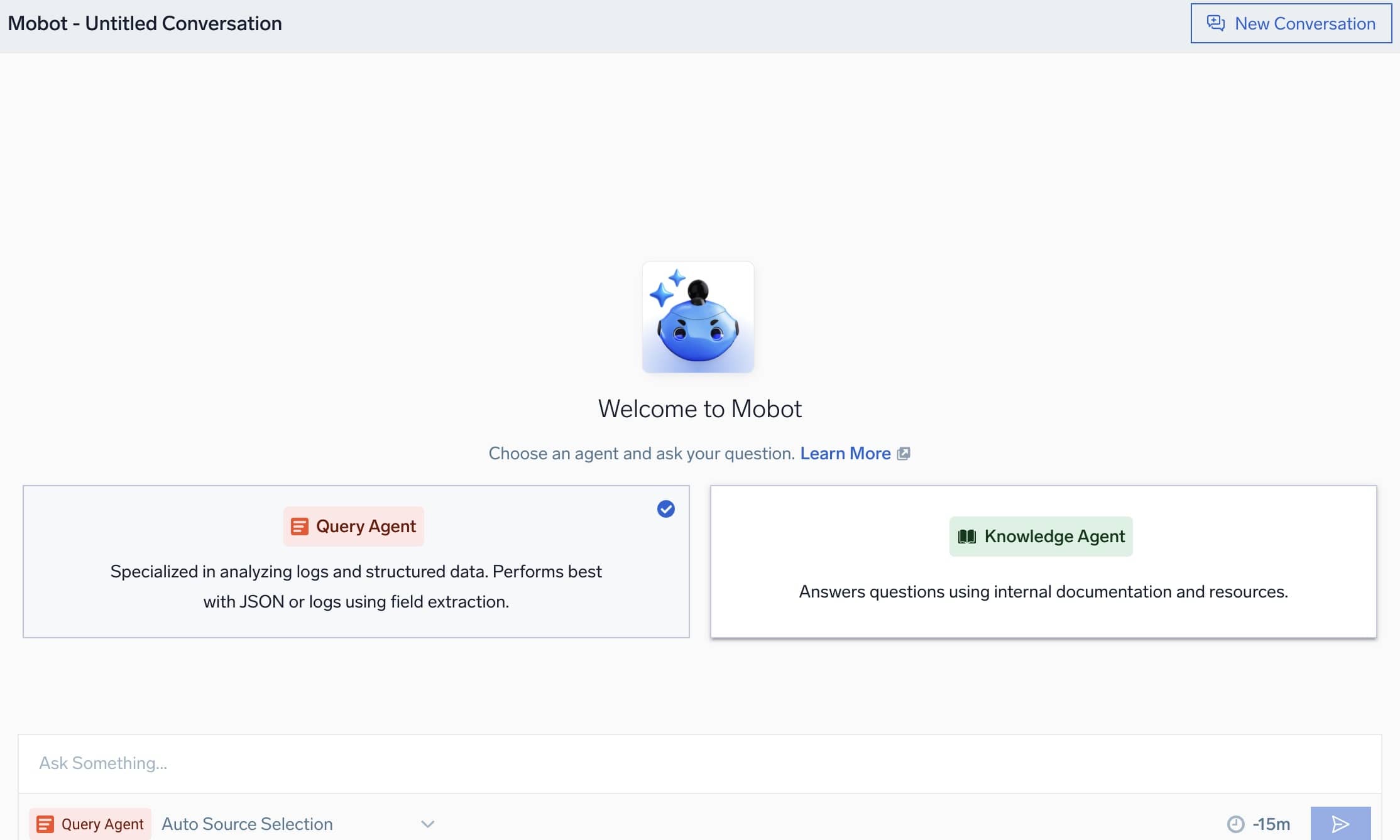
Dojo AI: Mobot, Query Agent, and Knowledge Agent (Platform)
November 26, 2025
Mobot is Sumo Logic’s AI assistant that speeds up troubleshooting and investigation by letting you ask questions in natural language. Mobot connects you to two specialized agents: Query Agent, which translates your questions into log queries and helps refine them, and Knowledge Agent, which answers how-to questions using Sumo Logic’s documentation. Together, they make it easier to explore your data, resolve issues faster, and learn the platform with less friction.
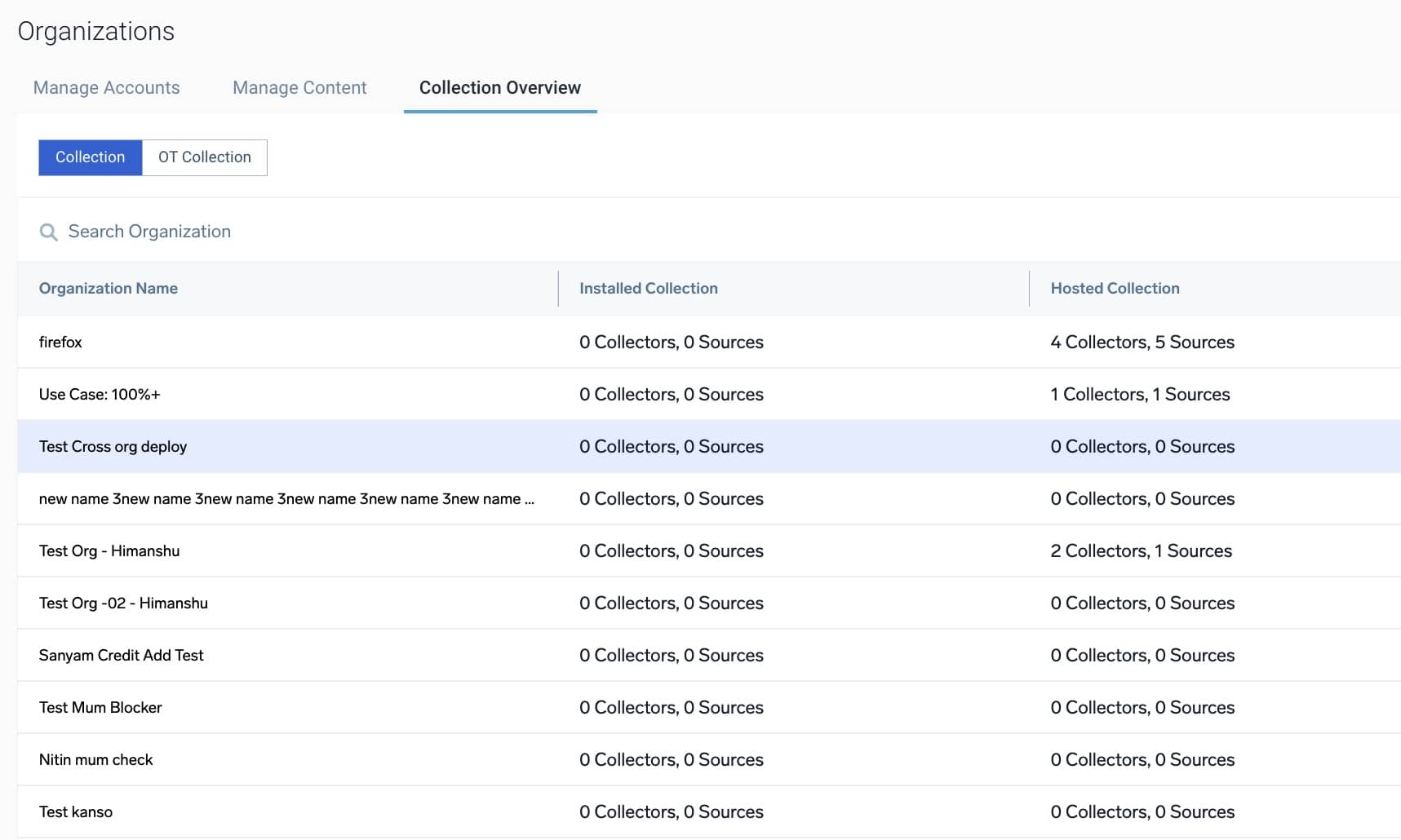
Unified collector visibility (Platform)
November 20, 2025
The new Collection Overview page gives parent-org users a unified view of all Installed, Hosted, and OpenTelemetry collectors across their child orgs. You can quickly assess collector health, drill into specific orgs for deeper analysis, and monitor deployment status in one centralized location.
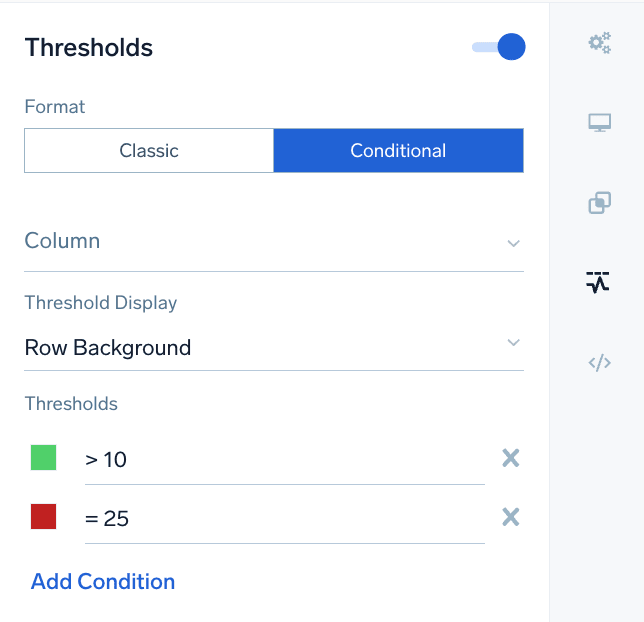
Dashboards: Conditional thresholds (Platform)
November 18, 2025
We’ve added conditional thresholds to table charts, making it easier to spot trends, outliers, and key indicators at a glance. You can now apply flexible color rules to rows and cells, helping you highlight values that exceed defined thresholds and improve dashboard readability.
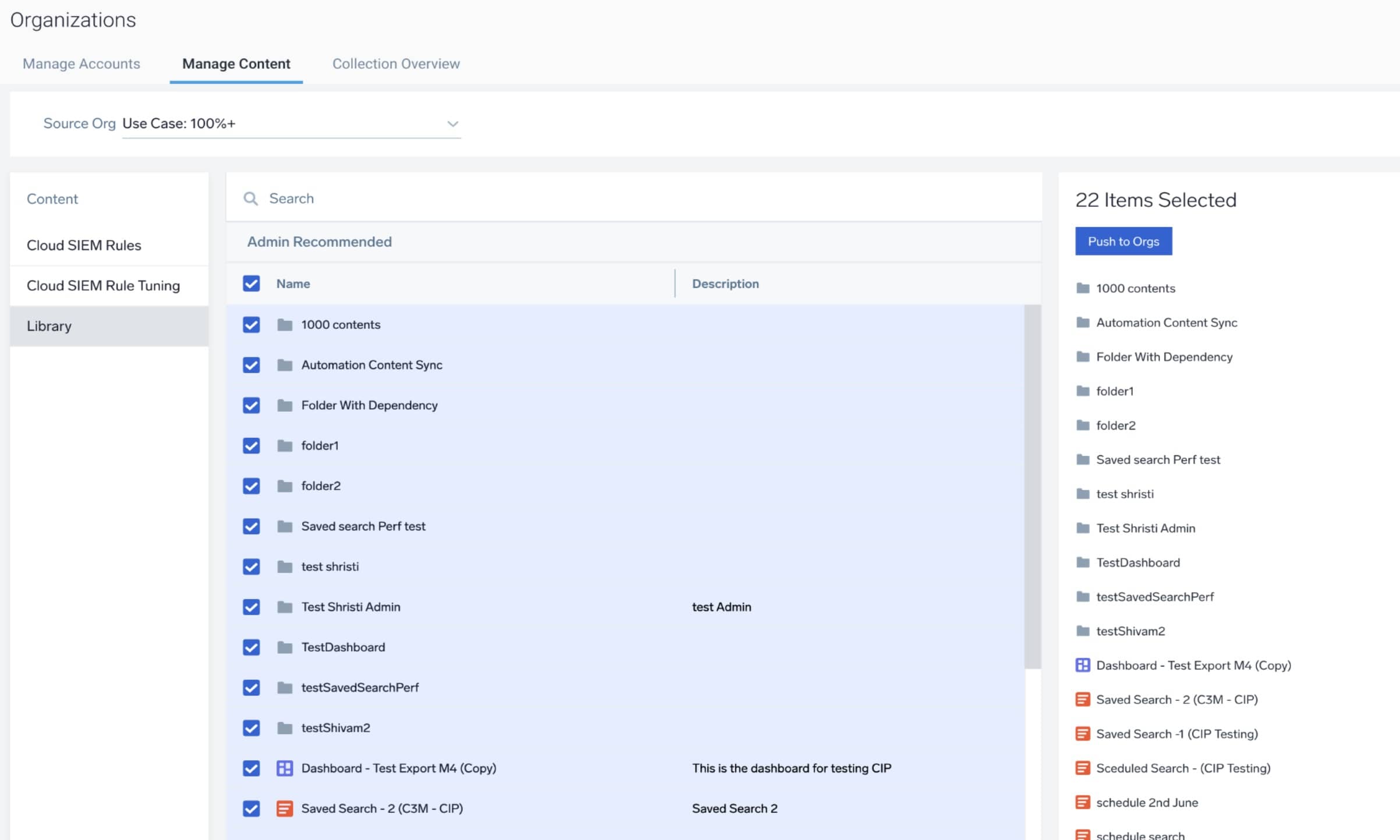
Centralized Content & Configuration Management: Library Content (Platform)
November 11, 2025
Parent org admins can now manage dashboards, saved searches, scheduled searches, connections (email & webhooks), and library folders across child orgs directly from the parent organization without logging in and out of each child org. This update streamlines content administration, reduces manual effort, and ensures faster, more consistent deployment across environments.
Terraform Support for Playbooks (Automation Service / Cloud SOAR)
November 7, 2025
Users can now deploy, update, delete, and import playbooks using Terraform while preserving existing roles-based access controls (RBAC) and receiving audit logs for all actions. This allows playbooks to be treated as code and managed consistently across environments.
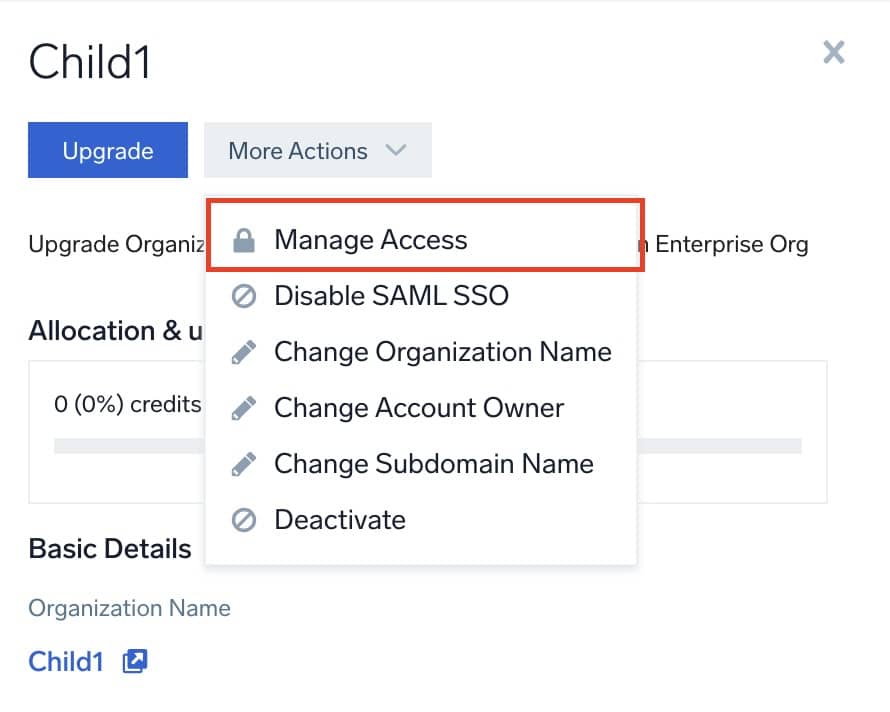
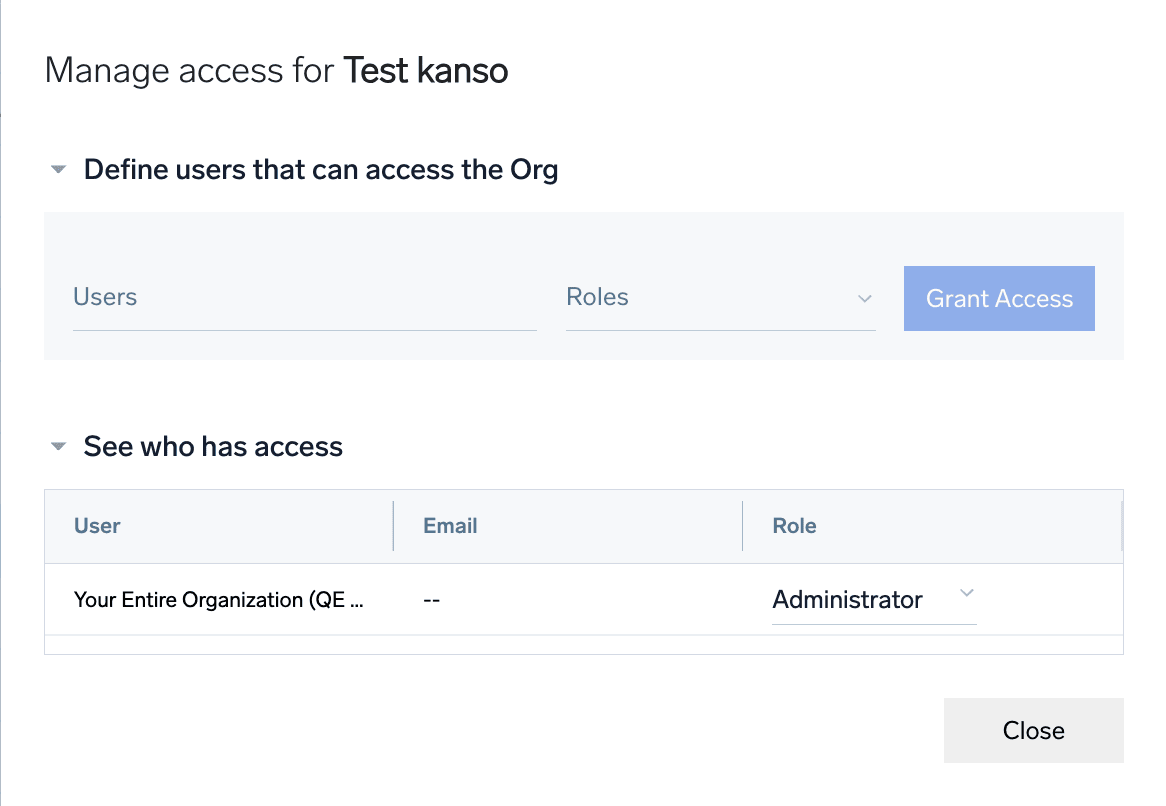
Manage access to child orgs (Platform)
October 6, 2025
Parent org admins can now configure which users can view and SSO into individual child organizations, giving admins precise control over who can sign in where. This update enhances security by ensuring only authorized personnel can access sensitive child org data.
