Cybersecurity is more challenging for businesses now than ever before. The average global cost of a data breach exceeds $4M per year. AI has changed the game for attackers: 97% of organizations have reported an AI-related security incident, and that’s only the beginning. As security teams work to keep pace, the environments they’re defending continue to get more complex, more distributed, and harder to see in full.
This guide covers what modern security teams need to know about a modern SIEM: how it works, why it matters, its benefits, and best practices to continue to optimize your SIEM.
Why do enterprises need a SIEM?
The term SIEM was coined by Gartner analysts in 2005. Two decades later, SIEM technology is more critical than ever. Organizations today operate across a fundamentally different environment than they did even five years ago.
Security challenges have not gone away; they’ve gotten more difficult. Cloud adoption, third-party integrations, and the explosion of microservices have made the traditional perimeter disappear, as there is no longer a clear boundary to defend. At the same time, the number of identities inside an organization has increased. Machine identities, service accounts, and automated workflows now outnumber humans and are harder to track.
In addition, AI has given attackers new capabilities: automated reconnaissance, phishing at scale, and defenses that adapt faster than security teams can. As environments grow more complex, the log volume grows with them, and the signal-to-noise ratio gets worse, not better. The result: an expanded attack surface that generates more data than a security team can realistically handle.
SIEMs help solve this problem. They analyze enormous amounts of data across an environment simultaneously, detect threats, and provide a workspace for investigation and response. Without one, security teams are left manually combing through individual log files, which is a slow, error-prone process that makes cross-source correlation nearly impossible. SIEM earns its value by correlating that data to surface the full picture; turning noise into context and context into action.
What is SIEM?
Security information and event management (SIEM) products help organizations stay ahead of the never-ending stream of security threats. It gives teams a centralized system to collect, normalize, and analyze disparate data, enabling them to spot and respond to threats quickly. It helps reduce risk through early detection and quick response.
The core features of a SIEM system include:
- Centralized collection and normalization of data: Disparate data is aggregated from multiple sources (firewalls, endpoint detection and response tools, servers, identity providers, cloud, etc.) across an organization’s IT infrastructure. The data is raw, unstructured, and inconsistent.
- Data normalization and parsing: The raw log data from different vendors is broken down into specific fields and mapped into a uniform naming convention (i.e. standardized schema) for future cross-platform analysis.
- Data enrichment and contextualization: Adds additional information to the normalized data, such as the geolocation of an IP address, identity info, etc., to help turn a signal into context.
- Log management: The storage and organization into a central repository that ensures data is stored securely and remains searchable for a specific time period for real-time monitoring, faster analysis, and compliance.
- Event correlation: Joins data from seemingly unrelated log sources into a single, unified security incident.
- Threat detection: The process of identifying malicious activity through signature-based rules for known threats, anomaly-based detection for outliers, and machine learning for sophisticated patterns that static rules miss.
- User, entity, and behavior analytics (UEBA): An analytical layer that uses machine learning to profile normal behavior of users and entities to detect deviations from the baseline.
- Alerting: The notification engine that automatically triggers when security events match pre-defined rules, thresholds, or anomalies. Using AI, alerts are assigned a severity level to help analysts focus on high priority threats.
- Unified case management: The workflow interface where security incidents are tracked, documented, and managed from start to finish. It allows multiple analysts or automated playbooks to work on the same incident without duplicating efforts.
- Incident response: Where the organization works to contain, eradicate, and recover from a threat. It can be automated with human oversight or done via set playbooks.
- Reporting and dashboards: Visual and analytical tools used to monitor, analyze, and report on security data. Dashboards provide real-time, out-of-the-box or customizable visuals while reports are detailed, scheduled, or ad hoc documents that summarize data for compliance, auditing, and management review.
- Compliance (PCI DSS, HIPAA, and more): Automatically collects, centralizes, and manages log data to meet regulatory requirements.
- Integrations: Through APIs and webhooks, it’s the connection between a SIEM and the rest of the security stack like threat intelligence, firewalls, EDR, identity providers, cloud platforms, etc. AI agents rely on these integrations to take action, such as telling a firewall to block a specific IP address.
