If you hear that a product is 92% effective, you’d assume it’s operating as intended. It seems like a success story. But dig a little deeper, and the picture changes; only 51% say that their security information and event management (SIEM) is very effective. What does it mean when a majority of security relies on a tool that works, but doesn’t work well enough? Not broken, not exceptional. It’s somewhere in between.
Somewhere between logs flowing in, alerts firing, and compliance boxes being checked, there’s a gap between the tool functioning properly and successfully identifying threats early on.
This friction is reflected in how security leaders discuss their tools. According to Sumo Logic’s 2026 Security Operations Insights report, while the majority of respondents rated their SIEM as effective, fewer expressed confidence in it. The gap between ‘it works’ and ‘it works well enough’ is the focus of this discussion.
The dangerous position of the effective zone
SIEM was designed to ingest logs, match events against predefined rules, generate alerts, and fulfill compliance requirements. While most SIEMs are doing exactly what they were built to do, the underlying design is decades old. Built before cloud-native architectures, before identity became the primary attack surface, and before AI-powered threats outpaced signature-based detection.
The real risk is the gradual accumulation of blind spots that go unaddressed because the system technically works, and the urgency to change it never materializes. The friction shows up in four predictable patterns.
- Reactive detection: The SIEM is designed to identify threats that you already know how to recognize. Threats that don’t match existing signatures go undetected; not because the tool failed, but because it was never built to catch what it hasn’t encountered before.
- Growing alert volume without intelligent triage: The SIEM generates alerts as part of its functionality, but the lack of intelligent prioritization leads to overwhelming alert queues, which creates noise and slows down response time.
- Manual context building: Correlating events across different data sources, constructing timelines, and surfacing relevant context often requires manual effort, resulting in inefficiencies in most environments.
- Operational burden: Excessive time tuning correlation rules, managing parsers, onboarding new log sources, and updating content as the threat landscape shifts. Most of the team’s time is spent keeping the SIEM up-to-date instead of focusing on proactive security measures such as threat hunting, improving detection, or building a stronger security posture.
These factors combined create a problem: practitioners experience daily friction without escalating it, and leadership doesn’t see enough signal to prioritize change. As the environment grows increasingly complex, the gap continues to widen.
Why teams stay in the effective zone
93% of enterprise organizations use at least three security operations tools, and 45% use six or more. More than half, 55%, already say they have too many point solutions. Every tool was purchased to address a specific gap, yet together they create another issue: siloed data, disconnected workflows, and alert noise that complicates the ability to understand what’s happening across the environment. A fragmented security stack makes even a capable SIEM work with incomplete information.
Additionally, most organizations review and consolidate their security vendors only twice a year, with a quarter doing it annually. In a landscape where AI capabilities, cloud-native architectures, and attacker tactics are all evolving rapidly, reviewing your stack once a year means relying on outdated practices.
And security teams are becoming leaner at exactly the moment environments grow more complex. Only 48% of security leaders believe their current tooling supports a streamlined team structure. In that context, the bandwidth required to evaluate and migrate to a new platform feels like a cost nobody can currently afford, even when remaining is the greater long-run cost.
What high performers do differently
The data points to two compounding problems for teams stuck in the effective zone, and high performers have taken steps to address both.