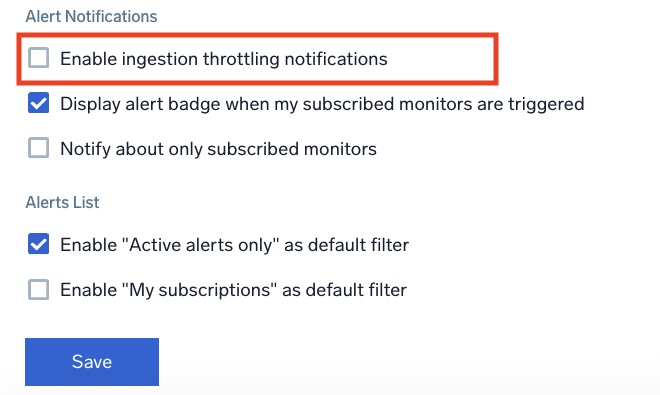
Ingestion Throttling Limits Visibility & Notifications (Platform)
October 6, 2025
We’re making it easier to monitor and manage your data ingestion limits. You can now:
- See usage at a glance: View organization-level usage and scan budgets directly in the platform.
- Stay informed with alerts: Opt in to receive email notifications when ingestion approaches or exceeds your plan thresholds.
These updates give you better visibility, help prevent throttling, and let you take action before limits impact operations.
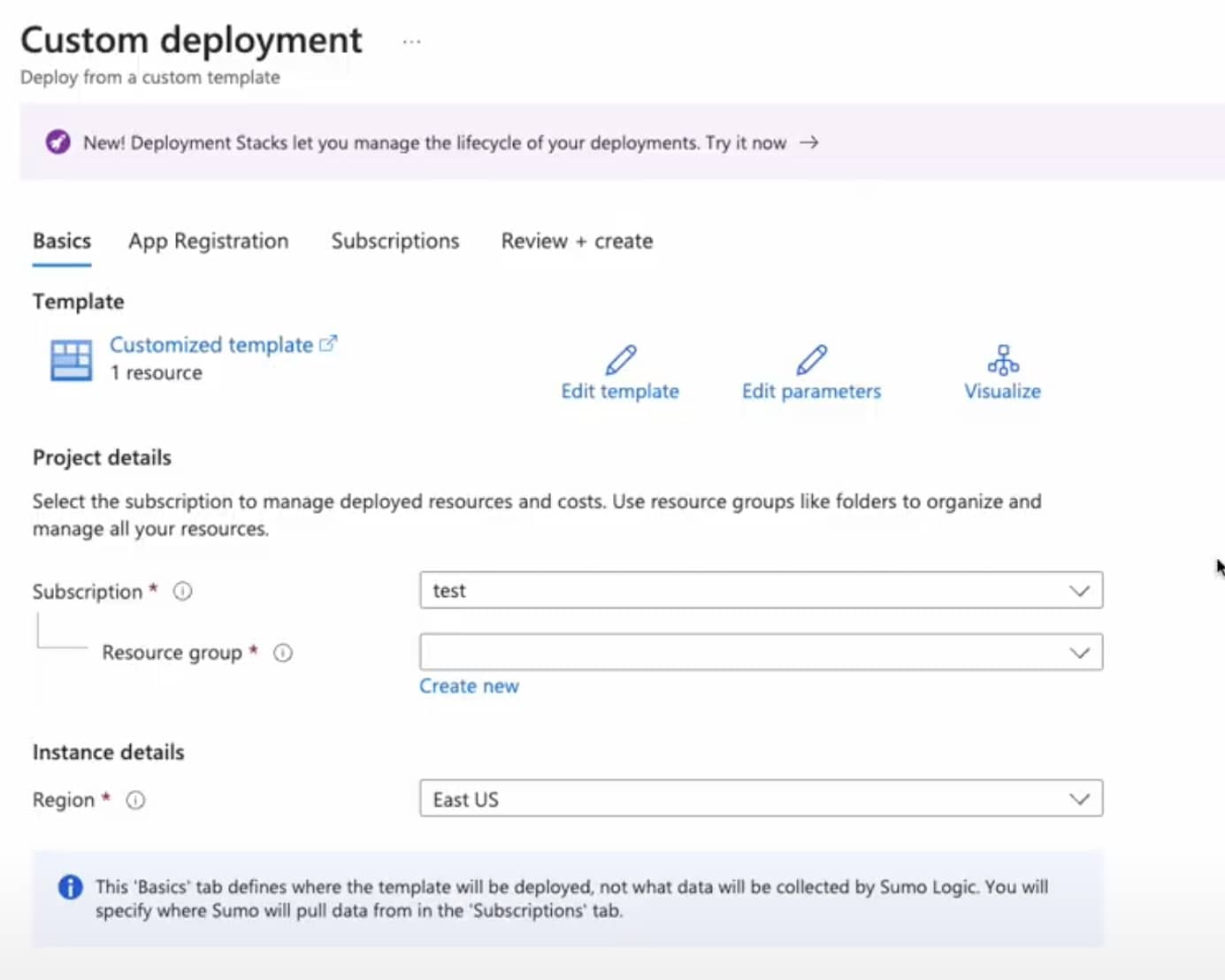
Data Collection: New Azure metrics source (Platform)
September 19, 2025
We’ve moved to a new Azure API-based solution that automates data collection. No more manual management of ARM templates, serverless functions, or addressing CVEs and bug fixes. With automatic updates, your team can spend less time maintaining your data collection and focus on important value-add activities. Onboarding new metrics is now faster and easier, and richer metadata means deeper insights into your Azure environments.
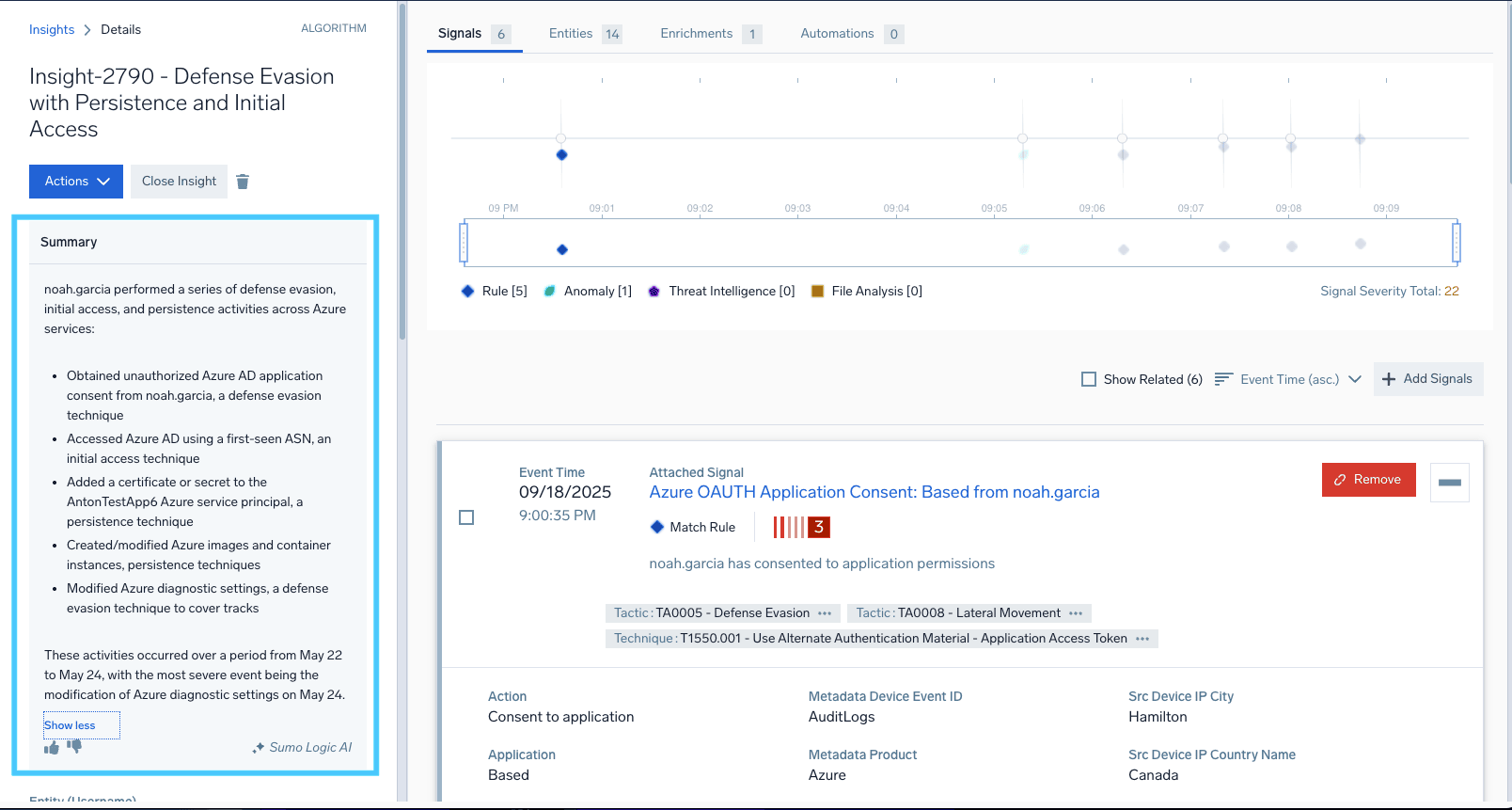
Dojo AI Summary Agent (Cloud SIEM)
September 22, 2025
The Summary Agent generates AI-driven summaries of signals within an Insight, so analysts no longer need to sift through raw logs or events. By reducing noise and highlighting key context, it speeds up triage, improves collaboration, and clarifies why an Insight was triggered.
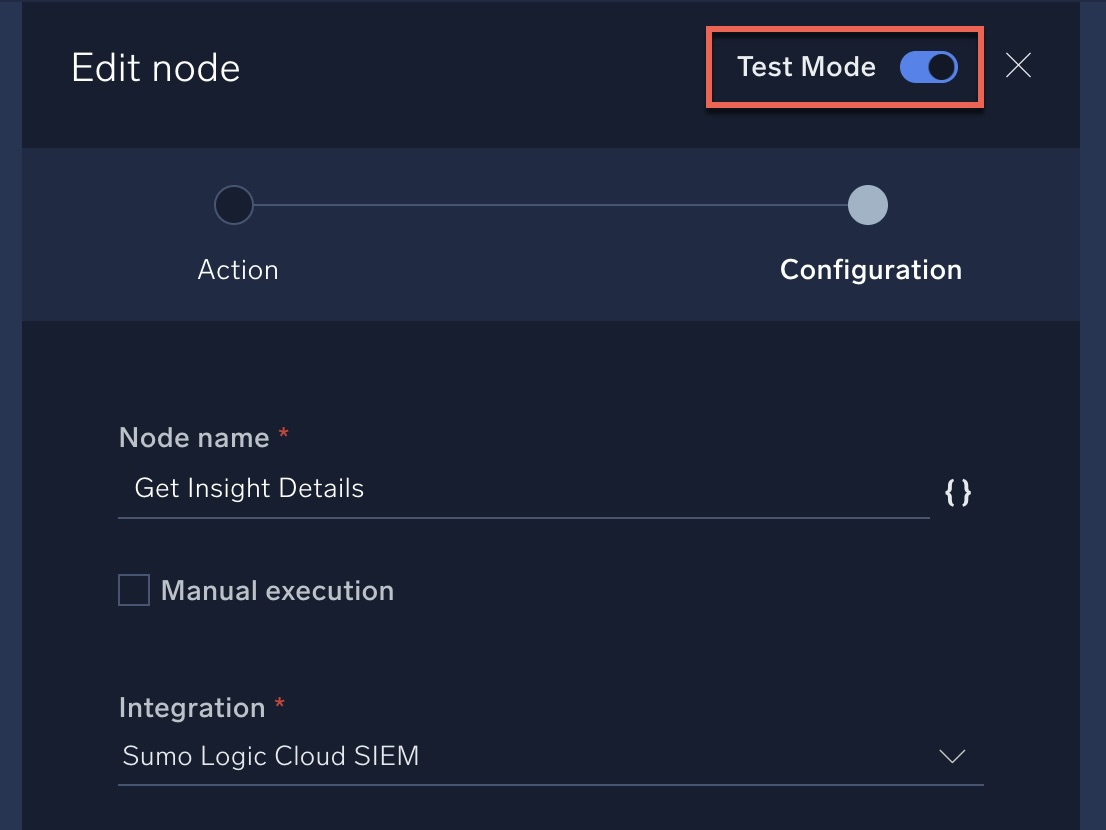
Playbook testing enhancements (Platform & Cloud SOAR)
September 10, 2025
You can now test a single playbook node without configuring the entire flow and provide mock values to see outputs and errors instantly. The Variable Panel lets you track inputs, outputs, and variable changes in real time—helping you configure playbooks faster and ensure they run reliably.
Child org search and dashboard (Platform)
September 8, 2025
As part of our ongoing commitment to enhancing the platform for customers with complex multi-org structures including MSSPs, we’ve introduced the ability for administrators to query data and manage dashboards from any of their child orgs directly from the parent search page.
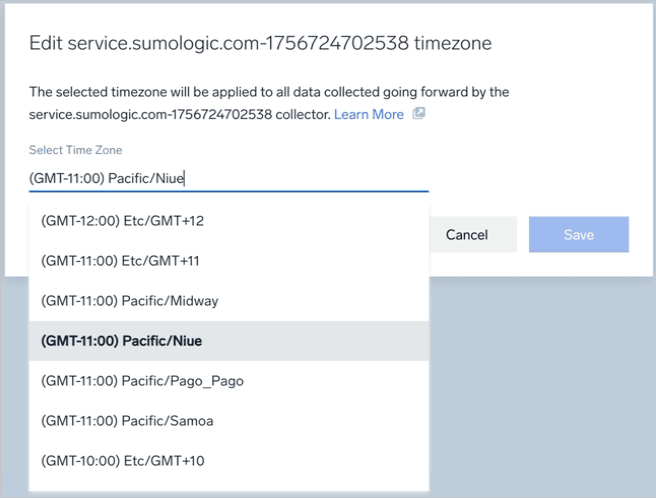
OTEL: Remotely update collector time zone (Platform)
September 8, 2025
You can now update the timezone for OpenTelemetry (OTel) collectors directly from the UI, just like Installed Collectors. This makes managing collectors easier, ensures log timestamps are accurate, and reduces manual effort during onboarding and maintenance.
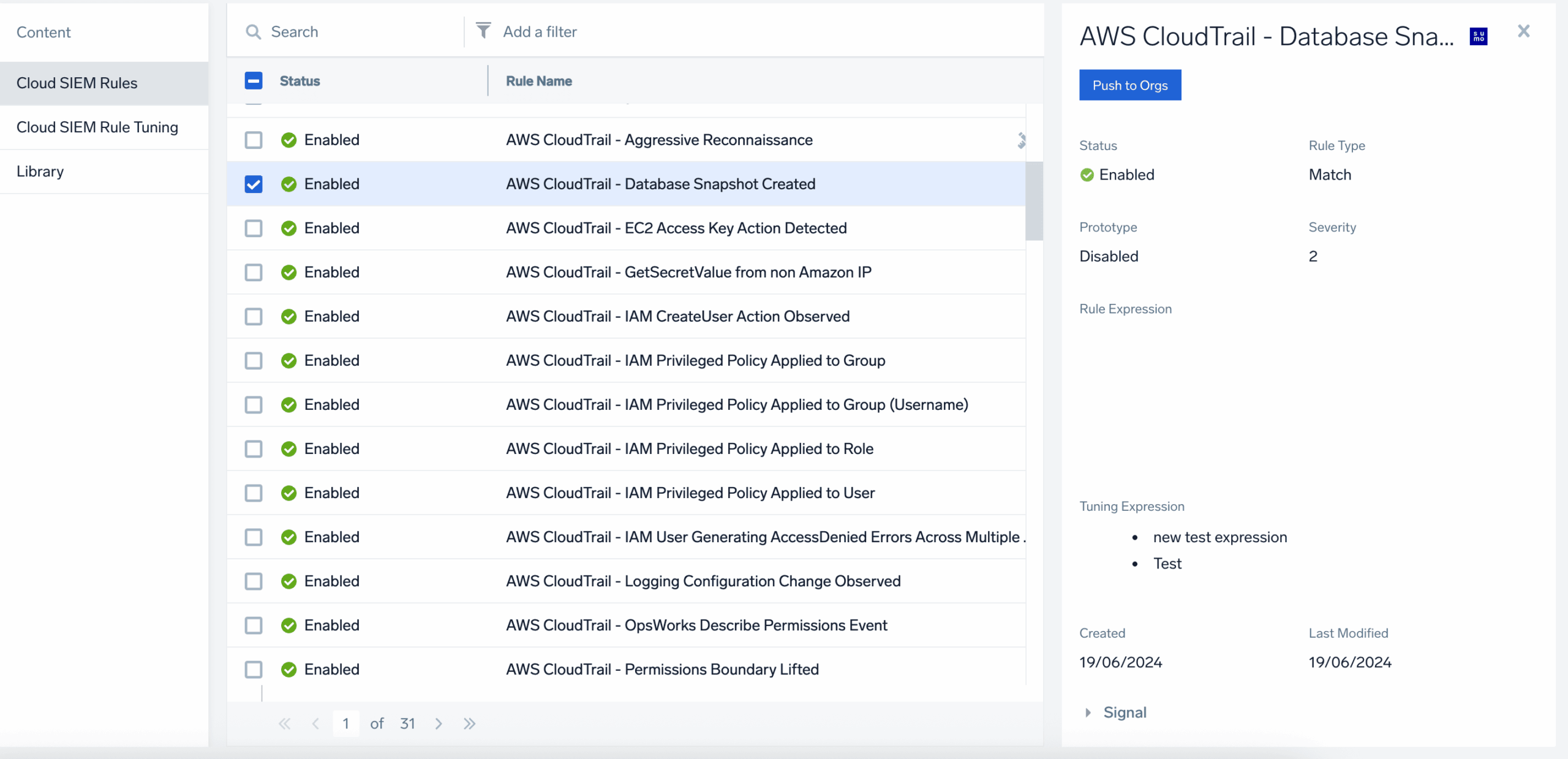
Centralized Content & Configuration Management: Rules & Tuning Expressions (Cloud SIEM)
September 4, 2025
Managing Cloud SIEM rules and tuning expressions across multiple child orgs just got easier. With Centralized Content & Configuration Management (C3M), parent org admins can create, update, and deploy rules to multiple child orgs with a single click, preserving all settings and logic. This reduces manual work, prevents errors, and ensures consistent security policies across your environments.