Traditional vs. next-gen vs. modern SIEM
Traditional SIEMs were originally built for log aggregation and compliance, but so much has changed since they were first introduced. Legacy SIEMs run on-premises, rely on signature-based rules, and focus mainly on collecting logs and manual-intensive investigation. They are difficult to scale and costly to manage and maintain. All of which results in high alert fatigue, high operational costs, limited visibility, and slow investigations, allowing attackers to dwell in systems for weeks or months.
Next-generation SIEMs brought a big shift by moving to the cloud. Using software-as-a-service (SaaS) and big data lakes, they solved the scaling issues and added machine learning (ML) capabilities for behavioral analytics (UEBA). Instead of only relying on signature-based (if-then rules), they built dynamic baselines of normal behavior for every user and device, surfacing anomalies not seen before. UEBA reduced alert fatigue by filtering out benign anomalies, allowing actual high-risk incidents to be identified. In addition, searching became faster, and data collection was easier, but analysts still had to do a lot of manual work.
While next-gen SIEMs gave the cloud-native scale to see everything and analytics to reduce alert fatigue, modern SIEMs provide the intelligence to understand it all in context. Defined by the convergence between security and observability, it unifies security telemetry with application performance and infrastructure health to help security teams move from reactive to proactive.
With AI tools like machine learning, large language models (LLMs), and AI agents, it learns from large amounts of data, guides investigations through natural language search, and automates responses with agentic AI.
Because of visibility across the entire technology stack, AI agents now reason through complex alerts (e.g., correlating a security event with a simultaneous performance spike), provide natural-language summaries of attacks, and execute responses instantly. By eliminating the manual aspect of triage, modern SIEMs empower analysts to shift their focus to proactive threat hunting, detection engineering, and improving the organization’s overall security strategy.
Legacy vs next-gen vs modern SIEMs
| Feature | Legacy SIEM | Next-gen SIEM | Modern SIEM |
| Architecture | On-premises, appliance-based | Cloud-native, SaaS, built for on-premises, cloud, multi-cloud, or hybrid | AI-native with built-in agents across the platform. |
| Data ingestion | Limited to network and log sources; struggled with cloud ingestion. Parses and indexes data upon ingestion. | High velocity from virtually any source, Stores raw data and parses on query. | Same breadth as Next-Gen, extended to AI pipelines, LLM apps, and full-stack observability telemetry |
| Investigation | Manual-intensive | Near real-time, faster search | Automated, natural language processing (NLP) guides and summarizes investigations in natural language |
| Detection | Manual, rigid rules-based | Machine learning (ML), user entity and behavior analytics (UEBA), dynamic behavioral baselines | Multi-agent system that generates and tests hypotheses across correlated data sets |
| Response | Manual investigation | Automated playbooks and integrations | AI agents execute responses autonomously with human oversight built into the workflow |
| Threat hunting | Not supported; fully reactive | Limited; analyst-driven with manual queries | Proactive; AI automates routine detection so analysts shift focus to active threat hunting and detection engineering |
| Scaling | Difficult, requires new hardware | Elastic scaling | Elastic scaling optimized for AI workload and high-volume telemetry from unified security and observability data |
| Speed | Delayed, batched processing | High-speed real-time search | AI triages and prioritizes alerts in real-time; humans focus on high-severity incidents |
| Observability coverage | Security telemetry only; siloed from IT and app teams | Security telemetry only; limited cross-team visibility | Unified security and application performance and infrastructure health; breaks down silos between SecOps, ITOps, and DevOps |
| Integrations | Manual, complex configuration of local agents and hardware, usually managed by in-house development | API-driven; automated maintenance | Deep bidirectional integrations across stacks; AI agents act through integrations (i.e. instruct firewall to block and IP) |
| Management | Requires internal IT to handle installation, upgrades, and security | Shifts management to the provider, allowing automatic updates | Shifts focus to outcomes; mean-time-to-detect (MTTD) and mean-time-to-respond (MTTR) |
Modern SIEM benefits
Modern SIEMs do more than just help teams automatically detect and respond to threats quickly. They redefine the operational model of the SOC by turning a data lake into an action engine. Key benefits include:
- Unified security and observability: By centralizing telemetry from cloud platforms, on-premises infrastructure, and application health, teams gain a single view of the entire environment. This convergence breaks down silos between SecOps, ITOps, and DevOps for a coordinated, full-stack response to incidents.
