Why risk it? Continuous compliance monitoring that you can trust
Demonstrate security best practices
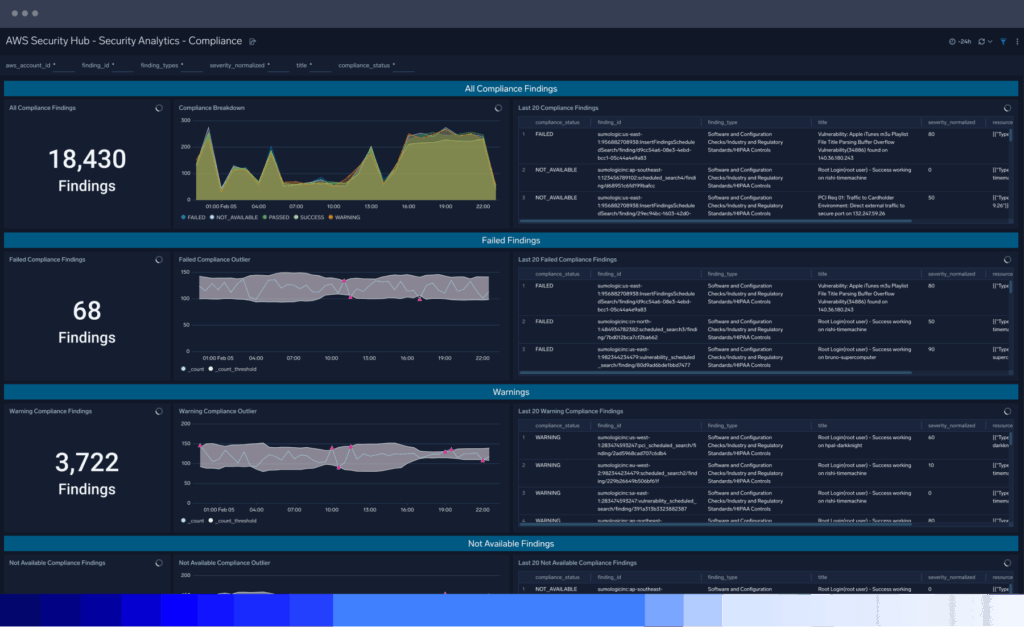
Streamline your risk management program with data monitoring and security and configuration analyses required for rapid, cost-effective continuous compliance readiness for security frameworks like HIPAA, NIST, CMMC or ISO 27001.
Manage compliance at cloud scale

Shorten audit cycles

Detect regulatory compliance risk

A trusted partner to support your continuous compliance readiness

Sumo Logic Platform
See how Sumo Logic can help demonstrate compliance in a snap

PCI DSS
Gain continuous monitoring and visibility of relevant PCI DSS requirements

Security data lake
Collect, store, search and analyze all your data with Sumo Logic

GDPR
Gain a central point for GDPR-related data collection and analysis

Audit and Compliance Guide
Shorten audit cycles and ensure ongoing compliance
FAQ
Still have questions?
The purpose of a security compliance audit is to assess and evaluate an organization’s adherence to specific security standards, regulations, or frameworks. Essentially, it answers the question, how are your current security controls meeting the security and privacy requirements of the protected assets?
In addition to assessing compliance, the cybersecurity audit helps identify potential security vulnerabilities, weaknesses, and risks, assesses the effectiveness of a company’s security controls and measures, verifies the existence and adequacy of security-related policies, procedures, and documentation, and ensures organizations meet legal and regulatory requirements of their industry.
In so doing, a cybersecurity compliance audit helps organizations improve their overall security posture and is evidence of an organization’s commitment to protecting its assets from potential threats and risks
Compliance risk management refers to identifying, assessing, and mitigating risks associated with non-compliance with laws, regulations, industry standards, and internal security policy within an organization. It is an ongoing process that requires commitment, resources, and a proactive approach to ensure that an organization operates in a compliant manner. And it involves establishing systematic approaches and controls to ensure that the organization operates within the boundaries of legal and regulatory requirements.
By effectively managing compliance risks, organizations can reduce legal and financial liabilities, protect their reputation, build trust with stakeholders, and create a more sustainable and ethical business environment.
An external audit by a compliance auditor (also known as an external auditor or compliance officer) will conduct an audit process to assess the internal policies of a company’s compliance program and determine if its fulfilling its compliance obligations.
Specific rules may vary depending on the audit framework or standard being used, but there are some general rules that apply universally.
Auditors must maintain independence and objectivity throughout the audit process, thoroughly document the process with a completed report, and adhere to a recognized compliance framework or standard, such as ISO 27001, NIST Cybersecurity Framework, PCI DSS, or industry-specific regulations.
The audit scope should be clearly defined, including the systems, processes and areas of the organization that will be assessed. Audits should take a risk-based approach, identifying and prioritizing higher-risk areas for detailed security assessment. Subsequently, they select a representative sample of systems, processes, or transactions for examination rather than auditing every item.
While the specific scope may vary depending on the industry, organization size, and regulatory requirements, here are some common areas that should be covered in a security compliance audit:
- Current security policies, procedures and guidelines and security incident history
- Access controls, including user access management, authentication mechanisms, password policies and segregation of duties.
- Network security controls, including firewalls, intrusion detection and prevention systems and network segmentation.
- Data protection measures, including encryption, data classification, data retention and data privacy controls.
- Incident response procedures and processes, including incident reporting and analysis.
- Physical security controls, such as access control systems, surveillance and security monitoring
- Security awareness and employee training programs
- Vendor management practices, including due diligence process, contractual obligations and ongoing monitoring of vendor security controls.
- Compliance with relevant industry-specific regulations, such as HIPAA, GDPR, PCI DSS, or SOX, depending on the industry and geographical location.
When it’s time for an audit, the Sumo Logic platform increases understanding, streamlines the auditing process and ensures ongoing compliance with various security regulations and frameworks in the following ways:
- Centralize data collection, capturing a wide range of organizational data from wherever it originates, empowering organizations to monitor and learn from it.
- Make various data types available with 100% visibility and visualize them in compelling, configurable dashboards for real-time monitoring and insights.
- Find any data at any time using query language to create filters and search parameters — whether it relates to regulatory compliance or internal security controls.
- Leverage machine learning analytics to improve and streamline audit processes and expedite compliance using tools like our PCI Dashboard.
- Cost-effective data storage that maintains attestations, such as SOC2 Type II, HIPAA, PCI Service Level 1 Provider, and a FedRAMP moderate authorized offering.
- Real-time monitoring of incoming data and security controls to identify anomalies that could signal a security risk, cyber threats, vulnerability, security threat or non-compliance.
Numerous data integrations and out-of-the-box applications that properly collect and catalog all data.