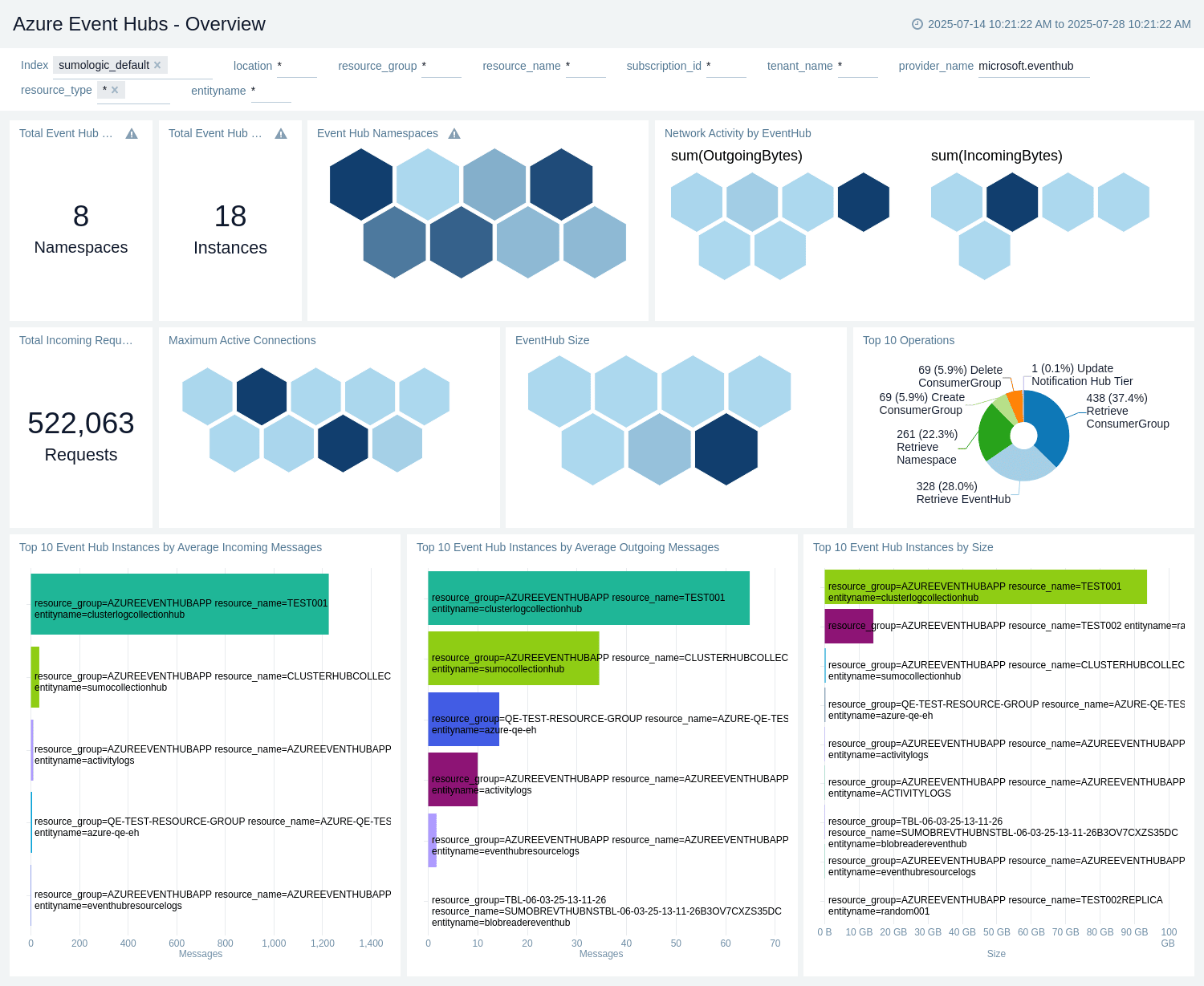
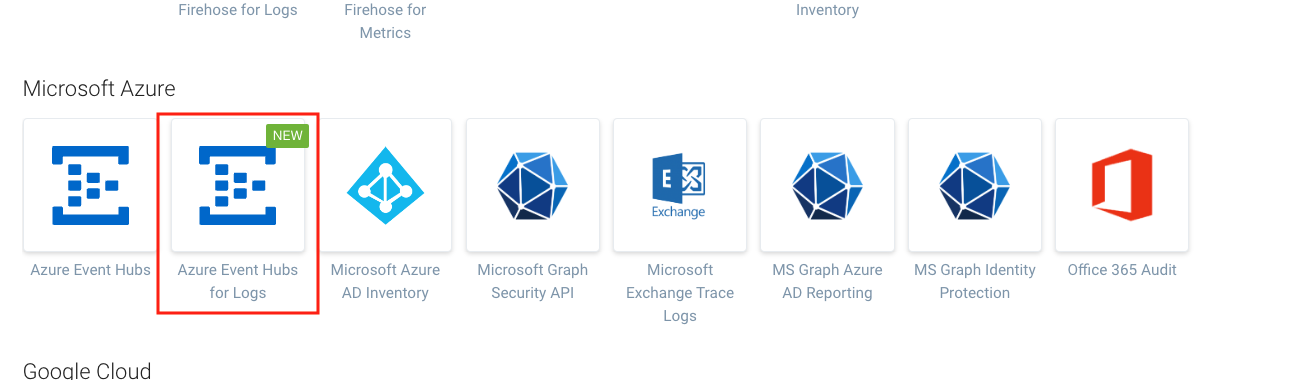
New Azure Apps (Platform)
September 4, 2025
We’ve added two new apps for monitoring and troubleshooting Azure environments:
- Azure Event Hubs: Track data plane operations such as sending/receiving events, monitor performance metrics including consumer lag, throughput, and active connections.
- Azure Machine Learning: Monitor compute resources (CPU/GPU), training runs, model deployments, pipeline events, and policy recommendations. Gain visibility into resource utilization and data plane operations to troubleshoot and optimize your ML workloads.
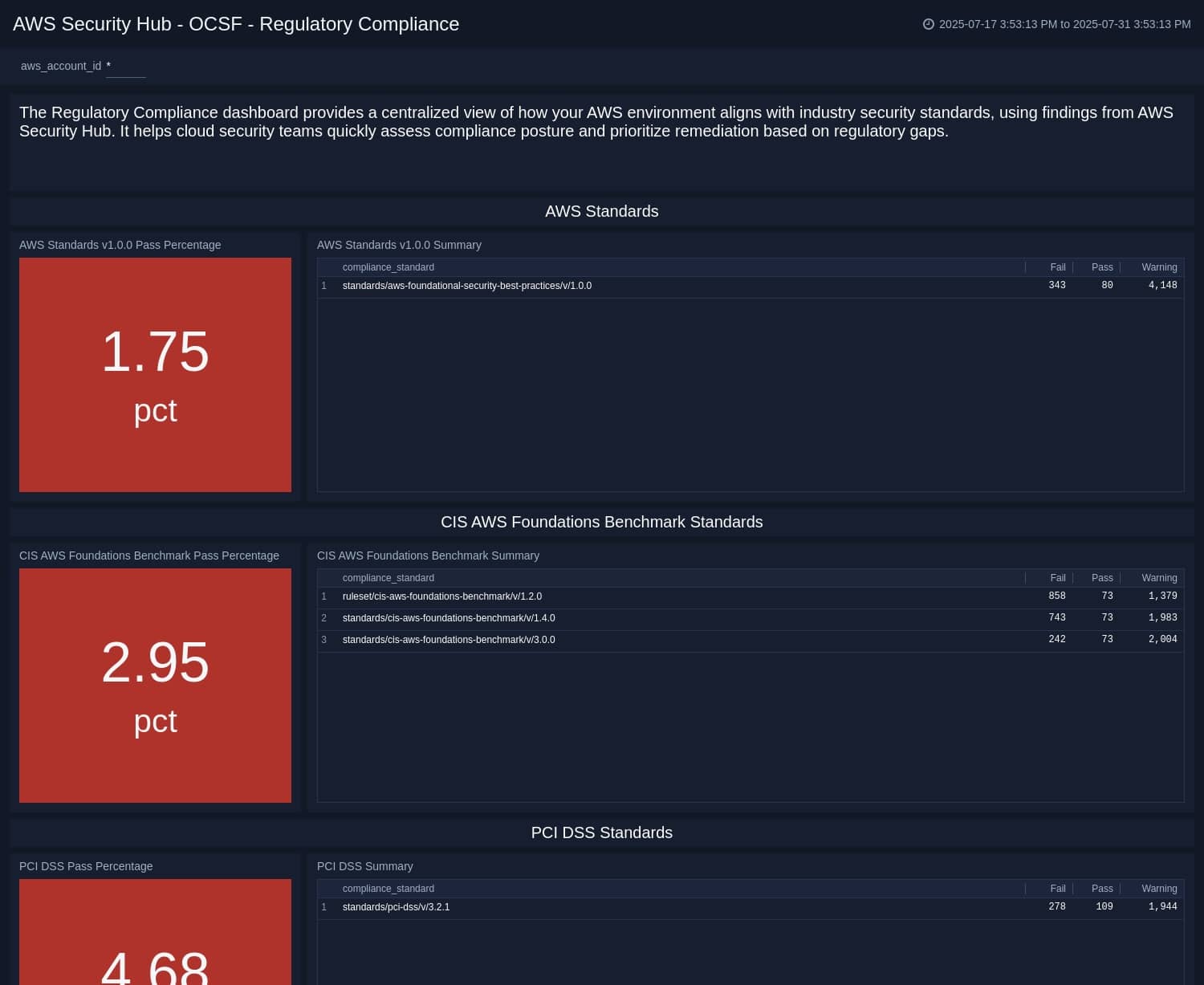
AWS Security Hub – OCSF (Platform)
August 31, 2025
This new app offers a centralized, structured view into your AWS security findings using the Open Cybersecurity Schema Framework (OCSF). Identify threats, track compliance violations, and investigate affected resources with speed and clarity.
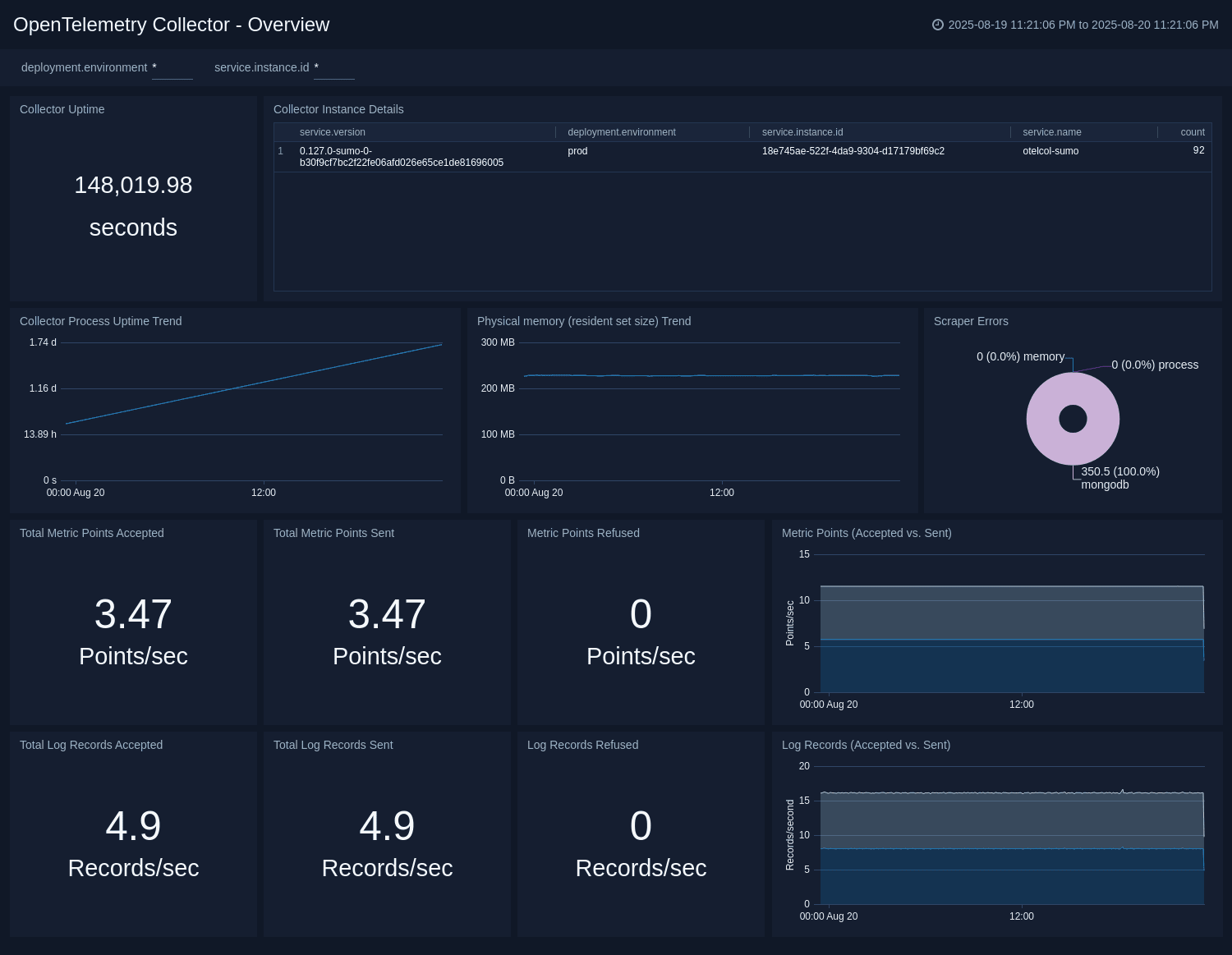
Recent app highlights (Platform)
Aug 29, 2025
- AWS IAM Users: Monitor and analyze user-related data to optimize security practices and maintain compliance within your AWS account.
- OpenTelemetry Collector Insights: End-to-end monitoring for your OTel Collector instances, with preconfigured dashboards and alerts to track performance, data flow, and resource utilization.
- Zimperium: Gain visibility into mobile threats by centralizing threat intelligence and device telemetry, collecting threat logs for analysis in Sumo Logic.
- ExtraHop RevealX 360: Monitor detection trends, track risk changes, and get insights into frequently observed MITRE techniques, top devices, and key network targets.
- Vectra: Monitor security threats detected across networks, cloud environments, and endpoints.
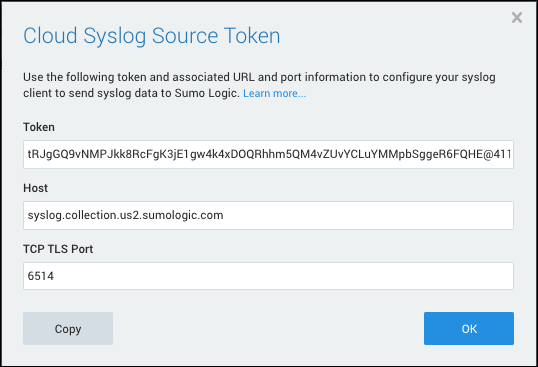
Cloud Syslog Source Certificate Transition to ACM (Platform)
August 1, 2025
We’re transitioning to AWS Certificate Manager (ACM) certificates for TLS communication between your cloud syslog sources and Sumo Logic. ACM removes the need for future manual certificate renewals, reducing administrative overhead and simplifying management within your AWS infrastructure.

Query Assist (Platform)
July 18, 2025
Query Assist streamlines the query-building process by offering real-time syntax suggestions, schema prompts, and partial query predictions. This enhancement speeds up query creation for both new and experienced users, reducing the learning curve and minimizing errors, so users can get insights faster and more accurately.
Deactivate and Delink Child Orgs (Platform)
June 20, 2025
Managing multi-entity organizations is a common need for many Sumo Logic customers. This update empowers administrators to deactivate and delink child organizations independently, eliminating the need to submit support tickets for cleaning up unneeded child accounts. With this improvement, admins can streamline account management and maintain a cleaner, more efficient organization structure.


Recent app highlights (Platform)
June 19, 2025
- Amazon RDS Proxy: This updated app provides enhanced insights into RDS Proxy health and performance, including connection pooling, failover events, and database performance. Proactively track connections to minimize risks and ensure smooth application operation.
- Confluent Cloud: This new app offers deep insights into Confluent Cloud performance, including Kafka performance, consumer lag, producer latency, and connector health. Pre-configured dashboards enable proactive troubleshooting and optimized data streaming.
- Snyk: Gain visibility into security vulnerabilities across software projects and dependencies. Snyk helps security and DevOps teams track risk, prioritize remediation, and maintain a strong security posture with real-time vulnerability detection.
- Google Cloud Security Command Center: Analyze, monitor, and respond to security issues in Google Cloud environments with this new app, improving security, reducing risk, and maintaining compliance.