- Contextual intelligence at scale: Machine learning, UEBA, and AI-driven correlation surface sophisticated threats that rules-based systems miss by identifying anomalies across disparate datasets.
- Monitoring for AI-specific threats: Log-based visibility across AI pipelines and LLM applications that legacy tools were never designed to see.
- Proactive threat hunting: By automating routine detection and investigation, analysts are able to move beyond reactive response by actively searching for hidden threats.
- Doing more with less: Security teams can operate at scale by automating routine tasks, allowing analysts to focus on complex incidents and strategic security improvements.
Accelerated time-to-value: A cloud-native platform enables rapid deployment. With out-of-the box integrations, pre-built detection rules, and ready-made compliance reporting, modern SIEMs deliver immediate value.
SIEM vs. SOAR and other security tools
SIEM is the foundational tool for managing data and threats, but it’s not the only tool organizations rely on, especially for incident response.
SIEM vs. SOAR
While a SIEM excels at ingesting large volumes of data from disparate sources and identifying threats through correlation and analytics, SOAR’s core purpose is to automate the response process once a threat has been surfaced. Over time, this distinction has blurred, as SIEMs began to natively support automated playbooks, response orchestration, and case management. Now the same is happening with AI.
SIEM vs. AI SOC
An AI SOC represents the next evolution in security operations. It’s how modern security teams operationalize AI across detection, investigation, and response. It’s an evolution in how the SOC functions.
A new category of vendors has emerged claiming to deliver an AI SOC as a standalone solution that promises autonomous threat detection and response. But the underlying limitation is significant: these platforms are only as good as the data they can see. AI agents don’t generate their own ground truth; they reason from the data they’re given. Without comprehensive, normalized, cross-environment telemetry, they’re drawing conclusions from an incomplete picture, leading to missed threats, false positives, and automated responses that make the wrong call at exactly the wrong moment. And speed without accuracy is a liability.
Modern SIEMs are what make an AI SOC trustworthy. They provide the centralized data ingestion, correlation, and detection capabilities that AI agents need to take meaningful, accurate action. Without the visibility that SIEMs provide, an AI SOC will just make wrong decisions quickly.
The future
Just as SOAR became part of modern SIEMs, AI SOCs are following the same path. Leading SIEM platforms are developing AI agents that automate investigative workflows, generate natural-language summaries, and take autonomous response actions with human oversight.
Over time, the distinction between SIEM and AI SOC will disappear, much like the line between SIEM and SOAR did before. By choosing a modern SIEM today, organizations are preparing for an AI SOC in the future without needing to stitch together separate tools.
SIEM vs. XDR
Extended detection and response (XDR) is a common alternative to a SIEM. It consolidates telemetry from endpoints, networks, email, and cloud workloads into a unified detection and response platform. It’s designed to work natively with a vendor’s endpoint, network, and cloud products, but that tight integration is also its limitation. XDR typically operates within a defined perimeter of supported sources, making it less effective in complex, multi-vendor or hybrid environments where data needs to be ingested from a wide range of disparate sources.
Modern SIEM, by contrast, is built for breadth. It ingests data from any source, regardless of vendor, normalizes it into a common schema, and applies correlation and analytics across the full environment. Where XDR gives you deep visibility within a defined ecosystem, SIEM gives you complete visibility across your entire organization.
SIEM adoption
More businesses are adopting SIEMs as they see the value in centralizing data and automating threat detection, investigation, and response through a single platform, and the market numbers reflect that.
Mordor Intelligence reports that the SIEM market is valued at $12.06B in 2026 and is projected to reach $20.78B by 2031, growing at an 11.50% CAGR (compound annual growth rate).