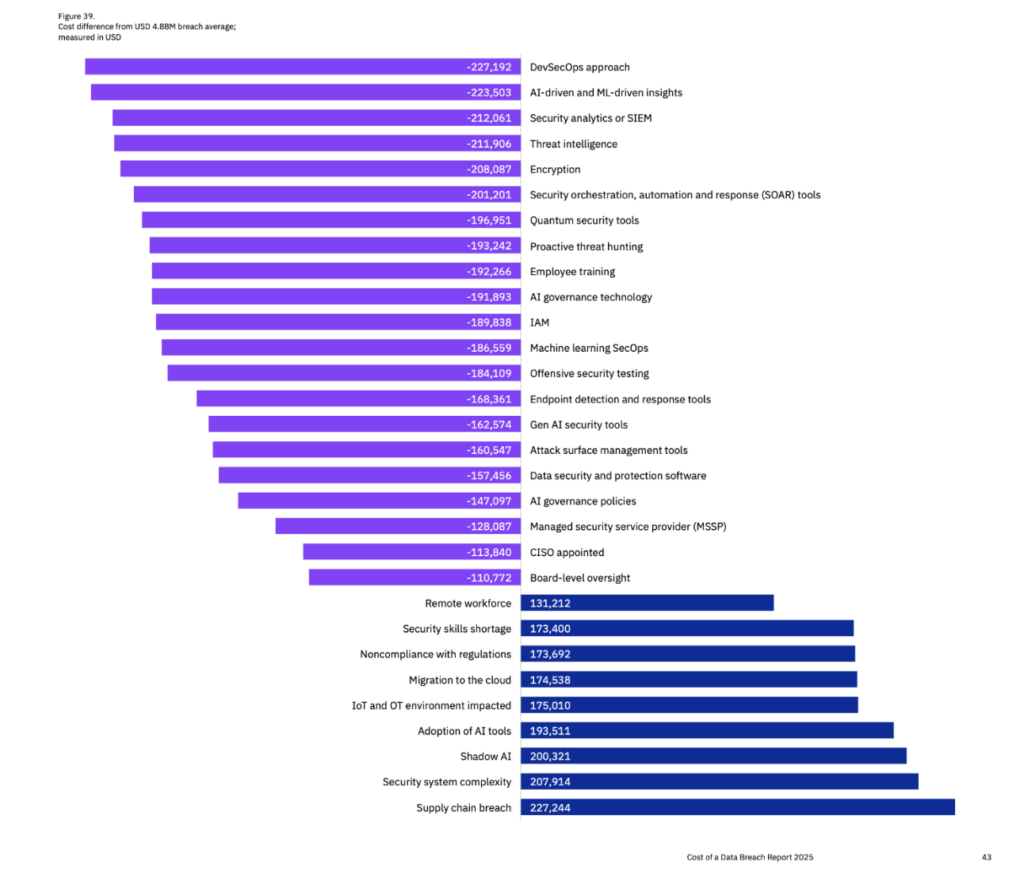
First is the SIEM architecture itself. Only 37% of security leaders have a cloud-native SIEM with integrated AI features, unified telemetry, and scalability. The majority are still using hybrid or legacy systems designed for a different era, before the data volumes, application complexity, and attack surface of modern cloud environments existed. These systems may not be visibly failing, but they weren’t built for the realities that security teams face today.
The gap between the intended function and current requirements is not a configuration issue; it’s a structural one. And it has a direct consequence for AI: when the underlying data is fragmented, incomplete, or inconsistently normalized across sources, AI can’t perform reliably. The detection logic is only as trustworthy as the telemetry feeding it.
Second, alignment between SecOps and DevOps teams plays a huge role in overall performance. Organizations that collaborate between these areas – shared tools, workflows, and context – tend to outperform on all satisfaction metrics. In fact, among well-aligned teams, 82% report their SIEM is very effective.
It’s also crucial that SecOps and DevOps work from the same data foundation, and whether that foundation is built for the environment you are running today, in order to go from effective to exceptional SIEM.
From effective to exceptional
Transitioning from effective to exceptional doesn’t require adding more security tools. More point solutions create more noise, more integration work, and more budget pressure without delivering better coverage or faster response.
The data suggests consolidation into a unified platform. 87% of security leaders agree that unified security and monitoring tools would improve team efficiency, and 100% see value in a unified approach to logs, metrics, and traces for both SecOps and DevOps teams. This demonstrates a consensus that the existing fragmented security model is unsustainable.
But a unified platform is only half the equation. An AI-ready SIEM requires more than AI-integrated features; it requires trustworthy data underneath them. With trustworthy data, AI can move beyond pattern-matching on known threats. It can surface anomalies earlier, reduce the effort required to build investigation context, and operate with the reliability that reduces analyst burden rather than adding to it. It’s the difference between AI as a feature and AI as a force multiplier.
The teams moving to exceptional aren’t waiting for the urgency to arrive on its own. They are recognizing that 51% confidence in the tool at the center of their security operations is a risk, not a foundation. And they’re asking the harder question: is their SIEM built for the environment they’re actually meant to protect?
For most teams, the honest answer is: not quite. But that gap is closable.
See what an AI-ready SOC platform looks like. Request a demo.