- Microsoft Defender for Endpoint: The new app provides real-time visibility into security alerts across software projects, helping teams track risk, prioritize remediation, and maintain a strong security posture for endpoint protection.
Dashboard Scope-Based Variables (Platform)
June 18, 2025
Scope-Based Variables are a new dashboard variable type that act as log filters, enabling users to easily apply data filters across multiple panels without manually editing each panel’s query. These variables can be set as the default data scope for a dashboard, automatically applying to all or selected panels for streamlined, consistent filtering across your dashboard.

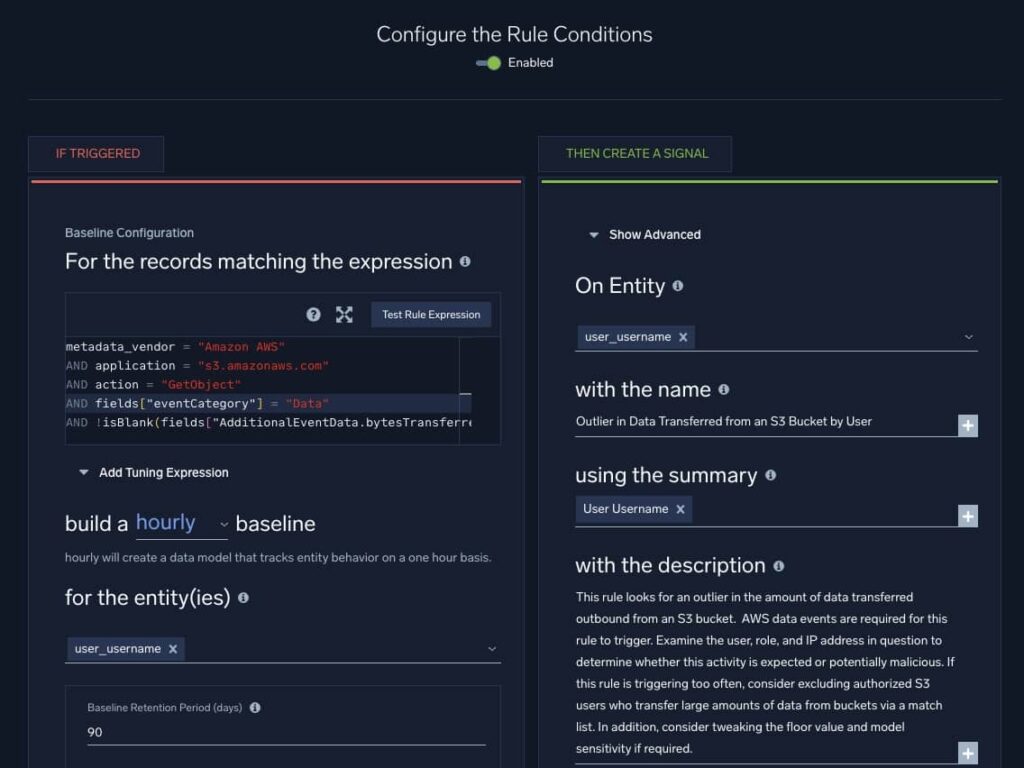
New method for building baselines (Cloud SIEM)
June 12, 2025
With this update, baselines now start building immediately using existing system data when you create or update a first-seen or outlier rule, typically becoming ready within minutes. This change accelerates insights and reduces tuning time from weeks to minutes, enabling faster iteration on your rules.
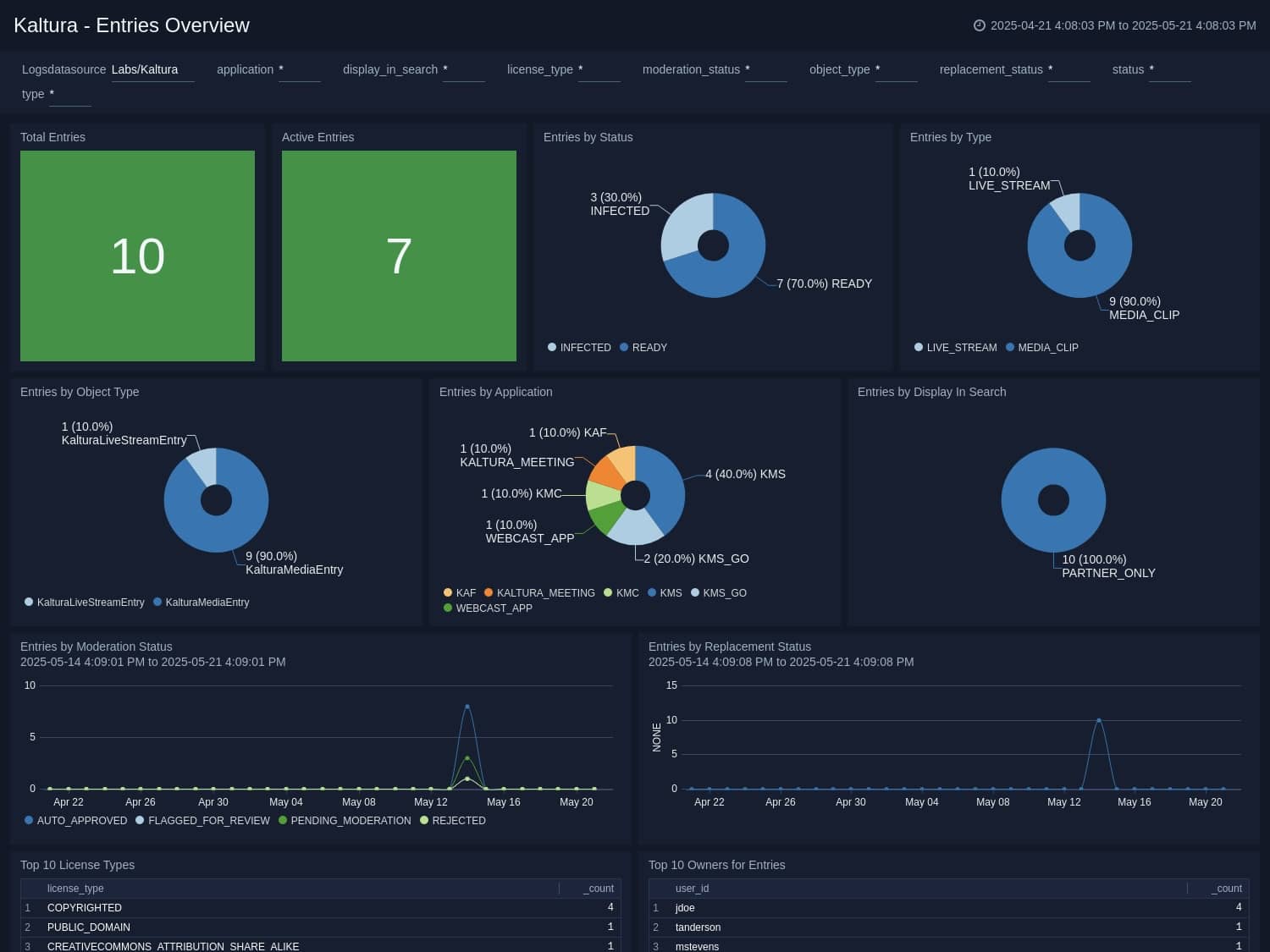
Recent app and cloud-to-cloud highlights (Platform)
June 11, 2025
- Kaltura: This new app provides insights into key content management metrics, including user activity trends, event distributions, and total entries, helping you monitor, secure, and optimize your content strategies.
- Bitwarden: This new app enhances threat detection and helps identify high-risk events, such as vault exports or SSO deactivation, accelerating incident response for credential and secret management workflows.
- Sysdig Secure: This new app offers real-time insights into vulnerabilities, compliance, and threats, enabling rapid response and continuous security for your Kubernetes and containerized environments.
- Gigamon Application Metadata Intelligence: This updated app includes new security-focused dashboards, including HIPAA Network, PCI Compliance, DevOps API Inventory & Network Insights, DNS & Web Traffic Insights, URL Analysis for Threat Detection, and Rogue Activity. These dashboards provide enhanced visibility into compliance, network behavior, and potential threats to improve security.
- Snowflake (C2C): A new cloud-to-cloud source for Snowflake Logs collects row data from unsupported global tables and sends them to Sumo Logic for analysis.
- Akamai (C2C): A new cloud-to-cloud source for Akamai CPC collects CPC-Configs, CPC-Alerts, and CPC-Alert Details data for analysis in Sumo Logic.
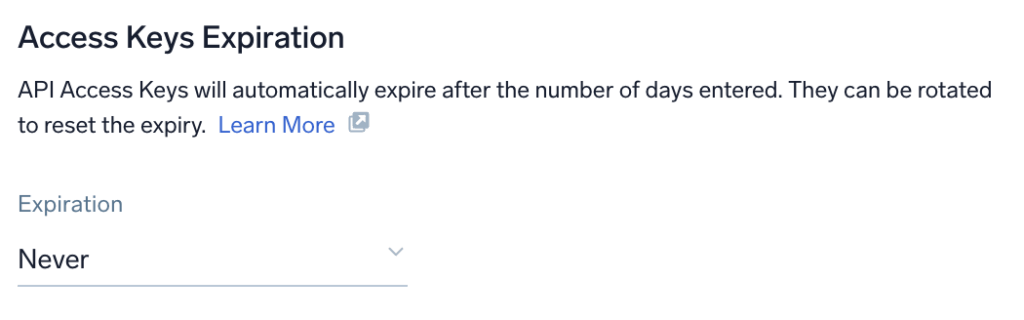
Access keys: Rotation (Platform)
May 29, 2025
This update enables administrators to define both the maximum lifetime and rotation frequency of API access keys. It ensures periodic rotation and automatic deactivation or expiration of keys that exceed their allowed lifetime, enhancing security through regular updates.
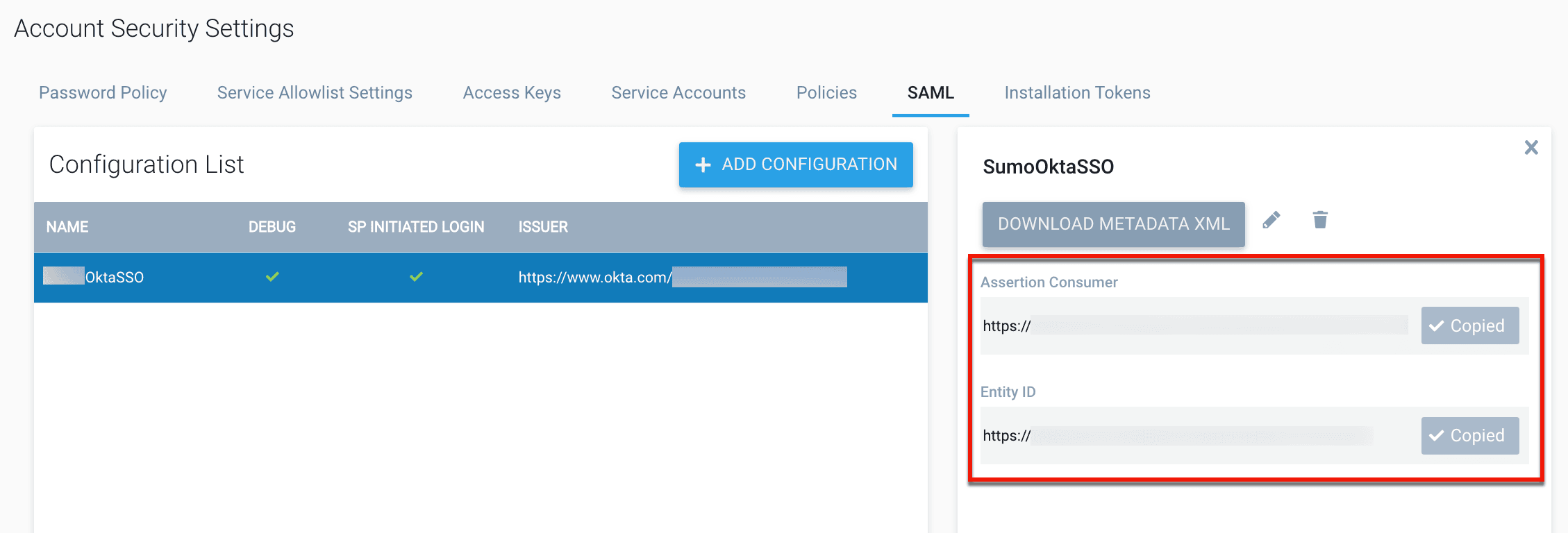
SCIM provisioning (Platform)
May 8, 2025
Sumo Logic now supports System for Cross-domain Identity Management (SCIM) APIs, automating the provisioning, updating, and de-provisioning of user accounts across connected systems. Integration with identity providers like Microsoft Entra ID, Okta, or OneLogin ensures consistent access control and secure lifecycle management.
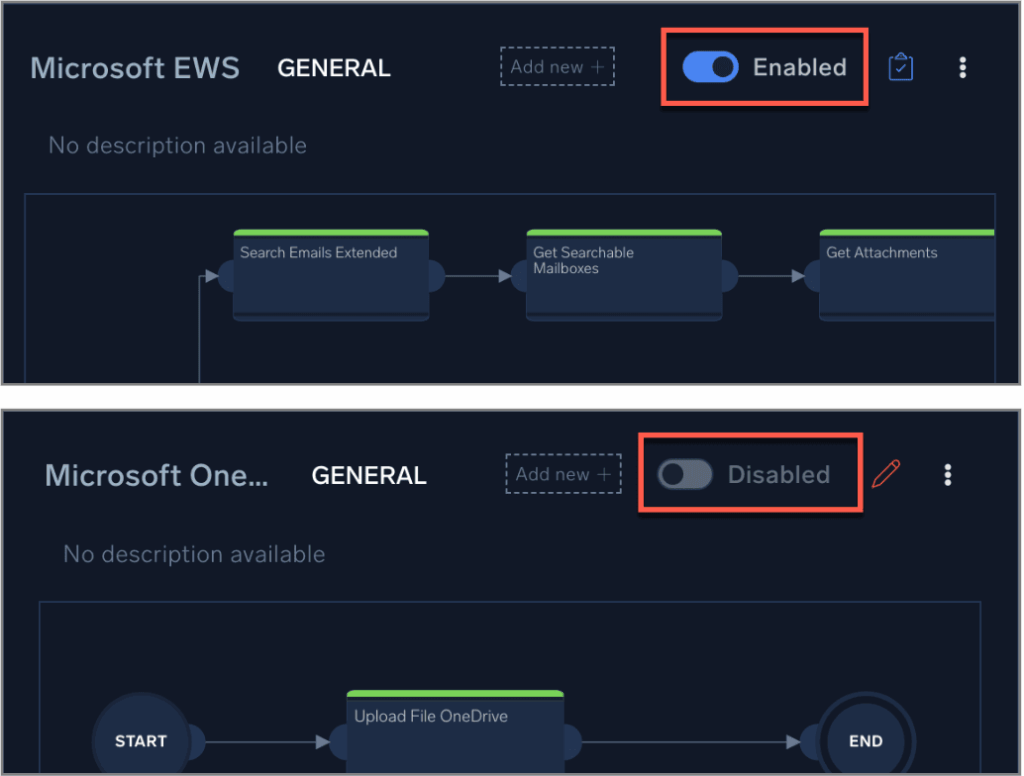
Playbook enable/disable (Platform)
May 6, 2025
This new feature allows you to manually enable or disable playbooks for use in automation. If a playbook causes issues, such as exceeding actions limits or sending too many emails, you can temporarily disable it instead of deleting it. This adds flexibility in managing workflows and improves operational efficiency during incident response.
AWS Observability Solution v2.12.0 (Platform)
May 1, 2025
This release updates nine apps and four monitors to integrate with the new Threat Intel feed, and migrates 28 classic apps to next-gen versions for easier management. We also released an FAQ section with 14 OTRM Source Templates to simplify the creation and deployment of OpenTelemetry configurations, letting you collect and send logs and metrics from various systems directly to Sumo Logic.
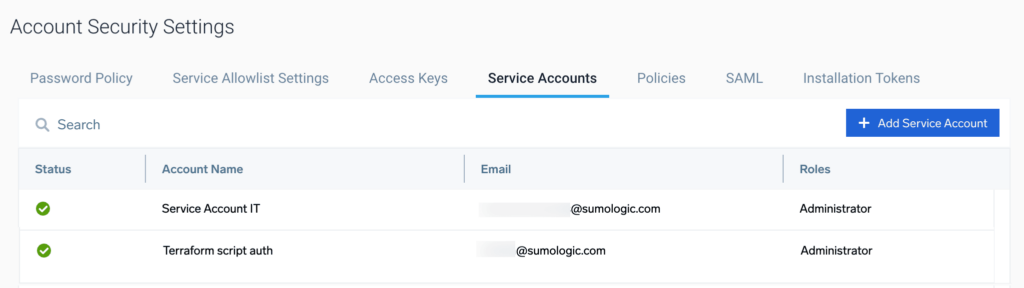
Service accounts (Platform)
May 1, 2025
Service accounts let administrators create non-interactive accounts for managing API keys, ensuring uninterrupted API integrations even when users are offboarded. This feature improves operational continuity by decoupling API access from individual user accounts.