Cloud-native architectures are outpacing that at a 11.95% CAGR. They explain: “Mandatory log-retention rules, accelerated cloud migration, and increasingly sophisticated adversaries are converging, forcing organizations to modernize correlation engines and adopt analytics that can scale with exploding telemetry. AI-infused triage tools are improving analyst productivity by filtering low-valued alerts.”
While threat detection remains the dominant use case at 43.7% of the SIEM market in 2025, the fastest-growing segment reflects where organizations are headed, towards distributed, multi-cloud environments. Through 2031, cloud-workload monitoring is projected to grow at 12.63% CAGR to fill the visibility and scalability gap that traditional SIEMs weren’t built to handle.
The SIEM market will continue to expand as businesses embrace modern SIEM solutions that are cloud-native, AI-ready, and built to scale with the environments they protect.
Best practices for making the most of SIEM
Simply installing a SIEM does not mean your business is safe from threats. To get the most value, you need to set it up for your needs, manage it regularly, and keep your strategy up to date.
- Develop a clear strategy: What does success look like for your organization? Establish your goals, identify the data sources that matter most to your organization, and implement correlation rules tuned to your environment and threat profile. Out-of-the box configurations are designed to help you get started quickly, but they are not specific to your business.
- Continually fine-tune: Monitor ingestion rates, query performance, and detection coverage on a regular basis. Update detection rules, threat intelligence feeds, and AI models continuously.
- Automate intelligently: Configure automated alerting with AI-prioritization to reduce alert fatigue and surface high-priority threats. Regularly test incident response playbooks and, as AI agents take on more response tasks, ensure human oversight is built into the workflow.