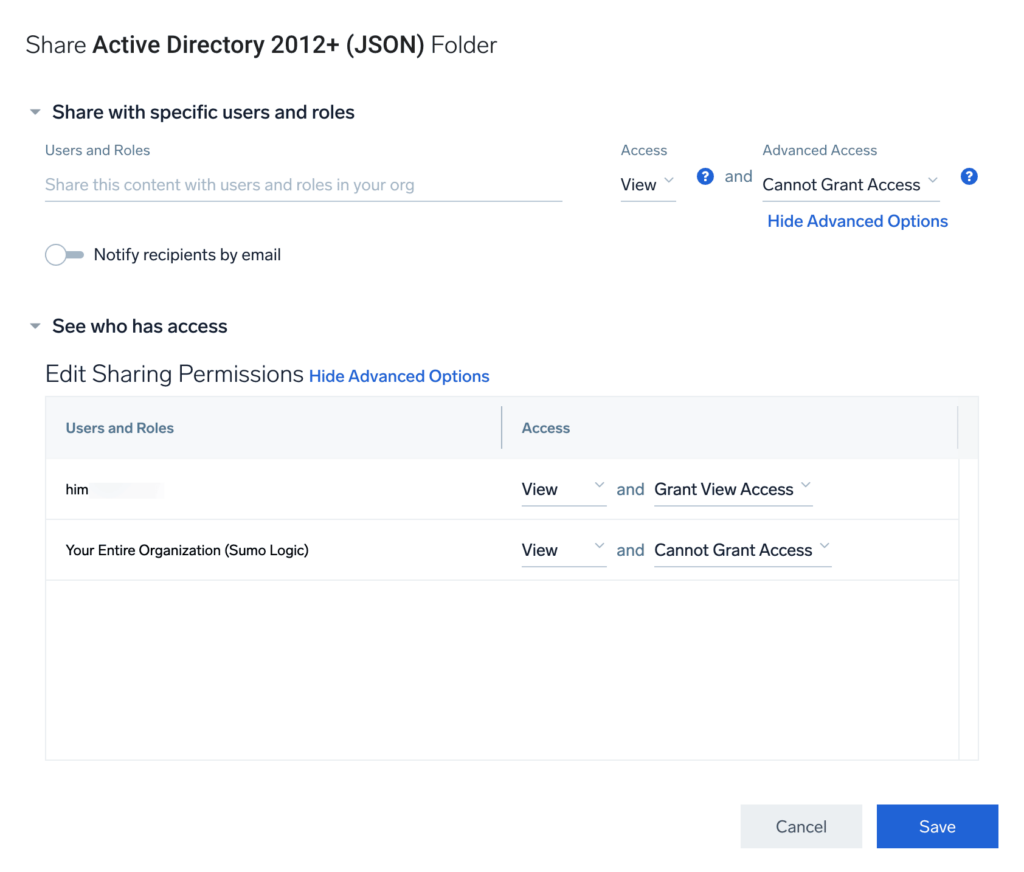
Content sharing for applications (Platform)
April 28, 2025
Administrators can now control the visibility of installed app content, enabling selective access based on user roles. This feature enhances security, reduces noise, and ensures that only relevant content is visible to the right users in organizations with diverse teams and varying access needs.
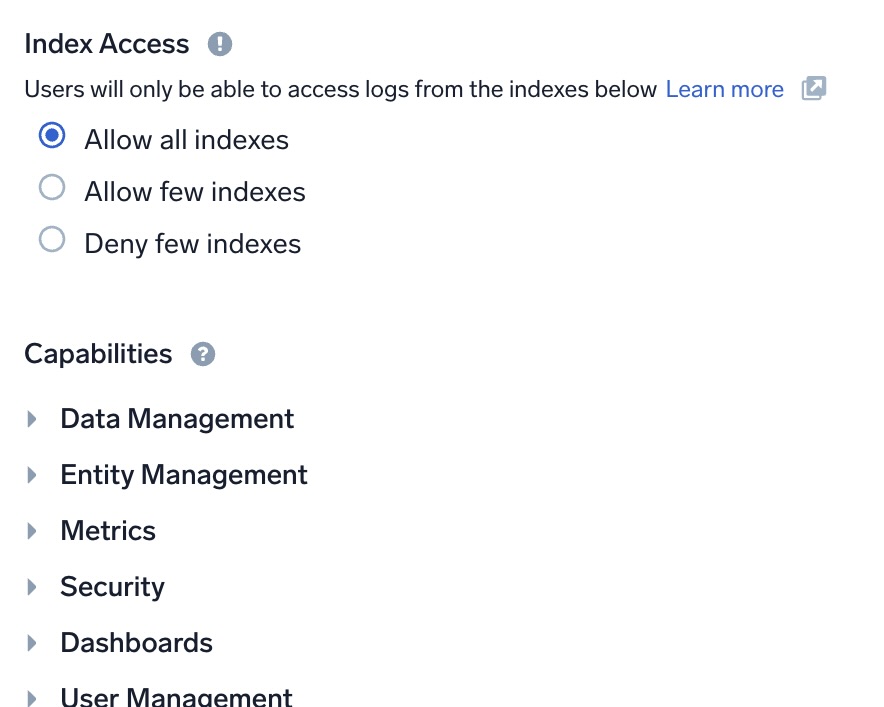
Role-based access control (RBAC) for indexes (Platform)
April 23, 2025
RBAC for indexes allows administrators to control access to data organized into indexes, enhancing both security and search performance. This update introduces role-based restrictions at both the index and field level, enabling efficient management of sensitive data access.
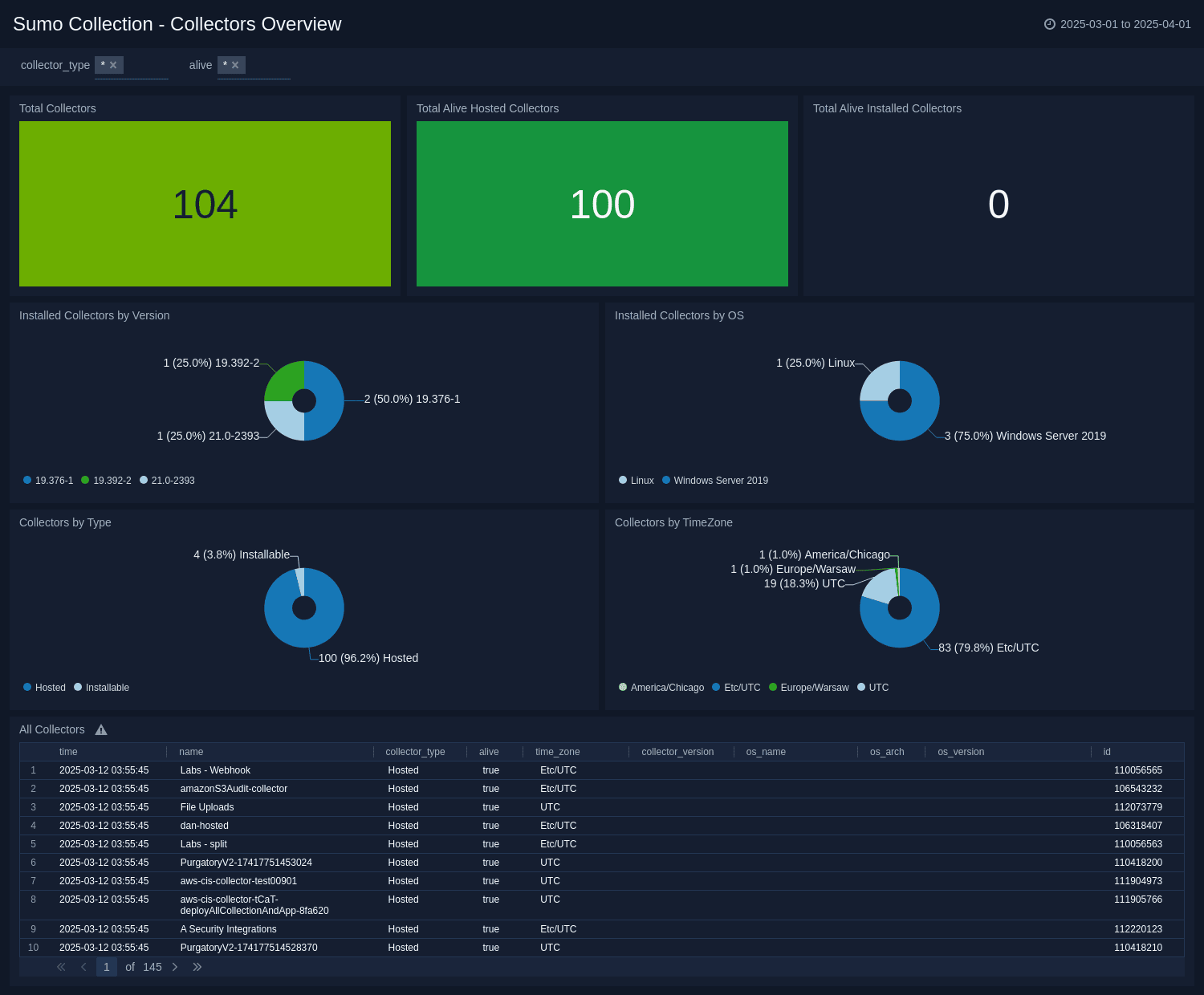
Sumo Collection app (Platform)
April 21, 2025
The new Sumo Collection app provides detailed insights into the health and status of Sumo Logic collectors and sources, enabling efficient management and monitoring. With intuitive analytics and visualizations, this app helps you optimize your data collection infrastructure and proactively identify issues.
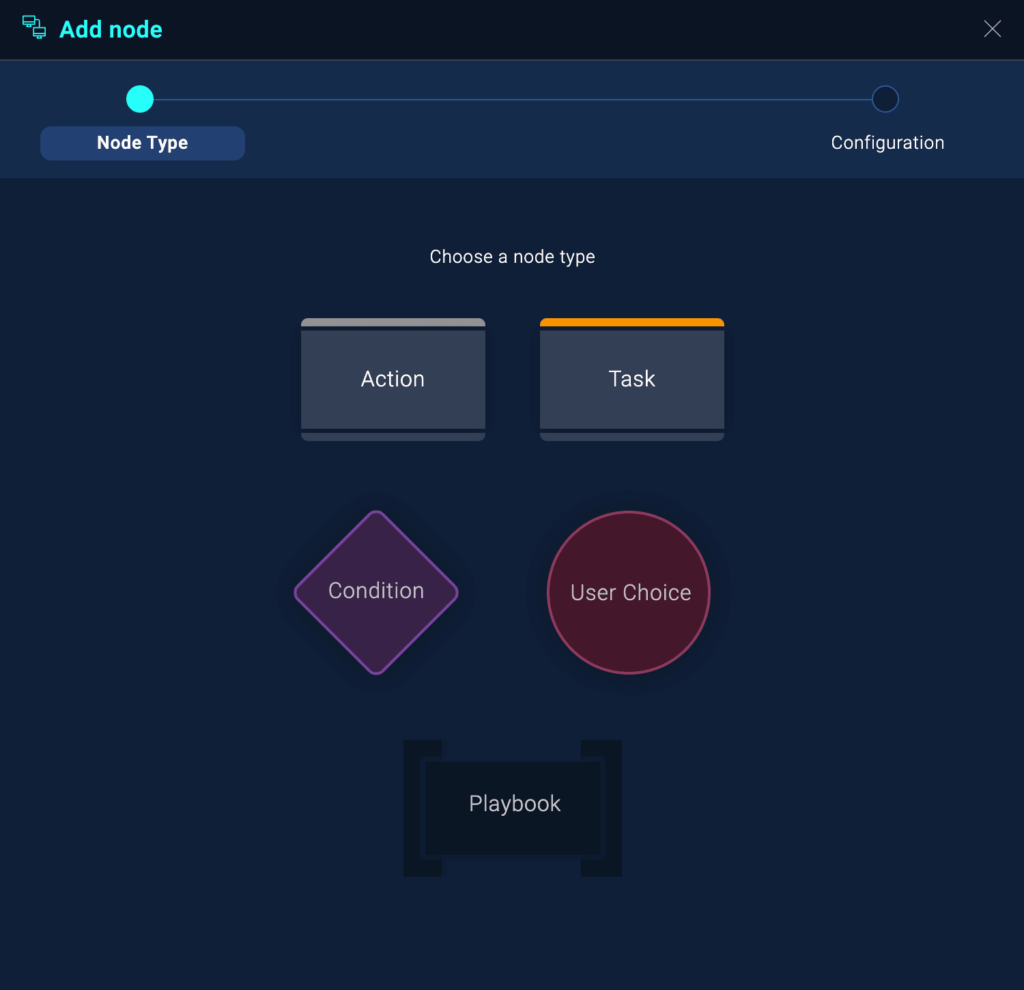
Playbook enhancements (Platform / SOAR)
April 21, 2025
Recent improvements to SOAR Playbooks enhance the user experience by preventing accidental overwrites and loss of changes. New features include dynamic field loading in node popups, confirmation dialogs for pre-existing drafts, alerts for unsaved changes, and audit logs for failed nodes during execution.
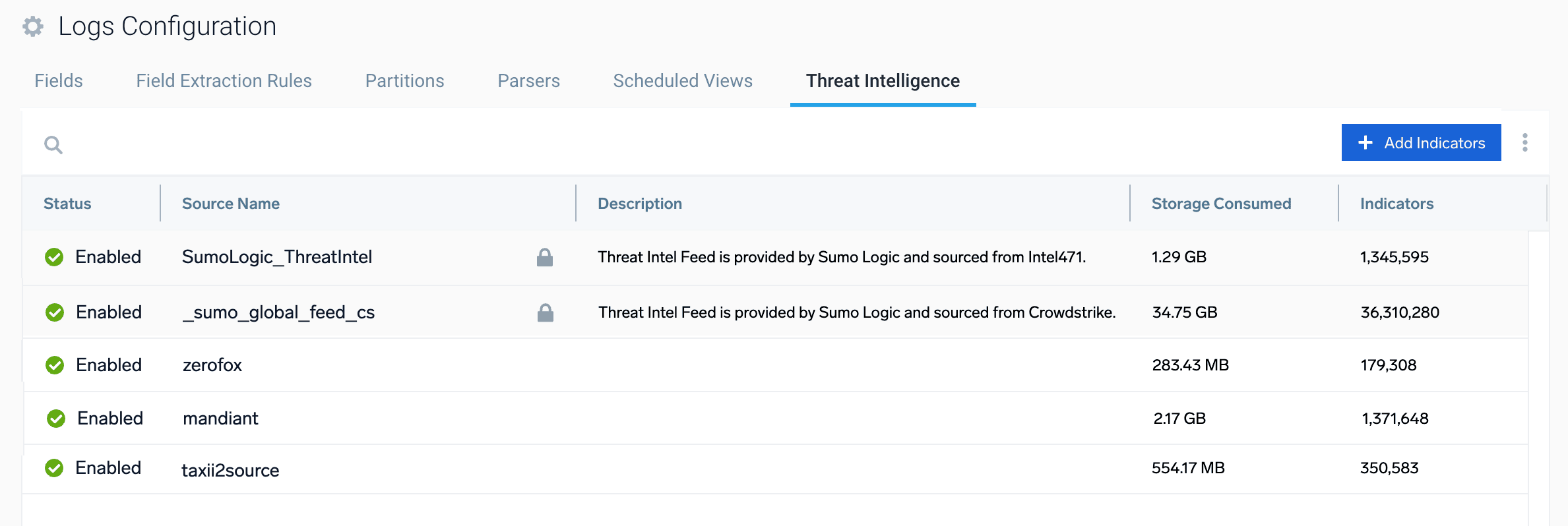
New threat intelligence source (SIEM)
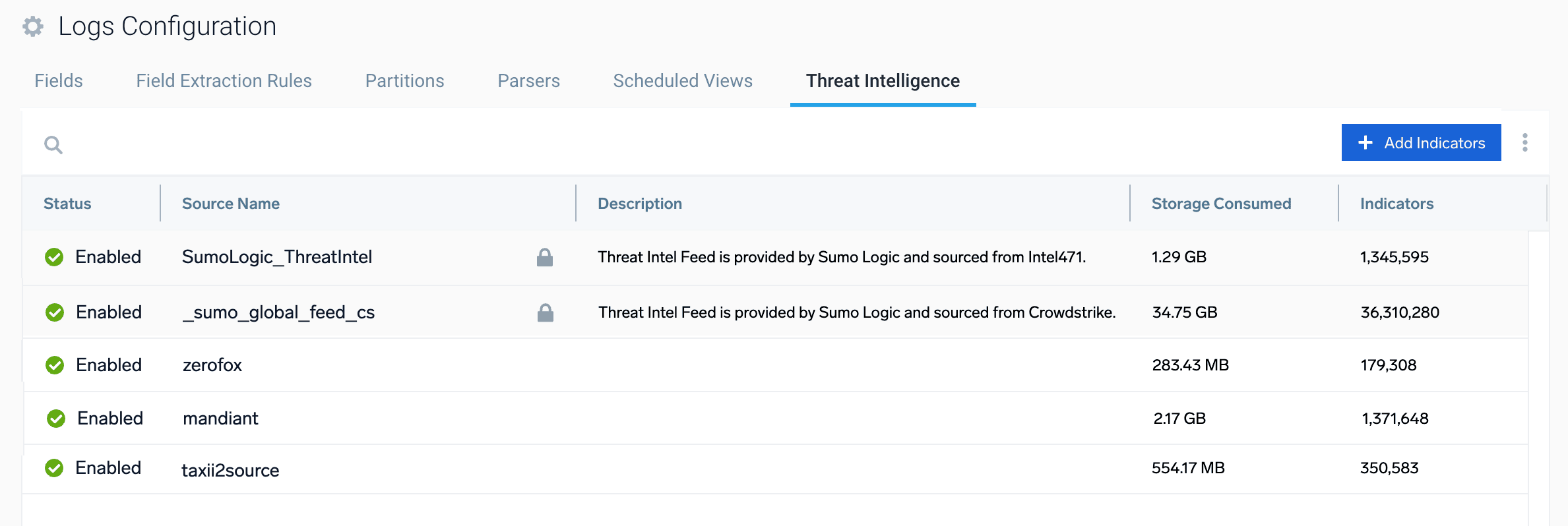
April 8, 2025
We’ve added a new default threat intelligence source, SumoLogic_ThreatIntel, which incorporates Indicators of Compromise (IoC) from Intel 471. This out-of-the-box source, alongside existing feeds from CrowdStrike, enhances security analysis with third-party threat indicators maintained by Sumo Logic.
March app and cloud-to-cloud highlights (Platform)
March 31, 2025
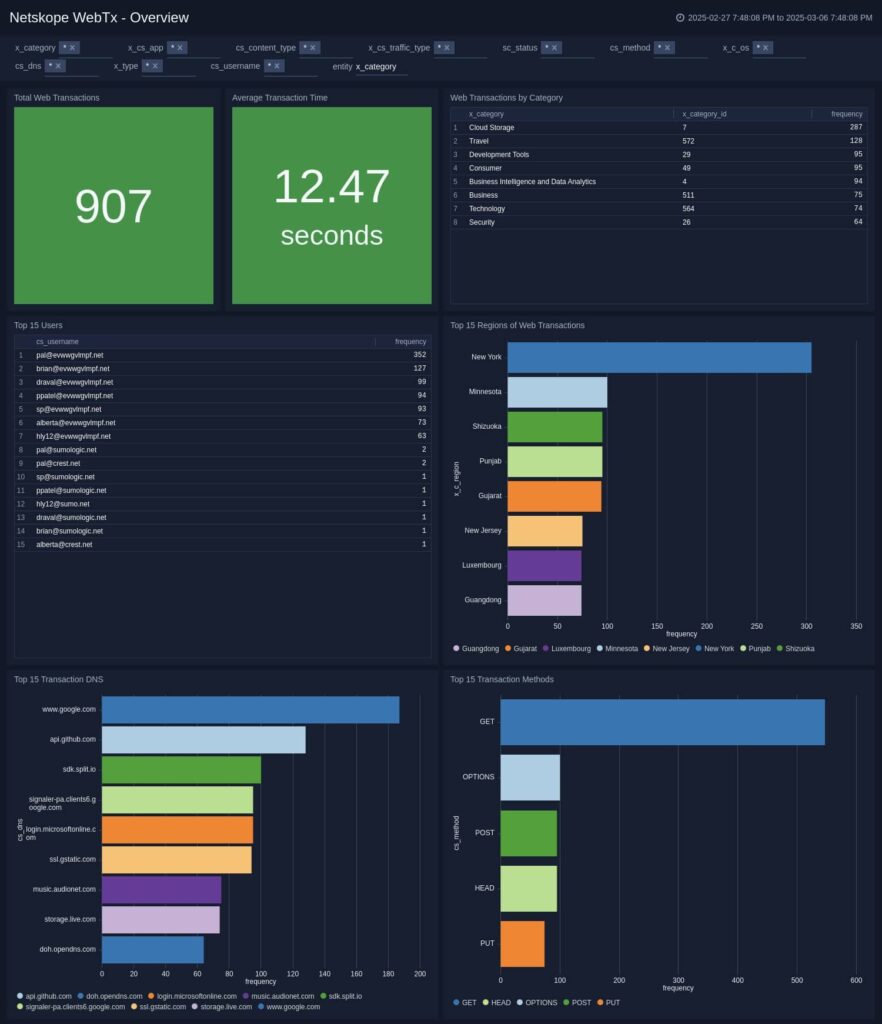
- Netskope WebTx: A new app leveraging the Sumo Logic Cloud-to-Cloud Netskope WebTx source to collect web transaction logs, offering visibility and insights into web traffic
- Confluent Cloud Metrics Source (C2C): A new cloud-to-cloud source for collecting metric data from the Confluent Cloud Metrics platform, enabling streamlined analysis in Sumo Logic
- Azure Security Advisor: A new app to help security analysts assess Azure Advisor’s recommendations and track remediation progress to improve Azure infrastructure security
- CyberArk Audit: A new app for monitoring and visualizing audit trails of user activities, security events, and anomalies to strengthen security posture
Threat intelligence (SIEM)
March 3, 2025
Threat intelligence lets Cloud SIEM administrators import Indicators of Compromise (IoCs) directly into Sumo Logic for enhanced security analysis. This feature lets you use the ‘hasThreatMatch’ function in Cloud SIEM rules to detect threats based on IoC data, helping you stay ahead of emerging threats.

February app and cloud-to-cloud highlights (Platform)
February 28, 2025
- JumpCloud Director: A new app providing visibility into authentication events and security actions within JumpCloud-managed environments, helping track failed logins, privileged access, and account lockouts in real-time
- Code42 Incydr: A new app for monitoring and detecting potential data threats, leveraging the Cloud-to-Cloud Code42 Incydr source to collect audit and file event data
- Trust Login: A new app that monitors authentication events and user activities using the Cloud-to-Cloud Trust Login source to respond to security threats
- Sysdig Secure Source (C2C): A new cloud-to-cloud source for collecting scan results from Sysdig Secure, enabling streamlined analysis of security data
- Dragos: A new app that helps security analysts minimize cybersecurity risks and safeguard critical infrastructure by collecting vulnerability and asset logs from Dragos
- Automox: A new app for collecting audit and event logs from Automox, providing security and IT teams with enhanced visibility into endpoint management
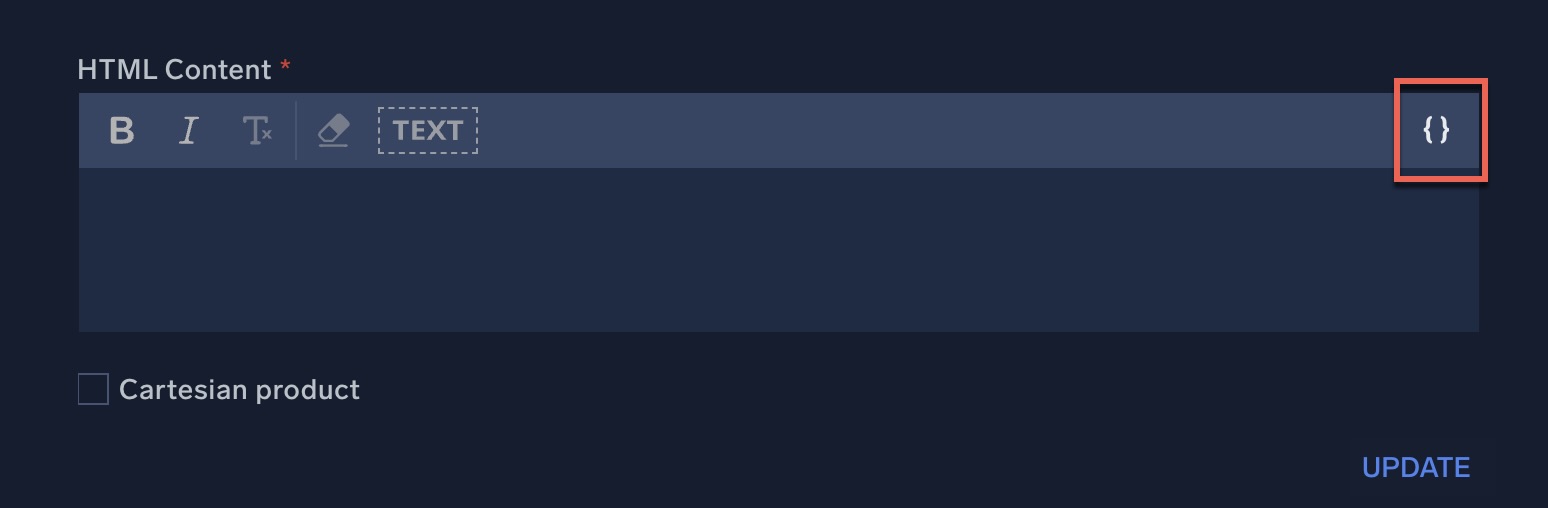
Dynamic array handling (Platform / SOAR)
February 24, 2025
The new dynamic array handling enhancement lets you loop through arrays directly within a text area field in action nodes. You can choose to iterate through the array or process it as a comma-separated list, improving efficiency in playbook automation.
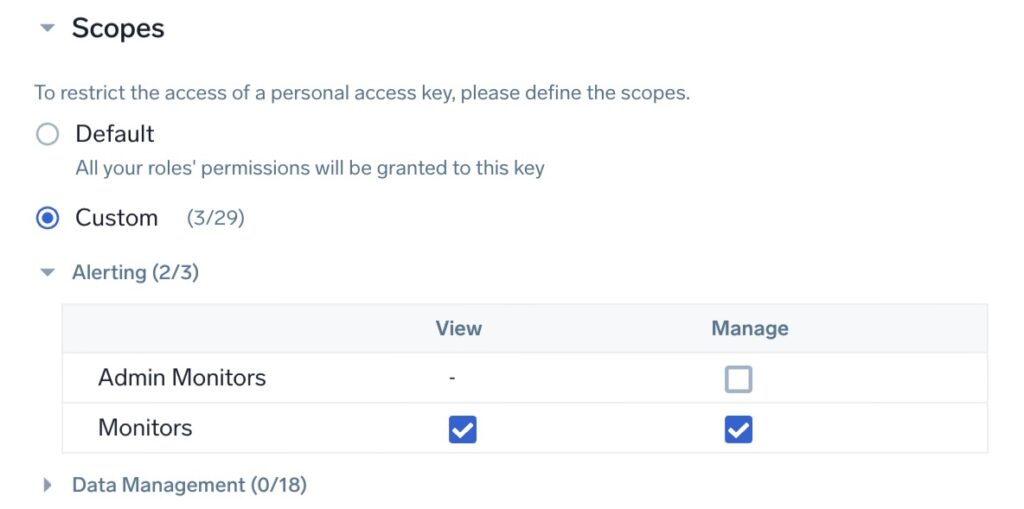
Access keys: Permission scoping (Platform)
January 16, 2025
Permission scoping for Access Keys lets you restrict access to only the necessary API endpoints, reducing security risks. This enhancement minimizes potential damage if an Access Key is compromised by applying the principle of least privilege.
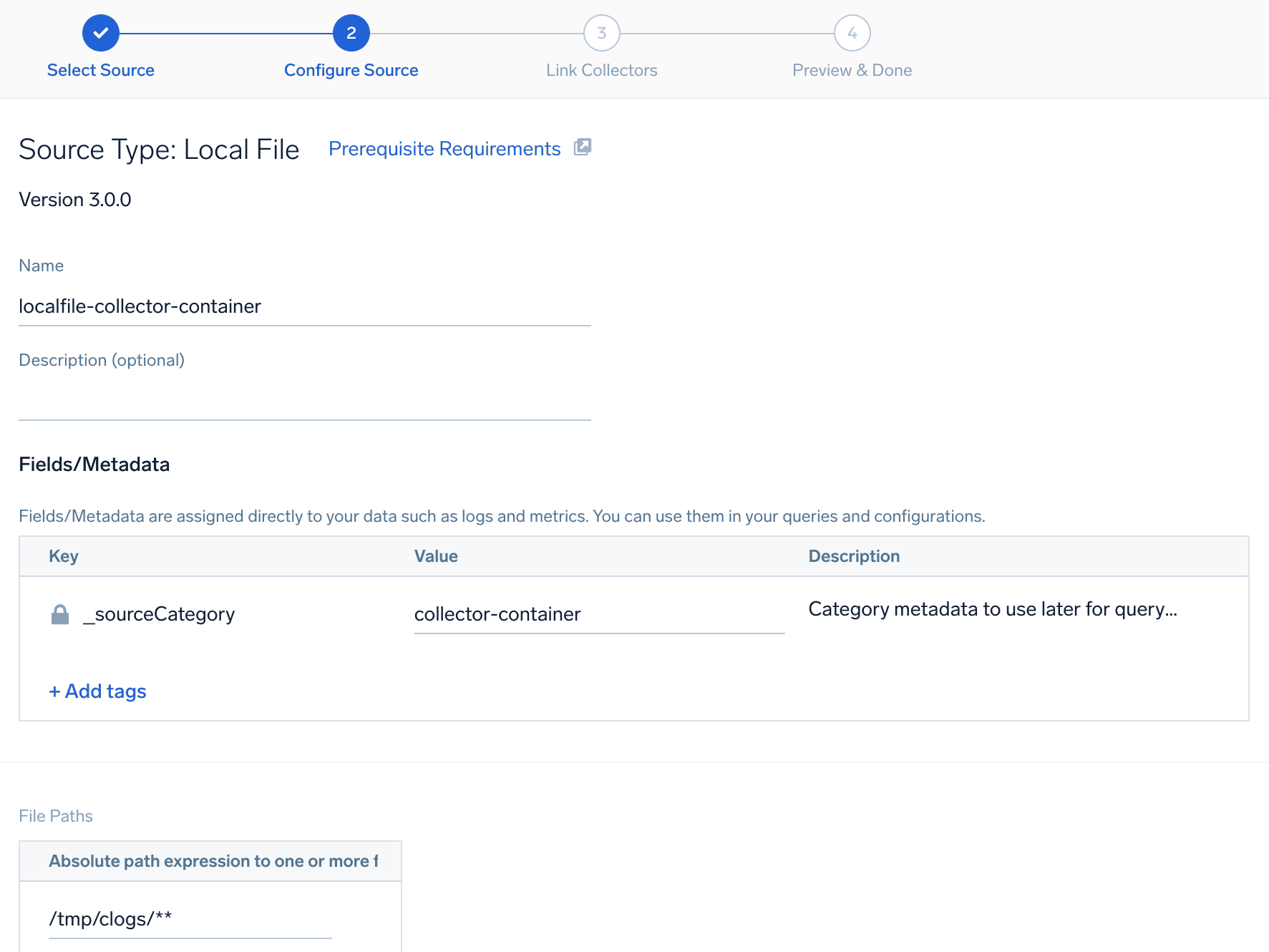
Remote Configuration now supported for Sumo Logic OTEL distribution
January 14, 2025
Sumo Logic OpenTelemetry distribution will now allow for remote management of data monitoring configurations. Customers will be able to configure data collection settings directly from the Sumo UI, eliminating the requirement for server access or manual modification of YAML files. New capabilities will make it easier to manage data monitoring across deployments by using Tags and defining what to monitor with Source Templates. These new feature improvements to Sumo Logic OTEL collectors will allow users to spend more time analyzing the data and less time configuring data collection.

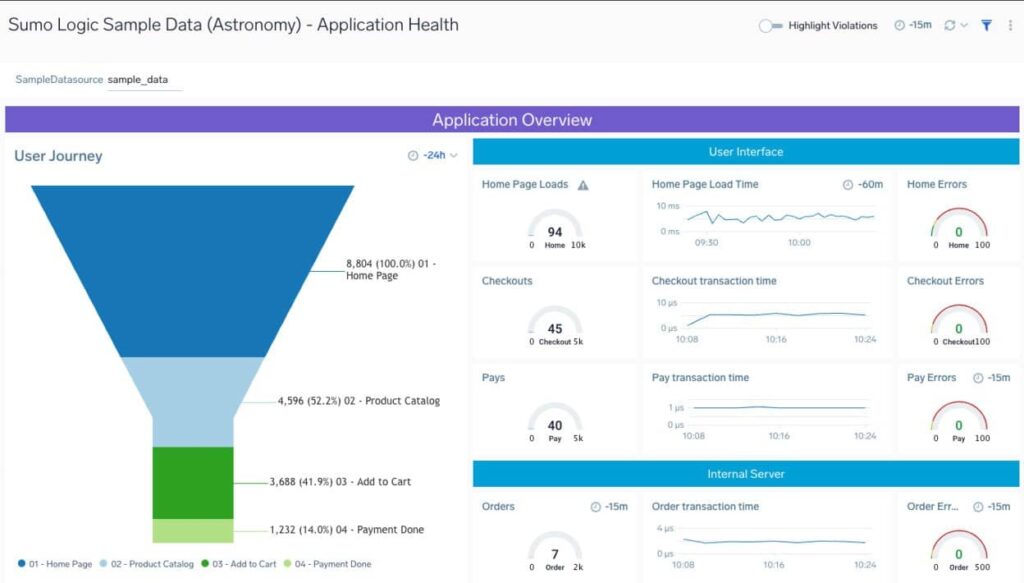
Kickstart data
December 12, 2024
Sumo Logic is enhancing the trial onboarding process with the introduction of pre-loaded sample data, allowing new users to immediately engage with the platform’s features without the initial need to provide their own data. This streamlined experience is designed to demonstrate the value of Sumo Logic quickly, as users can effortlessly explore interactive dashboards, carry out queries, and become familiar with the key functionalities right from the start. Trial users can access these sample dashboards through the Content library panel in the main side navigation of the classic UI, and they will be directed to them either via a modal or by finding them in the recently opened dashboards section. This addresses common onboarding hurdles such as data privacy concerns and technical intricacies of agent installation. This updated workflow not only removes early obstacles for new users but also fosters a deeper appreciation and understanding of Sumo Logic’s potential, paving the way for a smoother transition to actual data integration.
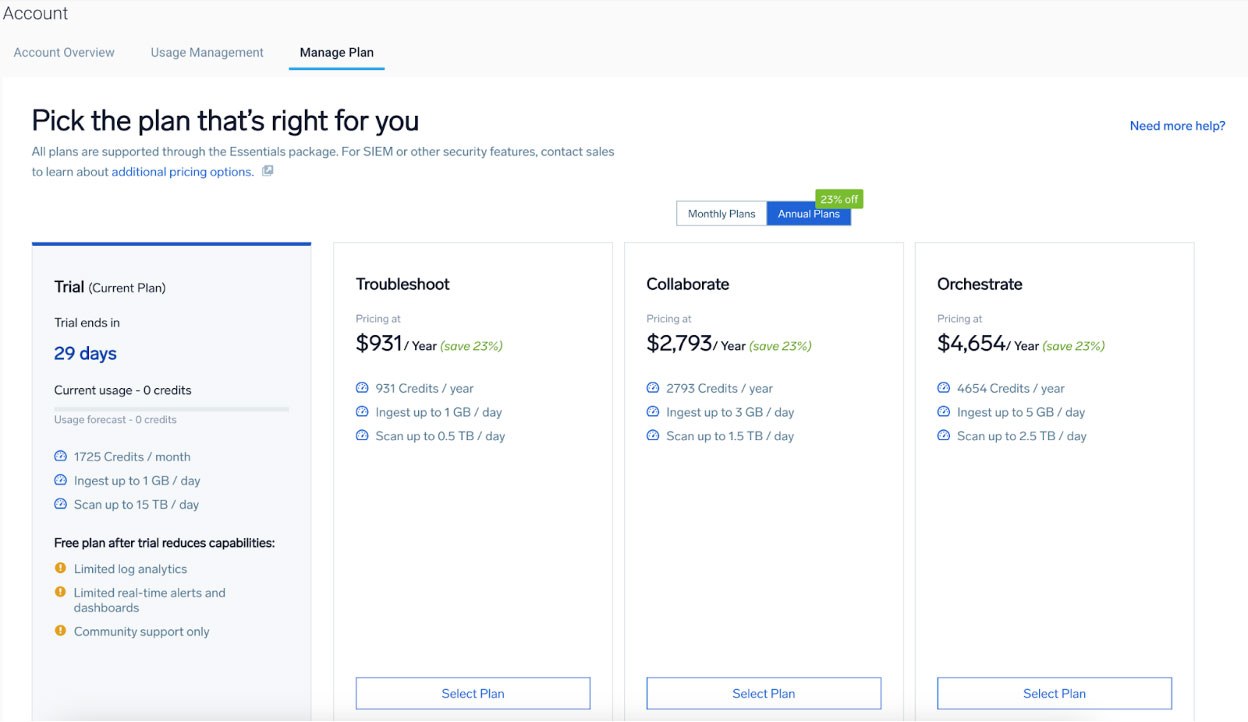
Self Serve checkout
December 12, 2024
Sumo Logic has launched a Self-Service Checkout feature which allows new signups and existing free trial users to autonomously select, and upgrade their pricing plans without the need for sales team assistance. This enhancement is part of our strategy aiming to provide an intuitive and accessible purchase experience. You can make quick adjustments to your plan in the Manage Plan section of your account page, using a secure credit card form powered by Zuora. Plans for future features include support for plan downgrades and various payment options, enabling greater flexibility and control over your use of Sumo Logic. With this new self-service model, Sumo Logic aims to improve customer satisfaction by simplifying the management of your service plan and expediting your path to obtaining value from the platform.