- Stay ahead of compliance audits: Log collection, retention policies, and reporting are continuously aligned with requirements such as PCI DDS, HIPAA, and SOC2. Regular compliance audits help identify gaps before regulators do.
- Invest in your team and break down silos: Regularly train staff on the platform, emerging threats, and AI-powered attack techniques. Effective security extends beyond the SOC. Developers fix code vulnerabilities, and IT teams reduce risks by patching systems or isolating compromised accounts. SIEMs enable cross-collaboration by serving as a common platform for stakeholders. When integrated with monitoring tools or as one system, all teams will have a shared view of what’s happening across the environment.
Sumo Logic Cloud SIEM
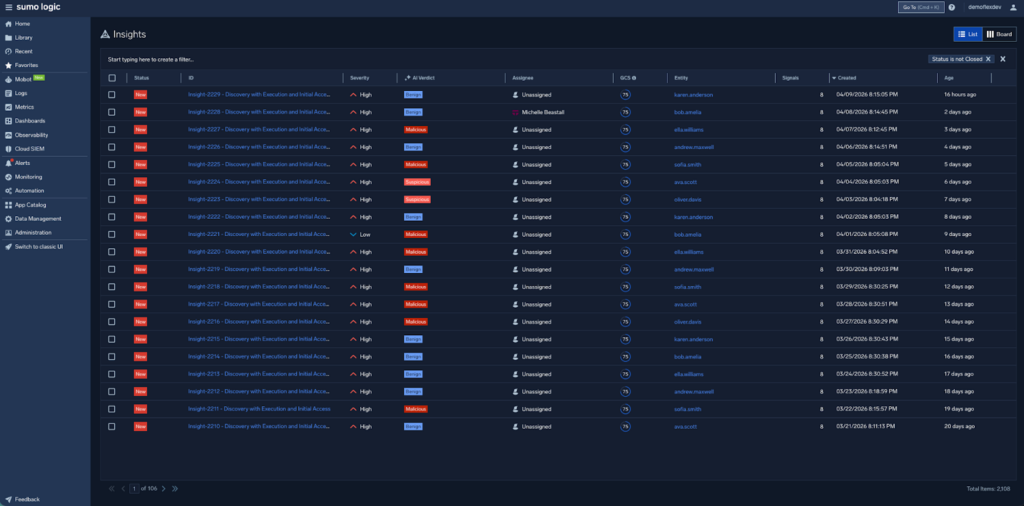
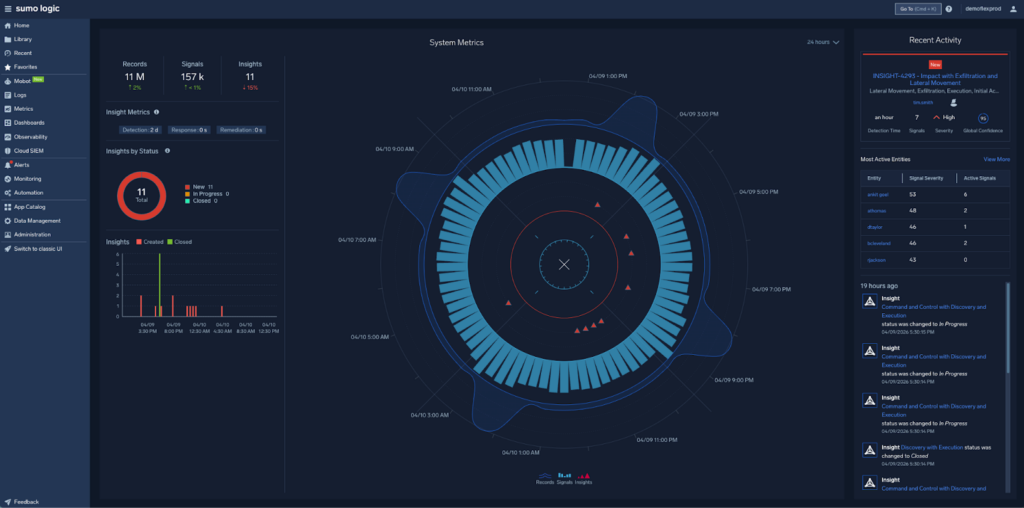
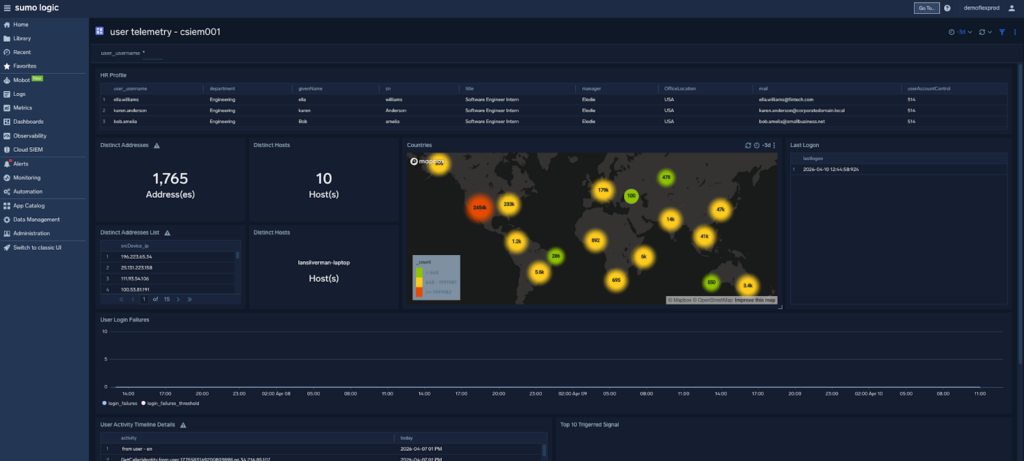
Sumo Logic Cloud SIEM is delivered from a modern SaaS platform that enables unified visibility across any type of environment – from on-prem and public clouds to hybrid and multi-cloud architectures. With built-in alert triaging and management, threat hunting capabilities, automated threat intelligence and collaboration features designed to make security a collective responsibility shared across the business, Sumo Logic Cloud SIEM helps businesses stay ahead of threats, no matter which types of IT resources they operate or where they deploy them.
Conclusion
The threat landscape will continue to grow in scale and complexity, but the technology built to defend against it is evolving quickly. Security teams have never had more powerful tools at their disposal. A modern SIEM sits at the center of it all, unifying data, accelerating detection, investigation, and response, while also creating an AI SOC-ready future where AI and human analysts work side by side to stay ahead of threats. Organizations that invest in that foundation today won’t just be better protected, they’ll be ready for whatever comes next.
See Sumo Logic Cloud SIEM in action. Get a demo.