Universal Cloud Source
December 9, 2024
Universal Cloud sources will enable our customers to collect logs for products that provide APIs to collect data. Users can now create custom configurations using this new source by defining Authentication, Protocol, Data format and Pagination to complete setup. This new solution empowers our customers and partners to integrate with an ever growing list of products and monitor them in Sumo Logic.
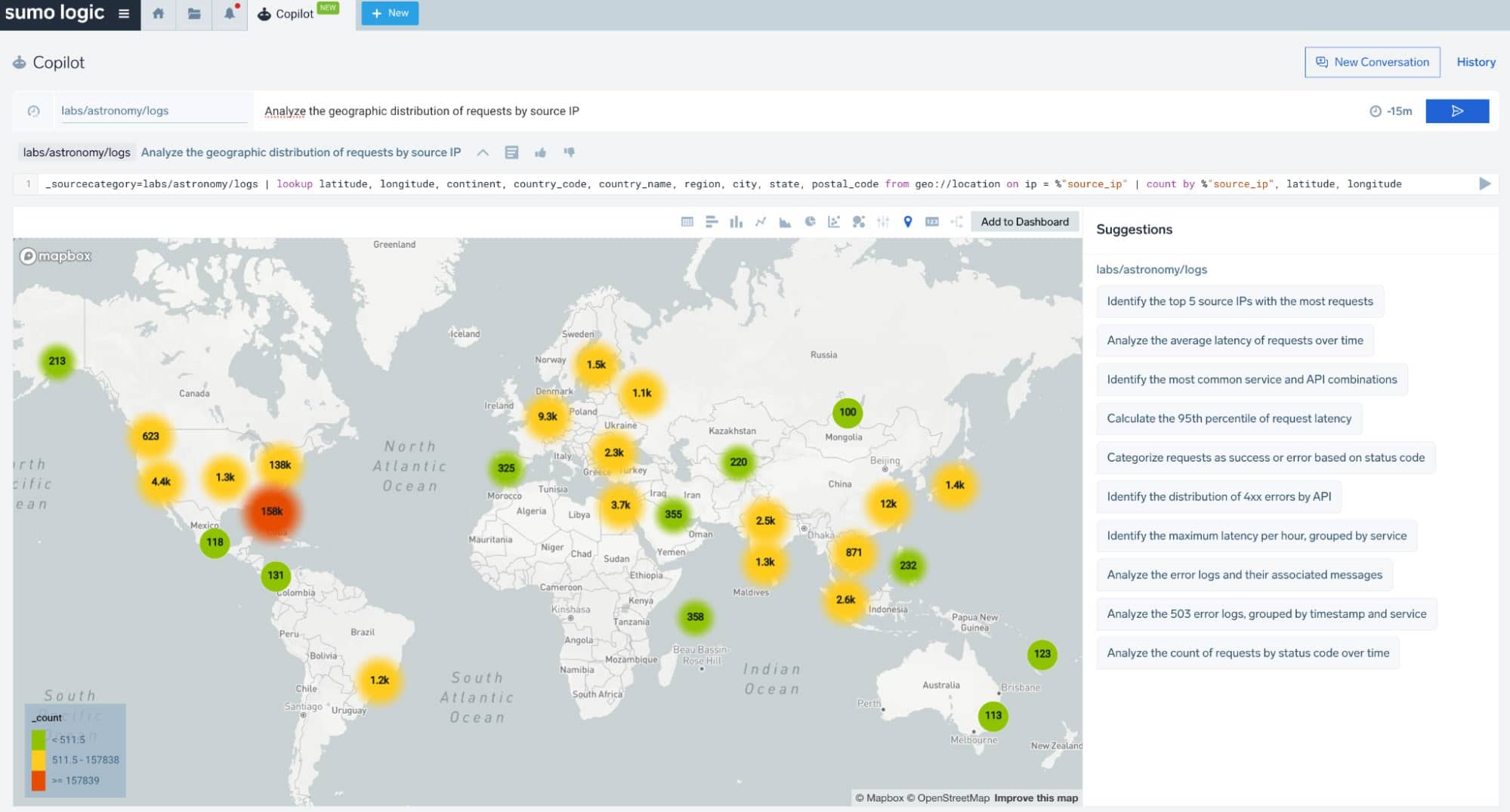
Sumo Logic Mo Copilot
December 2, 2024
Sumo Logic Mo Copilot is an AI-powered assistant that accelerates investigations and troubleshooting in logs by allowing you to ask questions in plain English and get contextual suggestions, helping security first responders and on-call engineers resolve incidents faster. Copilot features:
- Ability to ask questions in plain English to generate log insights.
- View suggestions relevant to your troubleshooting and investigations context.
- Save and resume troubleshooting or investigation sessions without losing context using Conversation History.
- Auto-visualize charts from search results, which you can add directly to dashboards.
- Auto-complete natural language queries to get to insights faster.
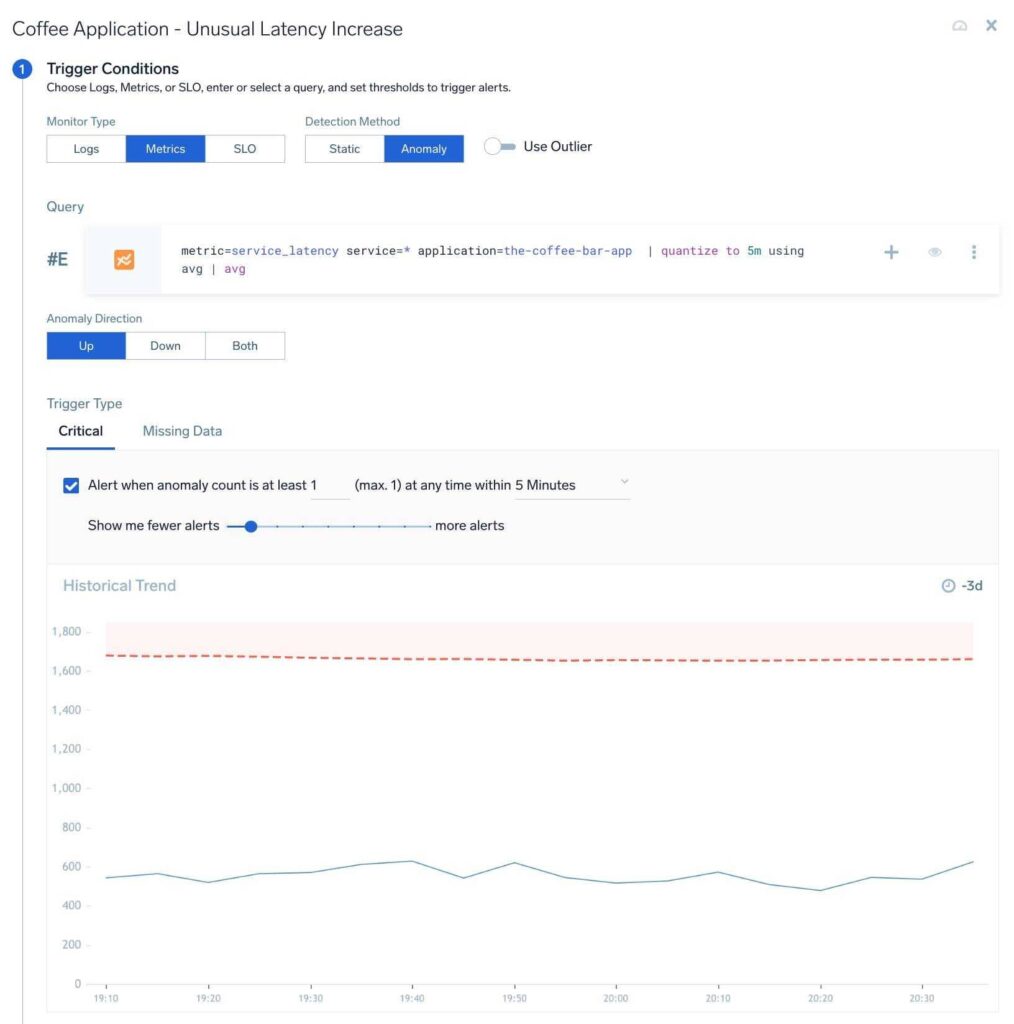
AI-Driven Metrics Monitors
November 7, 2024
AI-Driven Metrics Monitors, an extension of our previously announced AI-driven Logs Monitors capability are now generally available. 47% of customer monitors are based on metrics data. The noisiest 5% of these monitors trigger more than 10 times per day and consume about 6.5 hours of on-call attention each day.
With over 60% false positive alerts, such monitors are a distraction from feature development. With AI-driven Metrics Monitors, customers could reduce irrelevant alerts by 80% while acting on relevant alerts that signal deteriorated application availability or performance with automated recovery. Advanced anomaly detection on metrics data enables the noise reduction outcome while recovery is enabled by playbooks associated with a monitor.
AI-driven Metrics Monitors feature:
- Built-in ML model that uses 30d of metrics history to establish baseline behavior of the metrics signal and the underlying system
- Detecting seasonality in the underlying metrics signal including hourly or daily periodicity. This is important for eliminating noise from spikes that are expected from a periodic signal.
- Auto-tuned anomaly detection that minimizes user input to configure anomaly detection parameters for the least noise and most relevance.
Playbook capabilities are compatible with both logs and metrics-based monitors and help customers automatically enrich incident context, auto-diagnose root cause and automate recovery.
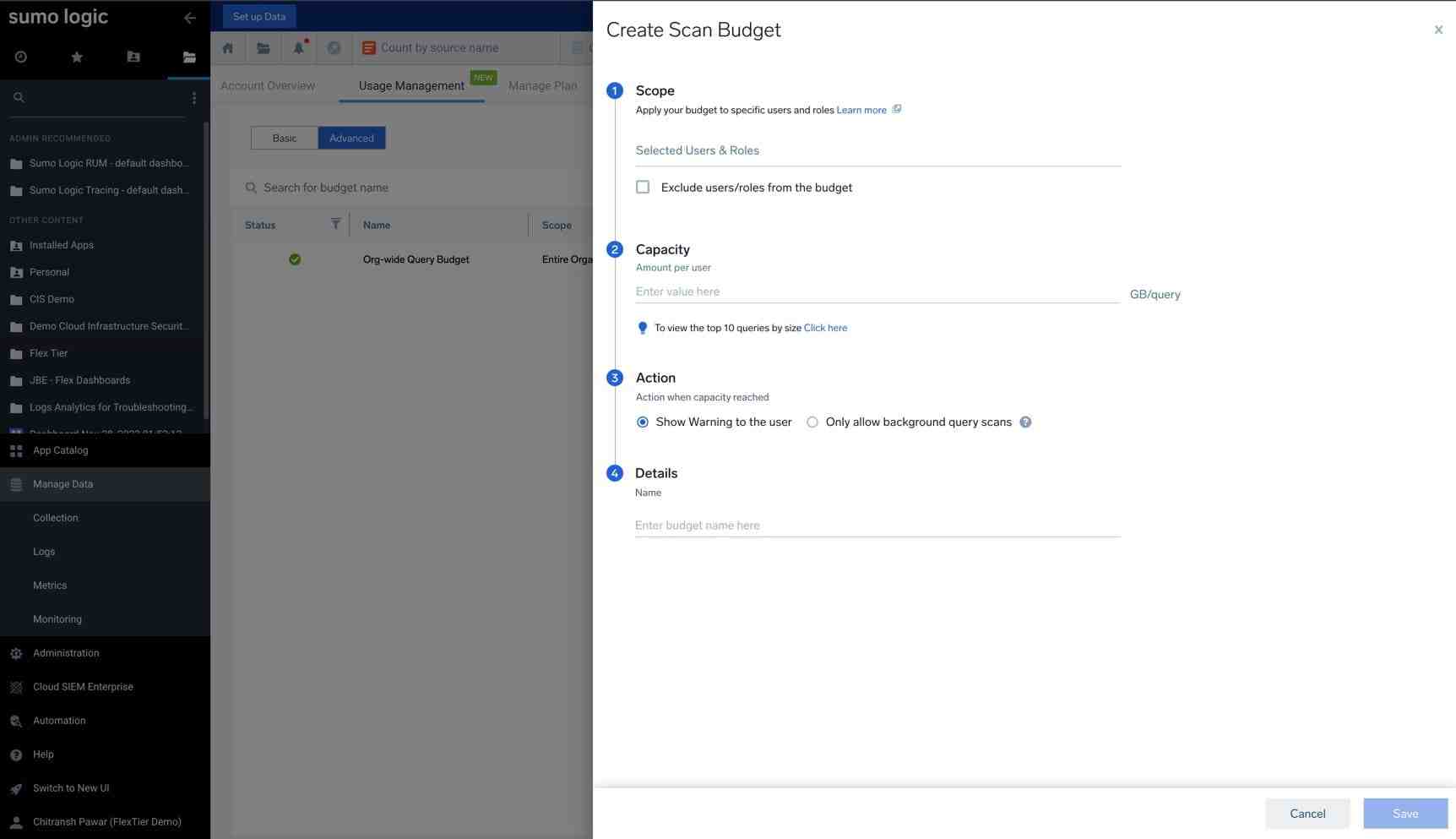
Usage Management – Scan Budgets
November 7, 2024
We are happy to introduce our new Scan Budgets functionality under the Usage Management tab in the Accounts section. This feature allows you to define search limits, helping prevent unexpected charges and manage Sumo Logic credits, particularly in pay-per-use scenarios by limiting search volume.
Key features include:
- Org-wide scan budget: Set a budget for search queries that applies to all users in the organization.
- User level and Role level scan budget: Set limits on search data volume at the user and role levels.
- Flexible actions: Choose what happens when the budget limit is reached. Options include “Display a warning to the user” or “Restrict Scans”.
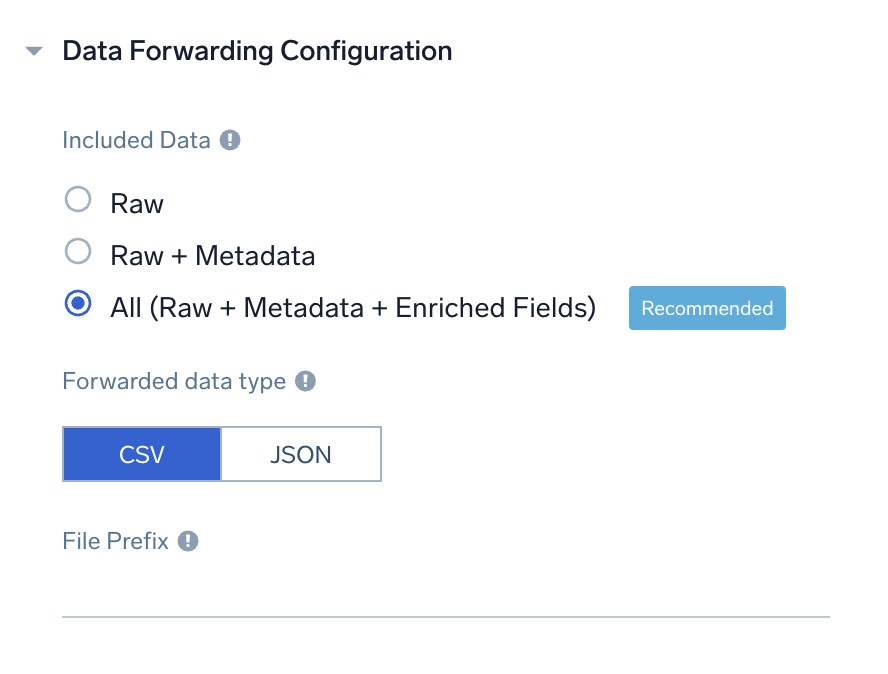
Enhanced data management and log handling
October 18, 2024
Over the past few months, we’ve rolled out several updates aimed at giving administrators and users greater control, precision, and flexibility in managing your data and logs:
- Customizable Log Data Forwarding: Gain flexibility in how your logs are stored by configuring the schema and format of log data sent to S3 destinations, ensuring your log exports meet your specific needs.
- Count Operator Enhancement: Count operator returns long values instead of int, allowing for more accurate calculations and support for significantly larger datasets.
- Advanced Filtering and Partition Management: Leverage advanced filters across FER, Fields, Partitions, Scheduled Views, and Data Forwarding, and seamlessly filter between User-Defined and System Partitions for faster, more intuitive navigation and management of your partitions.
These recent updates bring enhanced accuracy, streamlined management, and customizable log handling, empowering you to operate with greater efficiency and scalability.
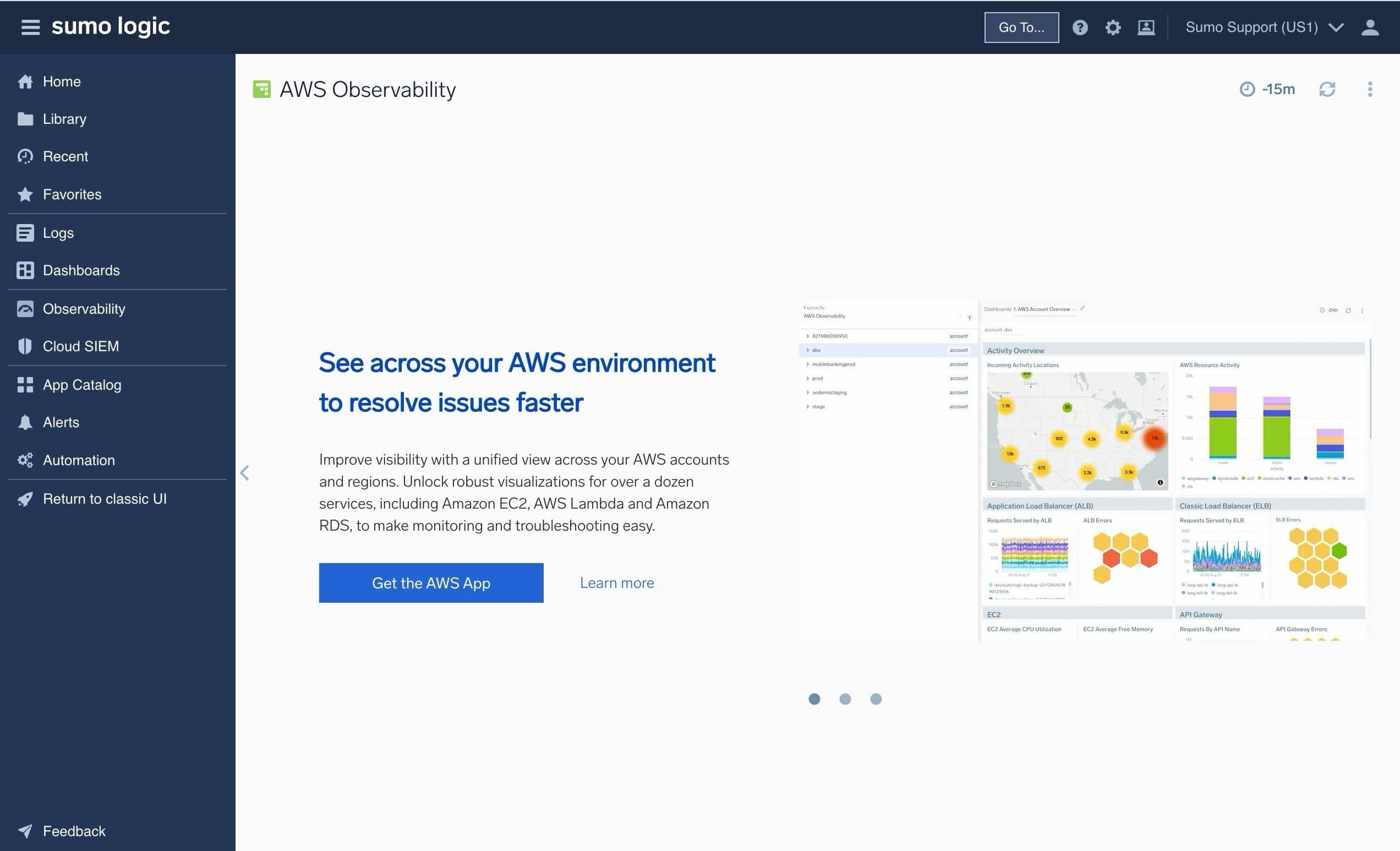
New Unified Navigation
September 30, 2024
We’re excited to announce the release of our new unified navigation, available today for you to explore. Our new navigation provides a fresh approach, bringing observability, Cloud SIEM, and Cloud SOAR offerings together under one unified navigation system making it easier for you to find, access and switch between the most commonly used features of the platform.
Along with the navigation we have moved to native browser tabs for managing your different open views within Sumo Logic, allowing you to take better advantage of the full features of your browser, and improving performance when loading or switching between different features of the platform.
You can try the new experience by selecting the “Switch to new UI” button found within the main navigation of the classic interface. If you wish to switch back, simply click “Return to Classic UI” from the new UI primary navigation.
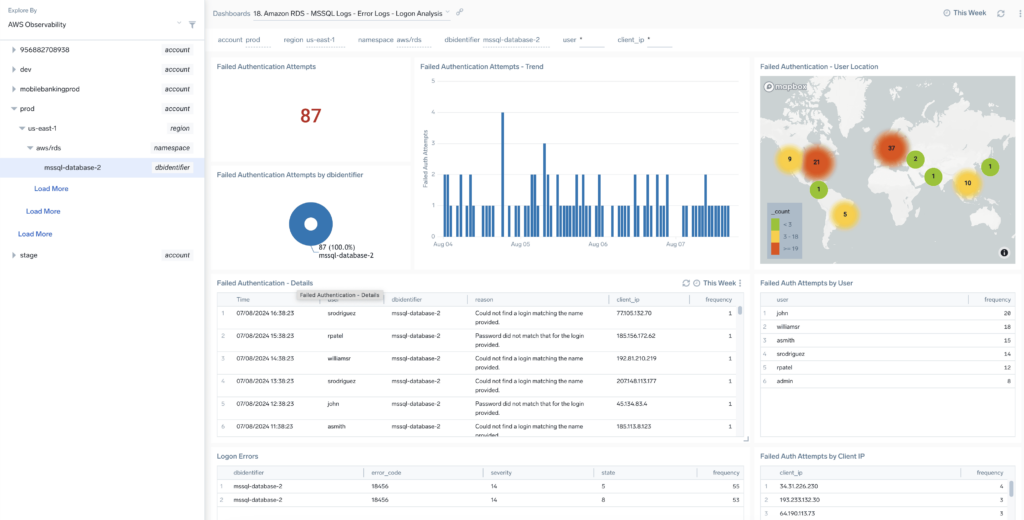
AWS Observability v2.9.0
August 7, 2024
We’re excited to unveil AWS Observability 2.9.0, now featuring support to analyze and monitor RDS MS SQL CloudWatch logs, with new monitors bringing the total to 70 out-of-the-box monitors. This release also includes automatic CloudFormation deployment telemetry to Sumo Logic (with an opt-out option) as well as brings reduced installation time via the CloudFormation template.
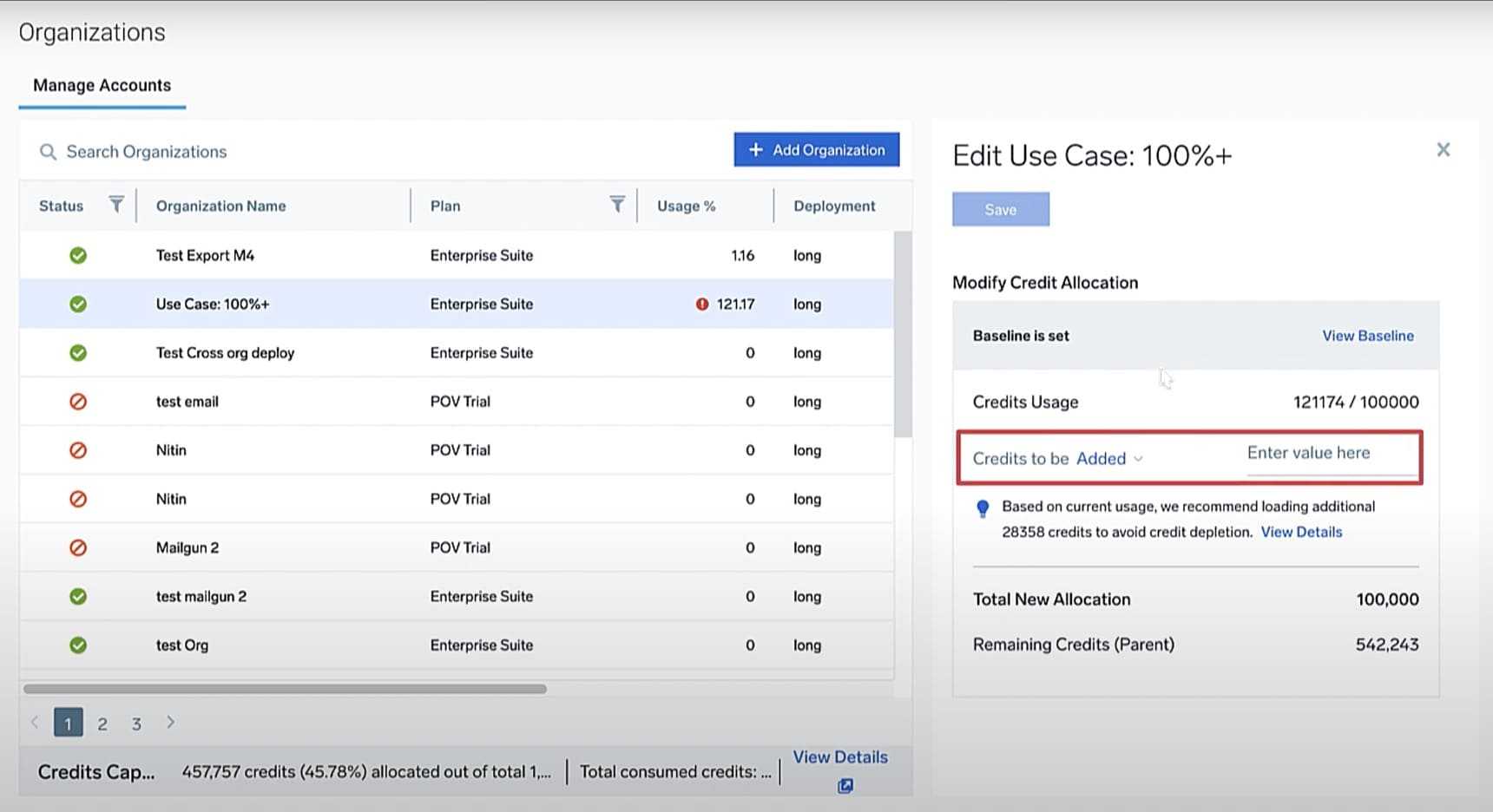
Sumo Orgs – New credits management experience
July 26, 2024
We are excited to introduce a new and enhanced credits management experience for our Sumo Logic orgs customers. This update empowers Sumo Logic parent org admins to manage child org credits with greater ease and control. Here are the key improvements in this update:
- Flexible allocation. Parent org admins can now allocate and manage credits for child orgs more flexibly, with faster and fewer steps.
- Smart recommendations. Receive system-suggested credit allocations tailored to your needs.
- Effortless top-ups. Seamlessly top-up credits for child orgs upon depletion without needing baseline adjustments.

Discover the new features in AWS Observability
July 10, 2024
We are thrilled to introduce AWS Observability 2.8, featuring new out-of-the-box dashboards for PostgreSQL based on Amazon RDS logs, a redesigned Amazon API Gateway with enhanced metrics and log-based dashboards for REST, HTTP, and WebSocket API types, over 20 new out-of-the-box monitors, and significant improvements in deployment time to streamline your monitoring experience on AWS.
Collect logs from Azure at Scale
March 28, 2024
Collecting data at scale is in Sumo Logic DNA and we are extending that to collecting data from Azure. Our integration with Azure Event hubs provides our customers a fully managed, scalable, and low latency solution to stream high volume logs from Azure to Sumo Logic. With this new source you can monitor high volume logs like endpoint , audit and load balancers with low latency and alert on findings in near real time.
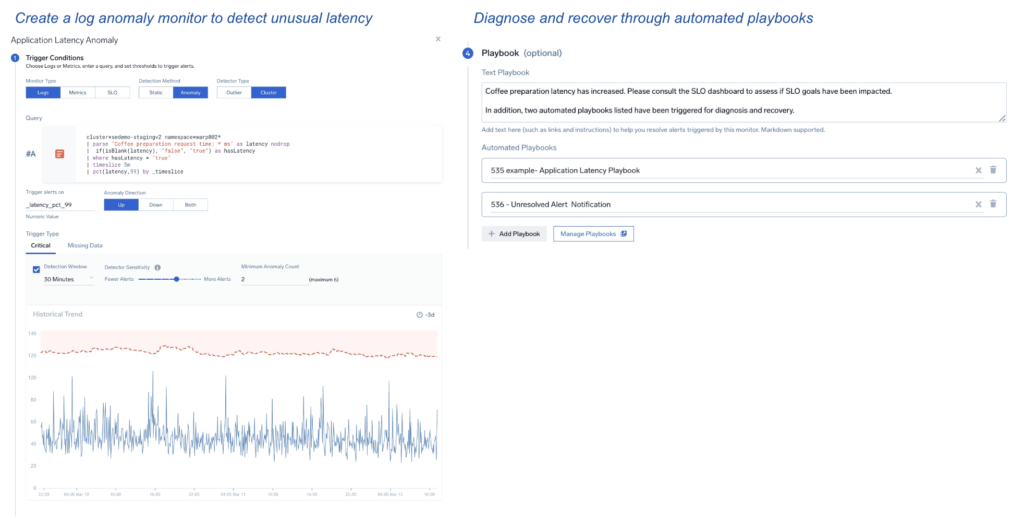
AI-driven alerts
March 12, 2024
We are excited to announce AI-driven alerts. This innovation combines patent-pending anomaly detection to monitor unusual application / security conditions in logs, alert a first responder and help them diagnose and recover quickly through automated playbooks.
Anomaly monitors help focus customer attention on real incidents and minimize distraction from false alarms. Playbooks powered by Sumo Logic Automation Service can be triggered by such alerts to accelerate incident diagnosis and recovery. AI-driven alerts also feature one-click set up to connect anomaly monitors to one or more playbooks. Moreover, first responders can view playbook execution within the Alert Response page itself.
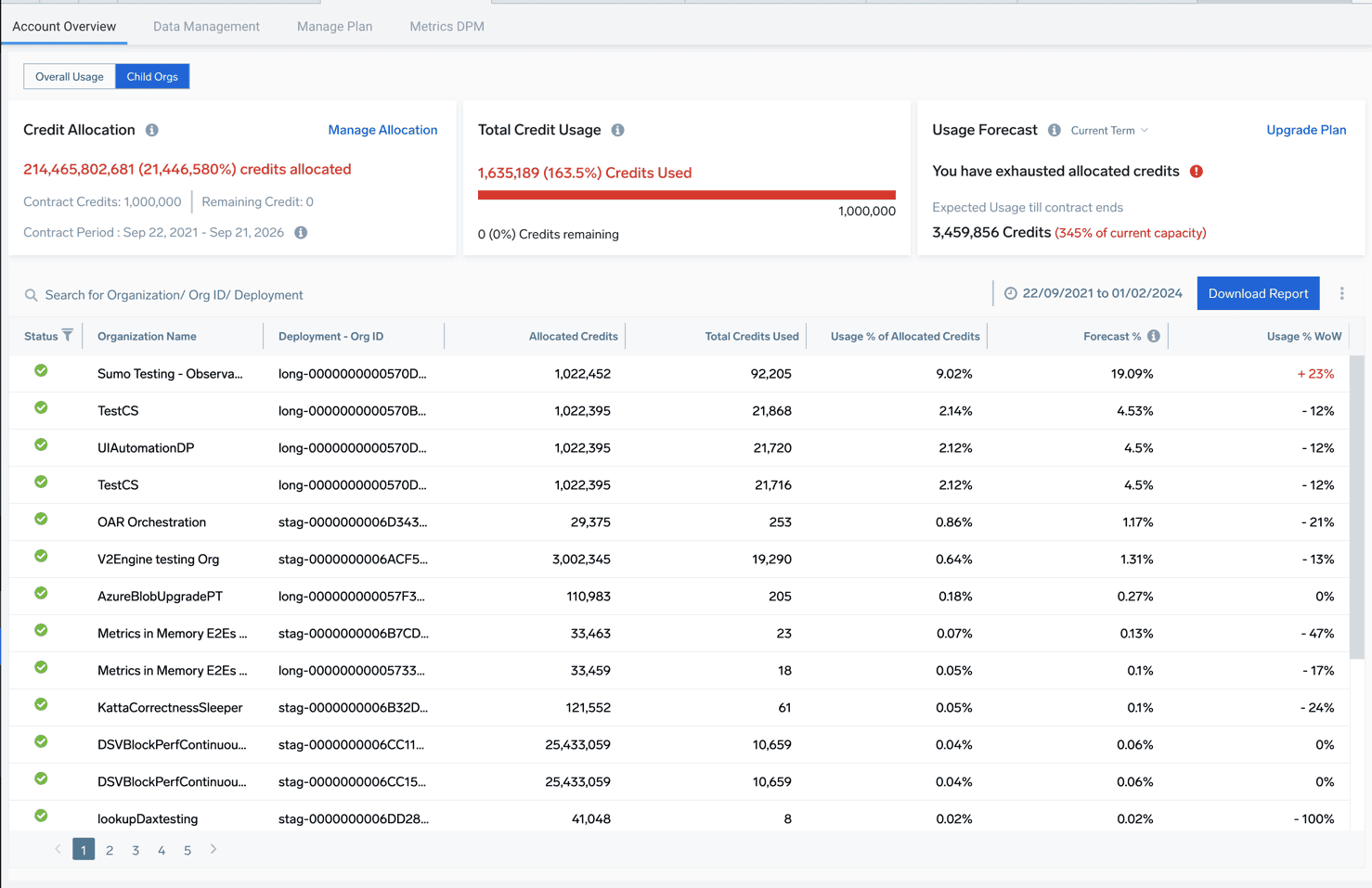
Sumo Orgs: New View for Child Orgs Usages
February 1, 2024
We’re excited to announce a powerful upgrade for Sumo Orgs customers: a centralized view of all child org usage within your accounts page! This update streamlines your experience and empowers you to manage your multi-org environment with greater efficiency. Now you can:
- Consolidated Insights: Gain a comprehensive overview of child org credit consumption and usage trends, all in one place.
- Dive deeper: Drill down effortlessly for granular insights into individual child orgs, identifying areas for optimization.
- Stay informed: Export detailed usage data for any timeframe, empowering informed decision-making.

Cloud Infrastructure Security for AWS
January 24, 2024
We are thrilled to announce the availability of Cloud Infrastructure Security for AWS, a Sumo Logic product offering that allows Cloud Operations, Security Engineers and developers to get a comprehensive view of threats, misconfigurations and suspicious activity in their AWS environment and take remedial steps through automated playbooks.
